Crime Tech Weekly proudly supports IACA and this material.
Monthly Archives: December 2015
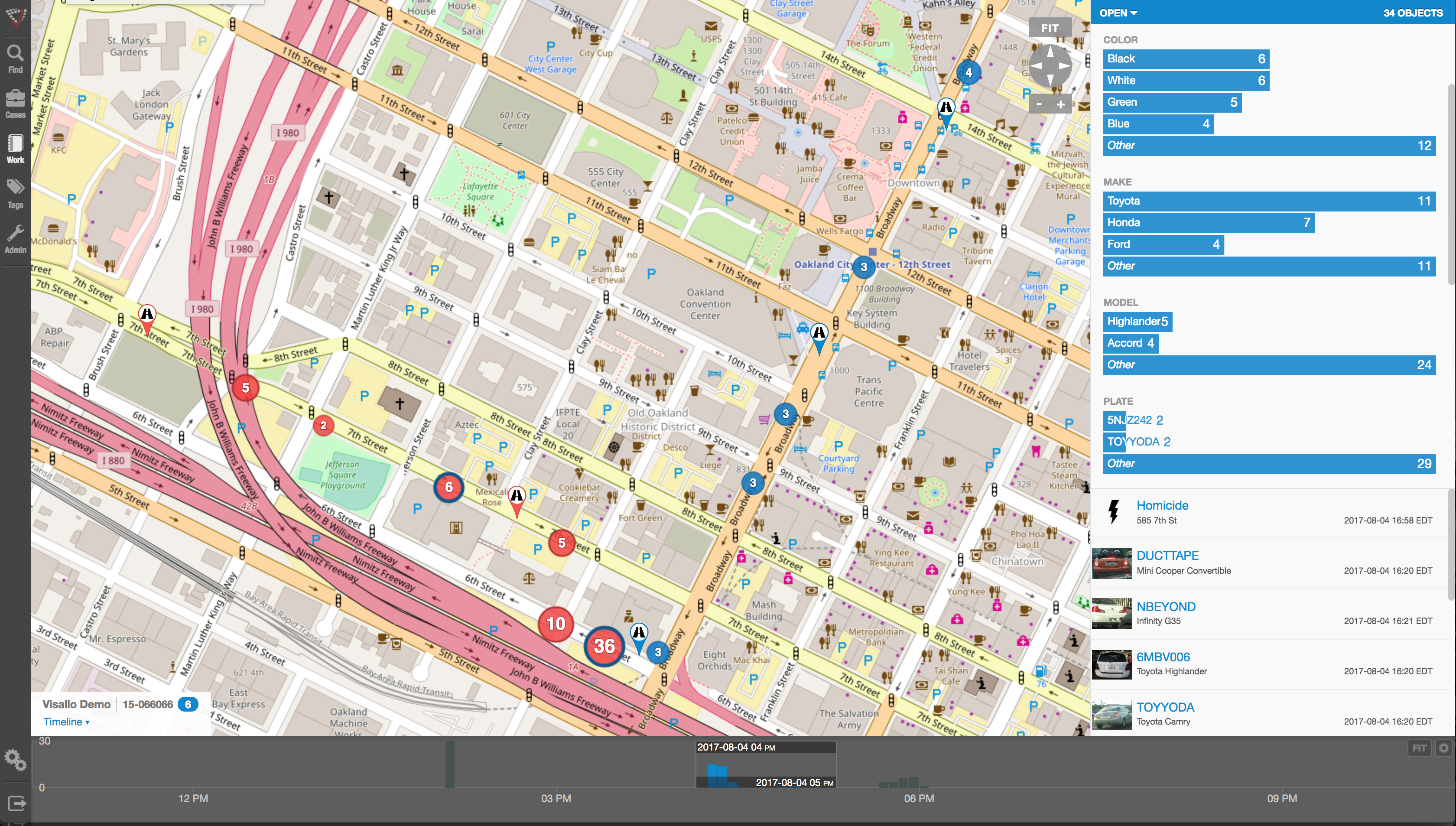
Best Practices – Geospatial Crime Mapping
Posted by Tyler Wood, Operations Manager at Crime Tech Solutions.

Crime mapping technology is a powerful and valuable tool for law enforcement. The ability to represent crime statistics visually – in a meaningful way – is helping police forces across America to analyze, understand, predict, and even prevent crime. It is, however, important to use caution when using such powerful tools, in order to prevent incorrect analyses of crime statistics that may hinder, rather than help, an investigation.
Specifically, there are a few key mistakes which should be avoided when utilizing this sort of predictive technology.
- Obviously, crime reporting should be thorough and detailed. Crime mapping technology takes a great many factors into consideration when developing a visual analysis of a certain area. The more detailed the input is, the more accurate the predictions and visualizations will be.
- Not every crime occurs at a specific street address. Certain crimes, like personal theft, may not be noticed until hours or even days after they occur, making it difficult to define an exact location at which the crime was committed. Analysts should take care to visualize each location in which it could have occurred.
- When developing a crime map of an area, analysts should take care to split the data between daytime and nighttime hours, as many areas have significantly different rates of crime depending on the time of day. If time is not taken into consideration, data can become skewed and law enforcement can develop a warped picture of the area.
- It is also important for analysts to consider other factors that affect crime reporting within a specific area. For example, petty crimes may be reported less often in lower-income neighborhoods. Care should be taken to consider the demographics and socioeconomic standings of the area being mapped in order to provide more context which can help analysts to more accurately predict and prevent crime.
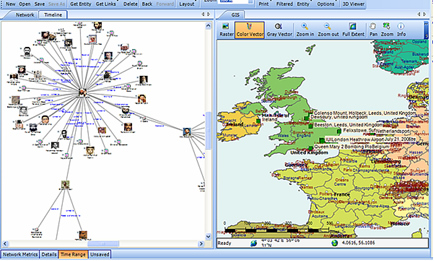 Combining, where possible, the functionality of link analysis into the crime mapping process brings powerful additional functionality. This ability to link, not only statistical, but entity-specific data is a potential game changer.
Combining, where possible, the functionality of link analysis into the crime mapping process brings powerful additional functionality. This ability to link, not only statistical, but entity-specific data is a potential game changer.
The role of crime mapping in the world of law enforcement is gaining popularity. Unfortunately, for many police departments, the cost of a full suite of software from category leader, ESRI is prohibitive. Still, there are options available… notably, CrimeMap Pro from Crime Tech Solutions.
___
(NOTE: Crime Tech Solutions is an Austin, TX based provider of crime and fraud analytics software for commercial and law enforcement groups. We proudly support the Association of Certified Fraud Examiners (ACFE), International Association of Chiefs of Police (IACP), Association of Law Enforcement Intelligence Units (LEIU) and International Association of Crime Analysts (IACA). Our offerings include sophisticated link analysis software, comprehensive crime mapping and predictive policing, and criminal intelligence database management systems.)
Link Analysis and Crime – An examination.
Posted by Tyler Wood, Operations Manager at Crime Tech Solutions
 The topic of fraud is widely discussed, and the focus of thousands upon thousands of articles. Television shows such as Crime, Inc and American Greed have become popular due, in part, to our fascination with the topic of fraud.
The topic of fraud is widely discussed, and the focus of thousands upon thousands of articles. Television shows such as Crime, Inc and American Greed have become popular due, in part, to our fascination with the topic of fraud.
The organizations that are affected by fraud are also fascinated… but for entirely different reasons. Some estimates suggest that the US economy loses 11 trillion dollars each year due to one form of fraud or another. It’s little wonder, therefore, that the companies most frequently defrauded have been heavily investing in anti-fraud technologies at an increasing rate over the past decade or more.
The biggest problem with fraud, of course, is that it is always evolving in a very Darwinian fashion. Like a living, breathing entity, fraud schemes change over time in order to survive. As the targets of fraud schemes put new policies, procedures and/or systems to deter the activities, the schemes modify and find new ways to survive.
So, since the nature of criminal activity is such that they constantly change, how do investigators find a fool proof methodology to ensure they are 100% safe from them? The answer, of course, is that they can’t. They never will; at least not until we live in a world such as the one depicted in the 2002 film Minority Report, starring Tom Cruise. In that movie, criminals are arrested prior to committing a crime based upon the predictions of psychics called ‘Precogs’. Corporations and individual targets of fraud can only wish.
Nope, there are no Precogs running around locking up would-be practitioners of fraud that would protect banks, insurance companies, Medicaid and Medicare programs, victims of Ponzi schemes, victims of identity theft, and countless others. Instead, organizations rely upon skilled knowledge workers using purpose-built crime and fraud analytics technology that can detect anomalies in patterns, suspicious transactions, hotspot mapping, networks of fraudsters, and other sophisticated data analytics tools.
Crime and fraud analytics
Any discussion of analytics and investigation software must touch upon the topic of ‘big data’. No longer just a buzz word, big data literally fuels the insights gathered by organizations in every area of business. Naturally, then, organizations who have been traditionally targeted by fraudsters have increasingly invested in crime technology such as investigation software and analytics in order to exploit the phenomenon.
 Of course, big data in and by itself does nothing. It just sits there. Nobody has ever yelled “Help! We’ve been defrauded! Call the big data!” Big data is only useful when it can be transformed into ‘smart data’. In other words, understanding the big picture of costly fraudulent activities is not akin to understanding the specifics of ‘who’ is defrauding you, and ‘how’ they are doing it.
Of course, big data in and by itself does nothing. It just sits there. Nobody has ever yelled “Help! We’ve been defrauded! Call the big data!” Big data is only useful when it can be transformed into ‘smart data’. In other words, understanding the big picture of costly fraudulent activities is not akin to understanding the specifics of ‘who’ is defrauding you, and ‘how’ they are doing it.
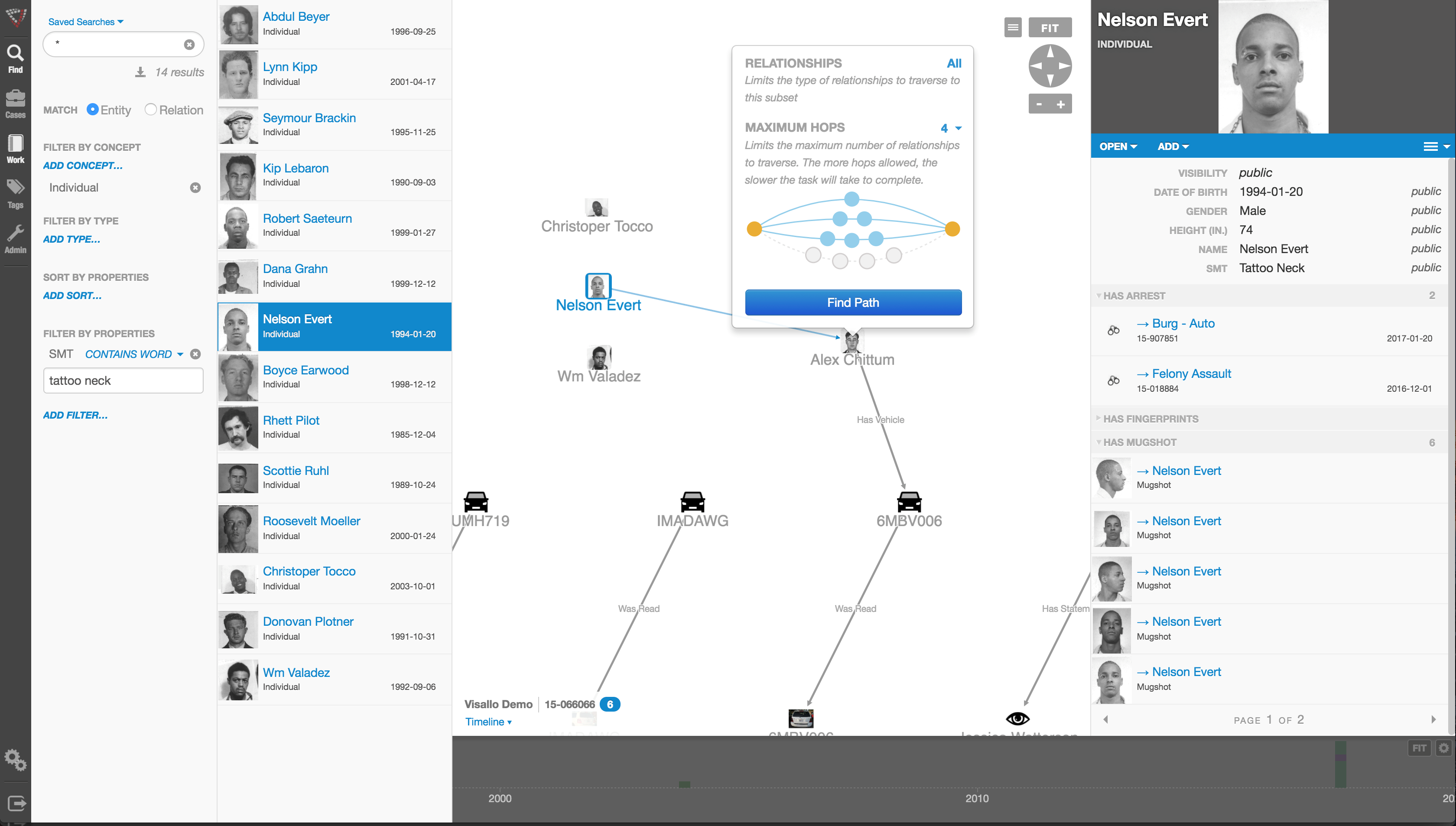
Those questions can best be answered through the powerful data mining and link analysis software tools offered by Austin, TX based Crime Tech Solutions in partnership with Sterling, VA based Visallo. Effective link analysis complements big data analytics platforms, helping to expose previously undetected fraud, and the entities (people or organizations) committing it.
Link Analysis – Transforming big data into smart data
By definition, link analysis is a data analysis technique that examines relationships among people, places, and things. As a visual tool, link analysis provides users a powerful method to quickly understand and ‘see’ what is happening. Because of this, it is widely used by financial institutions such as banks and insurance companies to uncover criminal networks, improve fraud investigations, detect insider fraud, and expose money laundering schemes. Similarly, government agencies use link analysis to investigate fraud, enhance screening processes, uncover terrorist networks and investigate criminal activities.
At Crime Tech Solutions, we liken the question of how to detect and deter fraud to ‘How do you eat an elephant?’ The answer, of course, is one bite at a time. If big data is the elephant, comprehensive link analysis software is part of the one ‘bite’ at a time. Or should we say ‘byte’.
(NOTE: Crime Tech Solutions is an Austin, TX based provider of investigation software and analytics for commercial and law enforcement groups. We proudly support the Association of Certified Fraud Examiners (ACFE), International Association of Chiefs of Police (IACP), Association of Law Enforcement Intelligence Units (LEIU) and International Association of Crime Analysts (IACA). Our offerings include sophisticated link analysis software, an industry-leading investigation case management solution, and criminal intelligence database management systems.)
What is Crime Analysis?
Posted by Tyler Wood Crime Tech Solutions, your source for investigation software.
The information provided on this page comes primarily from Boba, R. (2008: Pages 3 through 6) Crime Analysis with Crime Mapping. For a full discussion of the crime analysis discipline, refer to the book which can be obtained through www.sagepub.com.
Over the past 20 years, many scholars have developed definitions of crime analysis. Although definitions of crime analysis differ in specifics, they share several common components: all agree that crime analysis supports the mission of the police agency, utilizes systematic methods and information, and provides information to a range of audiences. Thus, the following definition of crime analysis is used as the foundation of this initiative:
Crime analysis is the systematic study of crime and disorder problems as well as other police–related issues—including sociodemographic, spatial, and temporal factors—to assist the police in criminal apprehension, crime and disorder reduction, crime prevention, and evaluation.
Clarification of each aspect of this definition helps to demonstrate the various elements of crime analysis. Generally, to study means to inquire into, investigate, examine closely, and/or scrutinize information. Crime analysis, then, is the focused and systematic examination of crime and disorder problems as well as other police-related issues. Crime analysis is not haphazard or anecdotal; rather, it involves the application of social science data collection procedures, analytical methods, and statistical techniques.
More specifically, crime analysis employs both qualitative and quantitative data and methods. Crime analysts use qualitative data and methods when they examine non-numerical data for the purpose of discovering underlying meanings and patterns of relationships. The qualitative methods specific to crime analysis include field research (such as observing characteristics of locations) and content analysis (such as examining police report narratives). Crime analysts use quantitative data and methods when they conduct statistical analysis of numerical or categorical data. Although much of the work in crime analysis is quantitative, crime analysts use simple statistical methods, such as frequencies, percentages, means, and rates. Typical crime analysis tools include link analysis and crime mapping software.
The central focus of crime analysis is the study of crime (e.g., rape, robbery, and burglary); disorder problems (e.g., noise complaints, burglar alarms, and suspicious activity); and information related to the nature of incidents, offenders, and victims or targets of crime (targets refer to inanimate objects, such as buildings or property). Crime analysts also study other police-related operational issues, such as staffing needs and areas of police service. Even though this discipline is called crime analysis, it actually includes much more than just the examination of crime incidents.
Although many different characteristics of crime and disorder are relevant in crime analysis, the three most important kinds of information that crime analysts use are sociodemographic, spatial, and temporal. Sociodemographic information consists of the personal characteristics of individuals and groups, such as sex, race, income, age, and education. On an individual level, crime analysts use sociodemographic information to search for and identify crime suspects. On a broader level, they use such information to determine the characteristics of groups and how they relate to crime. For example, analysts may use sociodemographic information to answer the question, “Is there a white, male suspect, 30 to 35 years of age, with brown hair and brown eyes, to link to a particular robbery?” or “Can demographic characteristics explain why the people in one group are victimized more often than people in another group in a particular area?”
The spatial nature of crime and other police-related issues is central to understanding the nature of a problem. In recent years, improvements in computer technology and the availability of electronic data have facilitated a larger role for spatial analysis in crime analysis. Visual displays of crime locations (maps) and their relationship to other events and geographic features are essential to understanding the nature of crime and disorder. Recent developments in criminological theory have encouraged crime analysts to focus on geographic patterns of crime, by examining situations in which victims and offenders come together in time and space.
Finally, the temporal nature of crime, disorder, and other police-related issues is a major component of crime analysis. Crime analysts conduct several levels of temporal analysis, including (a) examination of long-term patterns in crime trends over several years, the seasonal nature of crime, and patterns by month; (b) examination of mid-length patterns, such as patterns by day of week and time of day; and (c) examination of short-term patterns, such as patterns by day of the week, time of day, or time between incidents within a particular crime series.
The final part of the crime analysis definition—”to assist the police in criminal apprehension, crime and disorder reduction, crime prevention, and evaluation” generally summarizes the purpose and goals of crime analysis. The primary purpose of crime analysis is to support (i.e., “assist”) the operations of a police department. Without police, crime analysis would not exist as it is defined here.
The first goal of crime analysis is to assist in criminal apprehension, given that this is a fundamental goal of the police. For instance, a detective may be investigating a robbery incident in which the perpetrator used a particular modus operandi (i.e., method of the crime). A crime analyst might assist the detective by searching a database of previous robberies for similar cases.
Another fundamental police goal is to prevent crime through methods other than apprehension. Thus, the second goal of crime analysis is to help identify and analyze crime and disorder problems as well as to develop crime prevention responses for those problems. For example, members of a police department may wish to conduct a residential burglary prevention campaign and would like to target their resources in areas with the largest residential burglary problem. A crime analyst can assist by conducting an analysis of residential burglary to examine how, when, and where the burglaries occurred along with which items were stolen. The analyst can then use this information to develop crime prevention suggestions, (such as closing and locking garage doors) for specific areas.
Many of the problems that police deal with or are asked to solve are not criminal in nature; rather, they are related to quality of life and disorder. Some examples include false burglar alarms, loud noise complaints, traffic control, and neighbor disputes. The third goal of crime analysis stems from the police objective to reduce crime and disorder. Crime analysts can assist police with these efforts by researching and analyzing problems such as suspicious activity, noise complaints, code violations, and trespass warnings. This research can provide officers with information they can use to address these issues before they become more serious criminal problems.
The final goal of crime analysis is to help with the evaluation of police efforts by determining the level of success of programs and initiatives implemented to control and prevent crime and disorder and measuring how effectively police organizations are run. In recent years, local police agencies have become increasingly interested in determining the effectiveness of their crime control and prevention programs and initiatives. For example, an evaluation might be conducted to determine the effectiveness of a two-month burglary surveillance or of a crime prevention program that has sought to implement crime prevention through environmental design (CPTED) principles within several apartment communities. Crime analysts also assist police departments in evaluating internal organizational procedures, such as resource allocation (i.e., how officers are assigned to patrol areas), realignment of geographic boundaries, the forecasting of staffing needs, and the development of performance measures. Police agencies keep such procedures under constant scrutiny in order to ensure that the agencies are running effectively.
In summary, the primary objective of crime analysis is to assist the police in reducing and preventing crime and disorder. Present cutting edge policing strategies, such as hotspots policing, problem-oriented policing, disorder policing, intelligence-led policing, and CompStat management strategies, are centered on directing crime prevention and crime reduction responses based on crime analysis results. Although crime analysis is recognized today as important by both the policing and the academic communities, it is a young discipline and is still being developed. Consequently, it is necessary to provide new and experienced crime analysts with training and assistance that improves their skills and provides them examples of best practices from around the country and the world. http://crimetechsolutions.com
Insurance Fraud and Terrorist Financing – A bloody mix.
Published by Tyler Wood, Operations Manager at Crime Tech Solutions
December 7, 2015 – Nice post on LinkedIn today written by Aaron Denbo, Lead Trainer at Frauducate Counter-Fraud Academy…

The game has changed. Insurance Fraud isn’t the “quiet fraud” committed by otherwise “normal” people fudging a bit on their past driving experience, prior injuries, work status, or income. It is an $80 BILLION dollar a year problem and it funds and fuels organized crime rings, drug cartels, and terrorism. In a recent article by Christopher Tidball at PropertyCasualty360, “We’re seeing organized trans-national crime rings that are using insurance fraud as a vehicle to fund illegal activities.”
$80 BILLION is a lot of money. That’s a lot of well-funded death and destruction that can be bought and that’s just from the Insurance Fraud front.
That $80 BILLION also includes terrorism, which is more poignant than ever in the wake of both the Paris and the San Bernardino, California terrorist attacks. Combating insurance fraud – and fraud in general — has never been more important.
Now those of us who are counter-fraud professionals and have completed training in identifying, detecting, and investigating fraud and work fraud cases know that what we do is important. Your friends and family probably have a general understanding of what you do but have you connected your work to combating organized crime or terrorism? Have you thought of your work as part of a bigger piece that just might combat the next wave of terrorism? Have you thought of your fraud fighting in terms of making it so that some bad people with bad intentions might just not be able to make that extra explosive device because you disrupted their funding?
After San Bernardino, after Paris, after …. [insert next terror attack here]maybe we should think of ourselves not just as fraud fighters but also as disrupters and agitators to terror groups and organized crime rings. It is a change in awareness and mentality that I’m advocating here, an expansive sense of purpose. Terrorism Finance is more than just working Anti-Money Laundering cases now or leaving that to a problem that the banking sector has to face. It means our insurance fraud investigations are more than just money for our companies or agencies. It means we’re playing for keeps now.
__
Crime Tech Solutions delivers powerful link and social network analysis software to insurance companies to find hidden and suspicious connections between people, places, and things.
Uncovering Fraud means Uncovering Non-Obvious Relationships
Posted by Tyler Wood, Operations Manager at Crime Tech Solutions
Although no fraud prevention measures are ever 100% foolproof, significant progress can be achieved by looking beyond the individual data points to the relationships between them. This is the science of link analysis.
Looking at data relationships isn’t straightforward and doesn’t necessarily mean gathering new or more data. The key to battling financial crimes it is to look at the existing data in a new way – namely, in a way that makes underlying connections and patterns using powerful but proven tools such as the Sentinel Visualizer software offered by Crime Tech Solutions.
Unlike most other ways of looking at data, link analysis charts are designed to exploit relationships in data. That means they can uncover patterns difficult to detect using traditional representations such as tables.
Now, we all know that there are various types of fraud – first-party, insurance, and e-commerce fraud, for instance. What they all have in common is the layers of dishonesty to hide the crime. In each of these types of fraud, link analysis from Crime Tech Solutions offers a significant opportunity to augment existing methods of fraud detection, making evasion substantially more difficult.
Let’s take a look at first-party fraud. This type of fraud involves criminals who apply for loans or credit cards but who have no intention of ever paying the money back. It’s a serious problem for banks, who lose tens of billions of dollars every year to this form of fraud. It’s hard to detect and the fraudsters are good at impersonating good customers until the moment they do their ‘Bust-Out,’ i.e. cleaning out all their accounts and disappearing.
Another factor is the nature of the relationships between the participants in the fraud ring. While these characteristics make these schemes very damaging, it also renders them especially vulnerable to link analysis methods of fraud detection.
That’s because a first-party fraud ring involves a group of people sharing a subset of legitimate contact information and bogus information, and then combining them to create a number of synthetic identities. With these fake identities, fraudsters open new accounts for new forms of loans.
The fraudsters’ accounts are used in a normal manner with regular purchases and timely payments so that the banks gain confidence and slowly increase credit over time. Then, one day… Poof! The credit cards are maxed out and everyone has disappeared. The fraudsters are long gone and ready to hit the next bank down the road.
Gartner Group believes in a layered model for fraud prevention that starts with simple discrete methods but progresses to more elaborate types of analysis. The final layer, Layer 5, is called “Entity Link Analysis” and is designed to leverage connections in data in order to detect organized fraud.
In other words, Gartner believes that running appropriate entity link analysis queries can help organizations identify probable fraud rings during or even before the fraud occurs.