In Part One of this series, I provided my definition of Major Cases and went into some detail about some of the attributes that differentiate a Case from a Major Case. Moving ahead now, I want to take a look at the different ‘types’ of Major Cases and an overview of major case management.
One of the problems in dealing with Major Cases is that, because of the varying types of cases, there’s no firm blueprint for investigating them. Major Cases move in real time, and – based upon interviews I have conducted with Major Case Investigators – can generally fall into one of two categories – Single Incidents and Multiple (serial) Incidents.
This article tackles Single Incident Major Cases.
Single incident Major Cases are defined by one single criminal act so abhorrent to the socio-economic environment, that it alone creates intense pressure to apprehend the perpetrator(s). What makes the incident so abhorrent ranges from factors such as:
The identity of the victim: In September of 1996, at the height of tensions between The Bloods and The Crips, a 25 year old African American man is shot in a drive-by shooting on the streets of Las Vegas and dies a few days later. Unfortunately, young black men die far too frequently in times of gang tensions, and few of these cases ever elevate to the status of a Major Case. The victim here, however, was Tupac Shakur.
 Tupac was an American rapper and actor who came to embody the 1990s gangsta-rap aesthetic, and was a key figure in the feud between West Coast and East Coast hip hop artists. Simply put… he was famous as hell. Hence, a far-too-routine shooting became a Major Case in the blink of an eye. The case remains unsolved.
Tupac was an American rapper and actor who came to embody the 1990s gangsta-rap aesthetic, and was a key figure in the feud between West Coast and East Coast hip hop artists. Simply put… he was famous as hell. Hence, a far-too-routine shooting became a Major Case in the blink of an eye. The case remains unsolved.
The identity of the suspect(s): “We the jury in the above entitled action find the defendant, Orenthal James Simpson, not guilty of the crime of murder.” Thus ended the double murder trial of former NFL player and Heisman Award winner OJ Simpson. In what was deemed ‘The Trial of the Century”, Simpson had been charged with the June 13, 1994 killings of his ex-wife Nicole Brown Simpson, and her friend Ron Goldman.
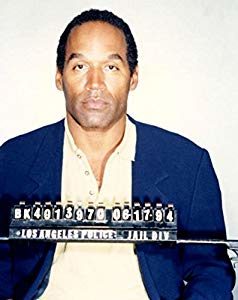 After weeks of testimony, and a clear nation-wide division between those who believed Simpson to be innocent and those who believed him guilty, Simpson was acquitted of the murders on October 3, 1995.
After weeks of testimony, and a clear nation-wide division between those who believed Simpson to be innocent and those who believed him guilty, Simpson was acquitted of the murders on October 3, 1995.
While the case of two relatively young and affluent Caucasians being killed in the generally safe area of Brentwood may have been newsworthy, it was the identity of the suspect that was the catalyst in this becoming one of the most famous single-incident Major Cases in American history.
The location of the crime: When a half-naked corpse, covered in cuts, bruises and bite marks, is found behind the Metropolitan Museum of Art in New York’s Central Park, you have the makings of a Major Case. The corpse was that of 18-year-old Jennifer Dawn Levin. Levin was murdered during the early morning hours of August 26, 1986.
 The ‘Met’, as the museum is known, is one of the most-visited and famous museums on the entire planet. Murders don’t happen in world-famous places like this, and the case became the top story on the evening news for months and months. That is one major single-incident Major Case.
The ‘Met’, as the museum is known, is one of the most-visited and famous museums on the entire planet. Murders don’t happen in world-famous places like this, and the case became the top story on the evening news for months and months. That is one major single-incident Major Case.
After an investigation into what the press dubbed “The Preppie Murder”, college student Robert Chambers was charged and tried for murder. The jury, however, remained deadlocked for nine days and a plea bargain was struck. (Chambers’ defense, you may recall, was that he had killed Ms. Levin during consensual ‘rough sex’.)
The uniqueness of the crime itself: Six year old girls in upscale Colorado neighborhoods aren’t supposed to die. They’re certainly not supposed to be murdered… especially in their own home while the rest of the family slept. Uniqueness has always surrounded the December, 1996 killing of young beauty queen JonBenét Ramsey in Boulder, CO.
 On the morning of December 26, 1996, John Ramsey found his daughter’s body with duct tape over her mouth and a cord twisted around her neck in the basement of the family home. John’s wife, Patsy, says she found a ransom note demanding $118,000 for JonBenét’s return – an amount that is purported to match exactly a recent work-related bonus that John Ramsey had received. Despite these odd circumstances, the couple retained lawyers and were not formally interviewed by police for over 4 months. (The case has never been solved, and Boulder Police have cleared the couple of any wrongdoing.)
On the morning of December 26, 1996, John Ramsey found his daughter’s body with duct tape over her mouth and a cord twisted around her neck in the basement of the family home. John’s wife, Patsy, says she found a ransom note demanding $118,000 for JonBenét’s return – an amount that is purported to match exactly a recent work-related bonus that John Ramsey had received. Despite these odd circumstances, the couple retained lawyers and were not formally interviewed by police for over 4 months. (The case has never been solved, and Boulder Police have cleared the couple of any wrongdoing.)
Tragically, it’s estimated that over 1500 children are murdered each year in America. JonBenét’s case may have been just another number in that truly sad statistic were it not for unique circumstances that surrounded it; it occurred in an upscale neighborhood, the victim was a young beauty queen, the ransom note matching the bonus, a possible crime scene contamination by father John, and ‘seemingly’ uncooperative parents that made this a single-incident Major Case.
In Part Three of this series, we examine some examples and problems associated with Multiple Incident Major Cases.
 Douglas Wood is CEO of Crime Technology Solutions | Case Closed Software, a leading provider of serious investigation software to law enforcement, state bureaus, DA offices, and other investigative units. Doug can be reached directly HERE.
Douglas Wood is CEO of Crime Technology Solutions | Case Closed Software, a leading provider of serious investigation software to law enforcement, state bureaus, DA offices, and other investigative units. Doug can be reached directly HERE.



 Crime Tech Solutions, who earlier this year acquired TN based
Crime Tech Solutions, who earlier this year acquired TN based 
 The topic of fraud is widely discussed, and the focus of thousands upon thousands of articles. Television shows such as
The topic of fraud is widely discussed, and the focus of thousands upon thousands of articles. Television shows such as 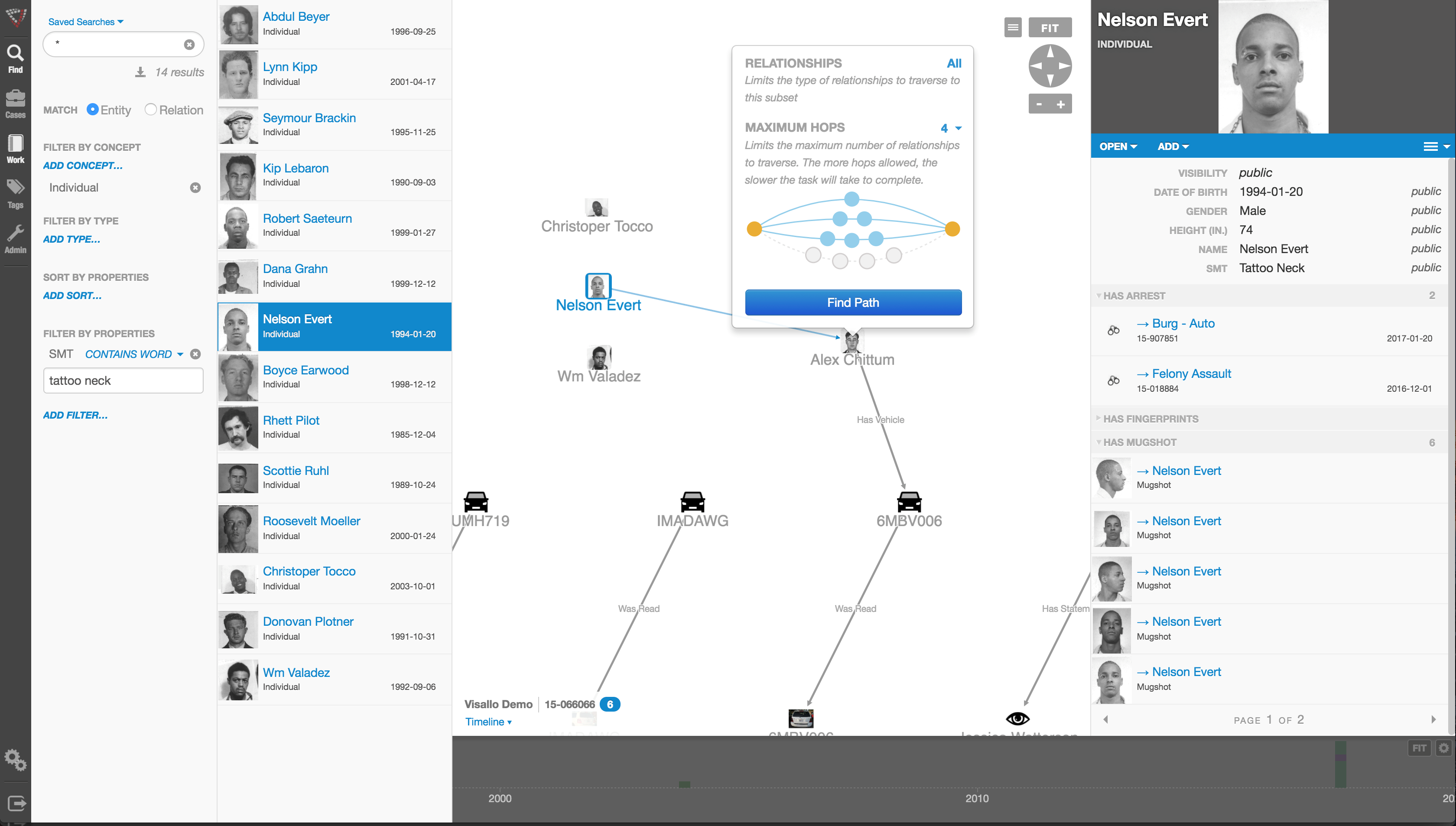
 Of course, big data in and by itself does nothing. It just sits there. Nobody has ever yelled “Help! We’ve been defrauded! Call the big data!” Big data is only useful when it can be transformed into ‘
Of course, big data in and by itself does nothing. It just sits there. Nobody has ever yelled “Help! We’ve been defrauded! Call the big data!” Big data is only useful when it can be transformed into ‘