A new solution for big data policing is answering the question “Can my agency afford big data policing?“. Strategic partners Visallo™ and Case Closed Software™ have built an affordable alternative to the types of solutions sold by Palantir Technologies™, IBM, and other massive tech companies.
The Visallo | Case Closed offering is the only affordable alternative for law enforcement agencies who know that the practice of crime analysis and criminal investigations management can be much worse than looking for a needle in a haystack. It’s actually pieces of needles hidden across many haystacks.
Finding those pieces and putting them together requires a metal detector and soldering gun. Visallo is the metal detector. Case Closed Software is the soldering iron.
Download our Pieces of Needles and Many Haystacks synopsis now, and contact us through the form below for more information:
[contact-form][contact-field label=”Name” type=”name” required=”1″ /][contact-field label=”Email” type=”email” required=”1″ /][contact-field label=”Website” type=”url” /][contact-field label=”Comment” type=”textarea” required=”1″ /][/contact-form]
Tag Archives: ialeia
Investigative Link Analysis: Consider the Source
Posted by Tyler Wood, Operations Manager at Case Closed Software and Crime Tech Solutions
Investigative link analysis and visualization software is a powerful tool for both law enforcement agencies and the private sector investigators alike. It allows investigators to visualize the hidden, non-obvious connections that would likely otherwise go undetected. After all, we know that the human brain is much more easily able to make connections when information is presented via images rather than text.
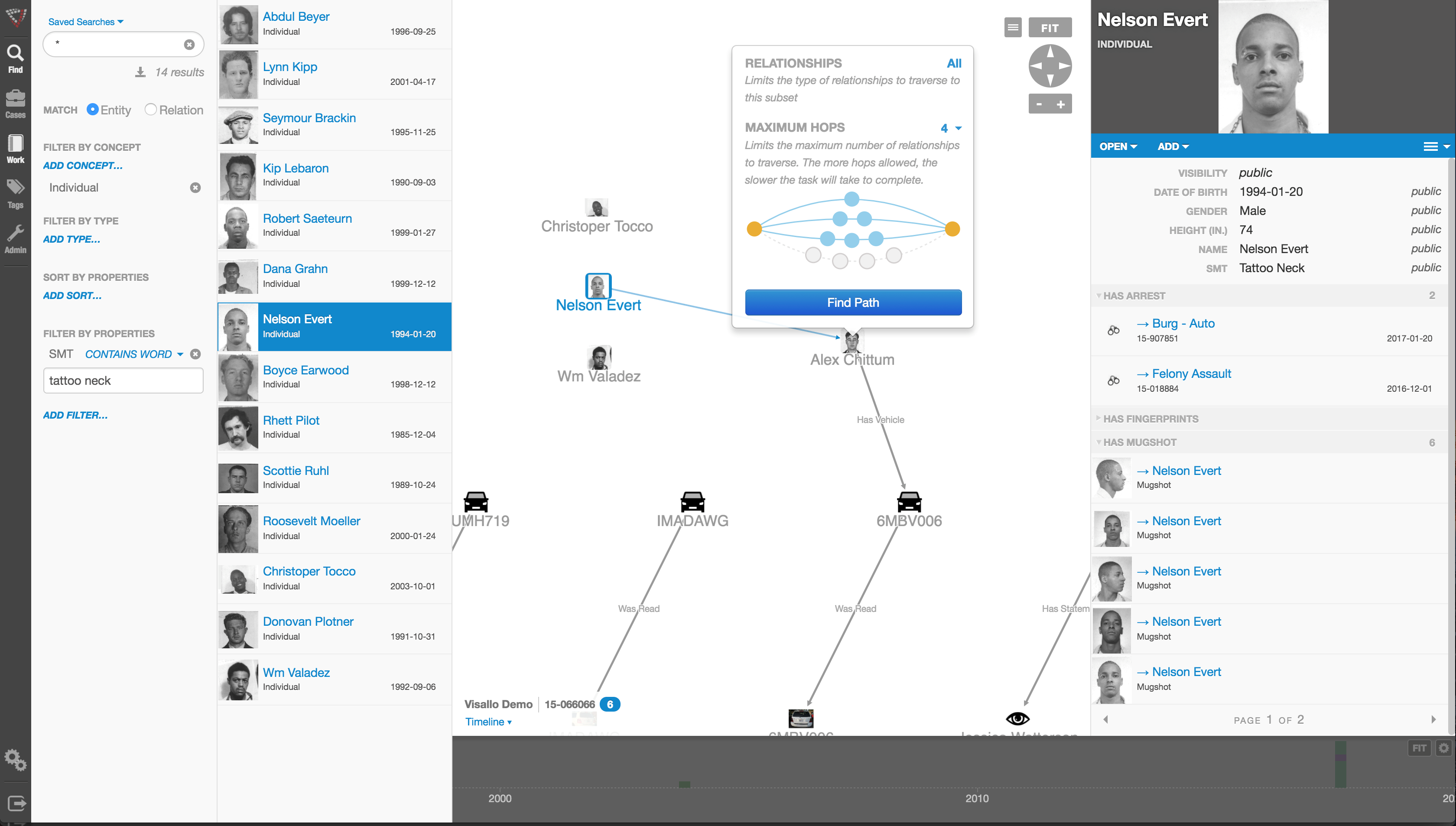
The software does, however, need a human to tell it what to look for, and where to look for it. Information is visualized in link analysis software by importing or querying a set of data, and then organizing that data according to parameters set by an investigator. The investigator is responsible for telling the software how to organize the data, and where to gather it from.
A smart investigator will utilize multiple sources when visualizing software. The majority of the time, not all the information needed for an investigation will come from the same source.
Law Enforcement investigators may need to pull RMS data, cell phone records, case management records, and even third party data, etc, to fully understand the big picture in a scenario. By using link analysis to cross-reference these data clusters against each other, the investigator is able to see even more connections, and find even more relevant data that may be crucial in solving a case.
It is important for investigators to exhaust all their resources so they can paint the clearest picture possible. This marriage of intuition and technology ensures that no connections stay hidden from investigation.
The key, as in all of life, is considering the source.
Contact us for more information about how powerful investigation big data link analysis can help your agency today.
[contact-form][contact-field label=”Name” type=”name” required=”1″ /][contact-field label=”Email” type=”email” required=”1″ /][contact-field label=”Website” type=”url” /][contact-field label=”Comment” type=”textarea” required=”1″ /][/contact-form]
Must Read: The Rise of Big Data Policing
 Here’s an excellent, must-read article from Andrew Guthrie Ferguson, a Professor of Law at the UDC David A. Clarke School of Law and author of the book The Rise of Big Data Policing: Surveillance, Race, and the Future of Law Enforcement (NYU Press 2017).
Here’s an excellent, must-read article from Andrew Guthrie Ferguson, a Professor of Law at the UDC David A. Clarke School of Law and author of the book The Rise of Big Data Policing: Surveillance, Race, and the Future of Law Enforcement (NYU Press 2017).
“The big data policing revolution has arrived. The singular insight of this innovation is that data-driven predictive technologies can identify and forecast risk for the future. Risk identification is also the goal of this book — to forecast the potential problems of big data policing as it reshapes law enforcement.”
Read the full article HERE.
In the meantime,  Case Closed Software™ reminds you that, as the only true alternative to Palantir®, we specialize in big data investigation analytics combined with the industry’s most robust investigative case management solution.
Case Closed Software™ reminds you that, as the only true alternative to Palantir®, we specialize in big data investigation analytics combined with the industry’s most robust investigative case management solution.
We are “Palantir® without the price tag and data-lock”.
Contact us for more information below:
[contact-form][contact-field label=”Name” type=”name” required=”1″ /][contact-field label=”Email” type=”email” required=”1″ /][contact-field label=”Website” type=”url” /][contact-field label=”Comment” type=”textarea” required=”1″ /][/contact-form]
Data Analytics Transforms Policing
 Great article from our friends at Visallo!
Great article from our friends at Visallo!
As police find new methods of tracking and solving crime, their needs and priorities in a data analytics strategy are bound to continuously evolve.
Be sure to read the article at the popular Visallo Blog, and for more information on how Visallo and Crime Tech Solutions are changing the investigation analytics world, contact us with the form below.
[contact-form][contact-field label=”Name” type=”name” required=”1″ /][contact-field label=”Email” type=”email” required=”1″ /][contact-field label=”Website” type=”url” /][contact-field label=”Comment” type=”textarea” required=”1″ /][/contact-form]
Visallo and Crime Tech Solutions: Partners in Crime-Fighting Software
Sterling, VA (August 24, 2017) – Visallo, the Sterling, VA based provider of investigation analytics software, and only true competitor to Silicon Valley giant Palantir, today announced a strategic partnership with Crime Tech Solutions out of Leander, TX.
 According to Jeff Kunkle, President of Visallo, the partnership enhances his company’s suite of easy-to-use, web-based data visualization tools for investigative link analysis, data discovery, crime analytics and geospatial analysis with Crime Tech Solutions’ powerful and flexible Case Closed investigation case management software.
According to Jeff Kunkle, President of Visallo, the partnership enhances his company’s suite of easy-to-use, web-based data visualization tools for investigative link analysis, data discovery, crime analytics and geospatial analysis with Crime Tech Solutions’ powerful and flexible Case Closed investigation case management software.
“Visallo is designed for intelligence analysts, law enforcement investigators, and fraud analysts who need easy to use tools to help them discover and visualize complex relationships within vast amounts of data without resorting to time-consuming, ad-hoc, and error-prone manual processes,” said Mr. Kunkle. “These are analysts that want to make sure they don’t miss important non-obvious insights during their investigations, want to produce more accurate, thorough, and defensible conclusions, and ultimately seek to be more accomplished investigators able to tackle the toughest cases.”
Tyler Wood, VP of Operations at Crime Tech Solutions added, “Where Visallo does much of the big data analytics, the Case Closed software is specifically designed for investigative process and major case management. The software manages the entire investigation workflow from start to finish and includes functionality such as task management, alerting, communications, evidence management, and a great deal more.”
Until now, investigative agencies had to turn to multi-million dollar solutions from behemoth multinational companies for this combined functionality. The partnership is designed to give customers more investigation functionality at a price point that can scale down to smaller groups. “For years, only the largest law enforcement and federal agencies could afford to purchase these types of advanced tools,” added Mr. Kunkle. “The partnership between Visallo and Crime Tech Solutions changes that reality.”
The companies have indicated that integration efforts are already underway to ensure a seamless and user-friendly experience.
About Visallo
Visallo helps investigators of all types produce more accurate, thorough, and timely analysis with a software platform to help them discover, visualize, and understand complex relationships hidden in massive amounts of data. Visallo’s all-in-one suite of easy-to-use, web-based, visualization tools and machine learning data analysis algorithms augment the investigator’s hard-earned experience and intuition with data-driven insights that would be difficult, if not impossible, to discover otherwise.
About Crime Tech Solutions
Crime Tech Solutions develops and markets a robust suite of powerful software solutions designed for intelligence and investigation teams. Their flagship products include the popular Case Closed™ investigation platform and IntelNexus™, an advanced criminal intelligence management software.
Save a tree… Go digital for investigation case management!

 Posted by Tyler Wood, Director of Operations at Case Closed Software.
Posted by Tyler Wood, Director of Operations at Case Closed Software.
Investigation Case Management (ICM) and Major Case Management (MCM) for law enforcement have always required a great deal of effort. Keeping track of every lead, every record, every relevant piece of information always takes time and manpower. Especially if the agency is stuck using paper-based files, cluttered file cabinets, and disorganized evidence rooms.
Modern case management technology allows the complex task of filing and organizing to be done in a simple piece of software, allowing the job to be done more quickly and with less risk of error. Unfortunately, many law enforcement agencies today are still using the traditional method of case management, even though a software approach has several distinct advantages:
Simplicity. Managing all the relevant paperwork and information for criminal investigations is labor intensive and susceptible to human error. A person must file all documentation such as witness reports, suspect information, crime scene reports, etc… into a file cabinet to be retrieved manually when needed. This creates a likelihood that something will eventually be placed in the wrong folder and an investigation could be weakened or compromised. A powerful case management software, however, will store all this data electronically on a central database. Data is able to be searched for and retrieved instantaneously by any authorized investigator. This streamlines the investigation process and makes document filing safer and less prone to error.
Cross-referencing. Paper copies of data, obviously, cannot be automatically searched through. If evidence from Investigation A happens to also be relevant to Investigation B, then with a traditional filing system and investigator would have to recall that information from memory then physically search through the files in order to find the relevant data. An electronic system will come with a powerful search function and the ability to cross reference against other investigation files with the click of a button. This allows law enforcement to more quickly gather relevant data.
In addition, law enforcement can also instantly share data between agencies. The sharing of data across agencies makes law enforcement across the nation more effective. Cross-referencing is a very important feature to have, especially when dealing with gangs and other organized crime in which evidence may be spread out among several related suspects.

Control. Using a secure electronic case management system, a supervisor can know exactly who accessed which data at what time. They can limit access to certain investigators in order to keep prying eyes out of the files. These features let supervisors rest easy knowing that their case files are kept digitally under their control.
Law enforcement agencies in the 21st century cannot afford to live in the past as far as case management goes. The convenience, simplicity, powerful features, and security of an electronic case management system is invaluable to investigators across the globe. In a world where criminals are becoming increasingly reliant on cutting edge technology, law enforcement must also make use of technology to make sure they are combating crime as effectively as possible. The case is closed on that discussion.
For information on our feature-rich and affordable ICM and MCM technologies, please visit Case Closed Software.
Criminal Intelligence Databases: Violations of privacy rights are the exception, not the rule.
 The notion that law enforcement fusion centers regularly violate individuals’ privacy rights as they capture intelligence on gangs, terrorist activities, organized crime, and other threats to public safety is simply not true. That, according to a study published in the Journal of Police and Criminal Psychology.
The notion that law enforcement fusion centers regularly violate individuals’ privacy rights as they capture intelligence on gangs, terrorist activities, organized crime, and other threats to public safety is simply not true. That, according to a study published in the Journal of Police and Criminal Psychology.The paper, “Law Enforcement Fusion Centers: Cultivating an Information Sharing Environment while Safeguarding Privacy,” was authored by Jeremy Carter, an assistant professor of Public and Environmental Affairs at Indiana University-Purdue University Indianapolis. His article carefully addresses the privacy-rights issue of criminal intelligence gathering, among others.
 There are approximately 80 fusion centers in the United States. They were created in response to the 9/11 terrorist attacks. The attacks exposed the requirement for greater information sharing and improved intelligence capabilities at all law enforcement levels. According to the article’s author, the idea was to have the key pieces of data funneled into fusion centers so that highly trained analysts could stay atop of threats and correspond with local law enforcement agencies on these potential threats.
There are approximately 80 fusion centers in the United States. They were created in response to the 9/11 terrorist attacks. The attacks exposed the requirement for greater information sharing and improved intelligence capabilities at all law enforcement levels. According to the article’s author, the idea was to have the key pieces of data funneled into fusion centers so that highly trained analysts could stay atop of threats and correspond with local law enforcement agencies on these potential threats.Designed with a view to enhance information-sharing among agencies, fusion centers act as ‘hubs’ of data and intelligence on gang activities, terrorist cells, organized crime, and other public safety threats. Vast amounts have data has been collected, and concerns about individual privacy and civil rights have ensued. The very legitimacy of these fusion centers has been called into question.
 The notion that law enforcement fusion centers represent ‘Big Brother’, and that data is being stored and disseminated about people irrespective of whether they are suspected of criminal activity is simply wrong, according to Professor Carter.
The notion that law enforcement fusion centers represent ‘Big Brother’, and that data is being stored and disseminated about people irrespective of whether they are suspected of criminal activity is simply wrong, according to Professor Carter.Still, concerns remain about who can access the data, and for what purpose. However, a survey of fusion centers across the country suggests that they take appropriate steps to safeguard individual privacy via something called Federal Regulatory Code CFR 28 Part 23.
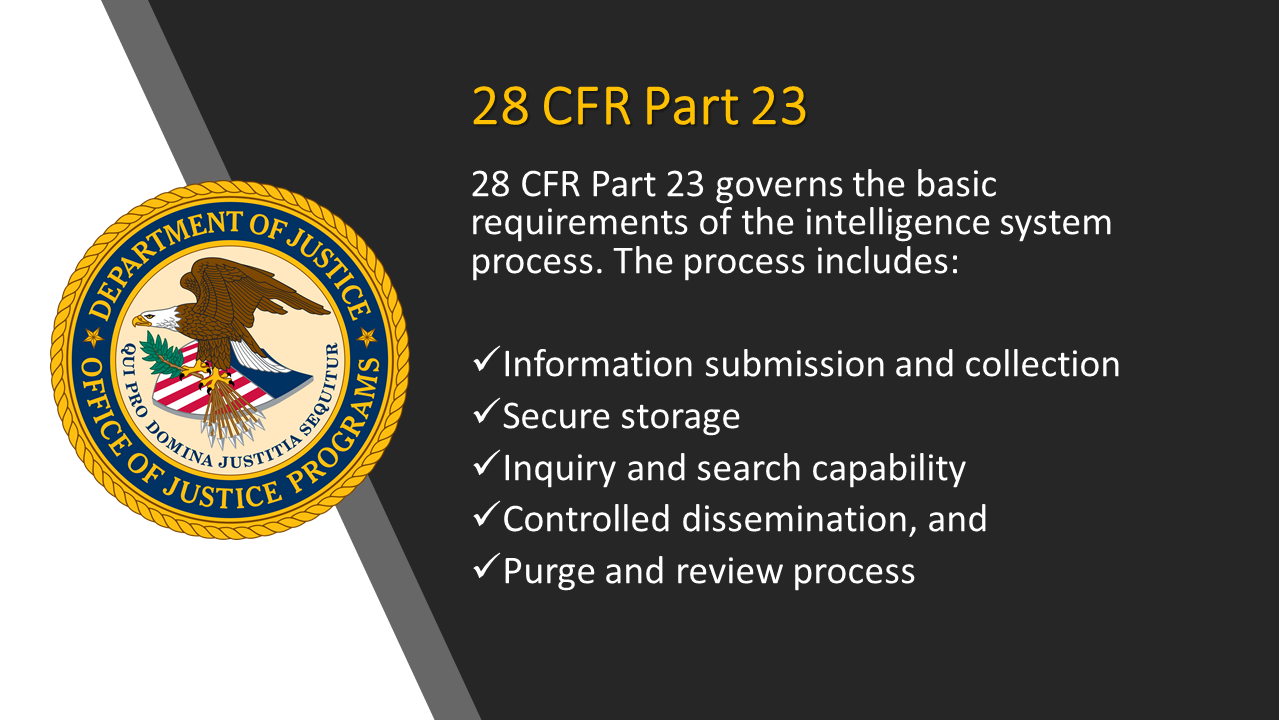 “Fusion centers are following the federal regulatory code, 28 CFR Part 23, that is the legal standard for collecting information,” Carter said. “That code says you have to establish a criminal predicate, basically probable cause, to keep information on identifiable individuals.”
“Fusion centers are following the federal regulatory code, 28 CFR Part 23, that is the legal standard for collecting information,” Carter said. “That code says you have to establish a criminal predicate, basically probable cause, to keep information on identifiable individuals.”Additionally, the majority of the fusion centers have implemented strong controls that provide built-in safeguards that protect the privacy of individuals. The fusion centers are also regularly audited to ensure that only the correct type of data is gathered, and that is stored and disseminated in a need-to-know basis.
 Crime Tech Solutions develops and markets a suite of crime fighting software including IntelNexus™, a criminal intelligence database system that complies with the above mentioned code 28 CFR Part 23. The company also provides software for investigation case management, advanced crime analytics, and link/social network analysis.
Crime Tech Solutions develops and markets a suite of crime fighting software including IntelNexus™, a criminal intelligence database system that complies with the above mentioned code 28 CFR Part 23. The company also provides software for investigation case management, advanced crime analytics, and link/social network analysis.
Hunting for D.B. Cooper – A study in analytics.
The following article originally appeared at In Public Safety, and is a highly recommended read. It was written by Erik Kleinsmith at American Military University.
Crime Tech Weekly is posting the article in its entirety for our readers’ convenience…
By Erik Kleinsmith
Staff, Intelligence Studies, American Military University
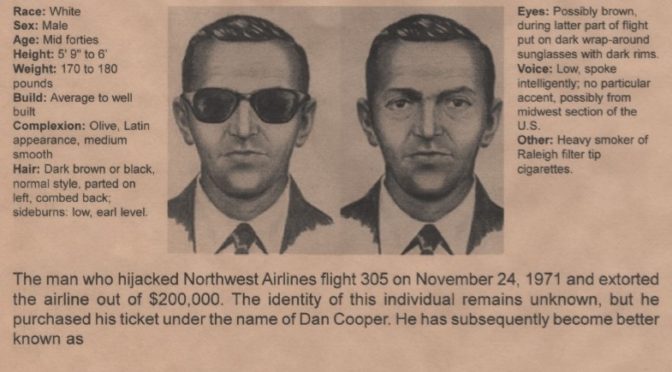
On November 24, 1971, a man using the name Dan Cooper purchased a $35 one-way airline ticket from Portland, Oregon, to Seattle, Washington. Not long after takeoff, he hijacked Northwest Orient Flight 305 and demanded $200,000 in cash along with two parachutes, which he received upon landing in Seattle. He then ordered the plane to take off and fly to Mexico City; during that flight, he jumped from the aircraft into the Oregon wilderness, securing his place as the only unsolved case in FAA history.
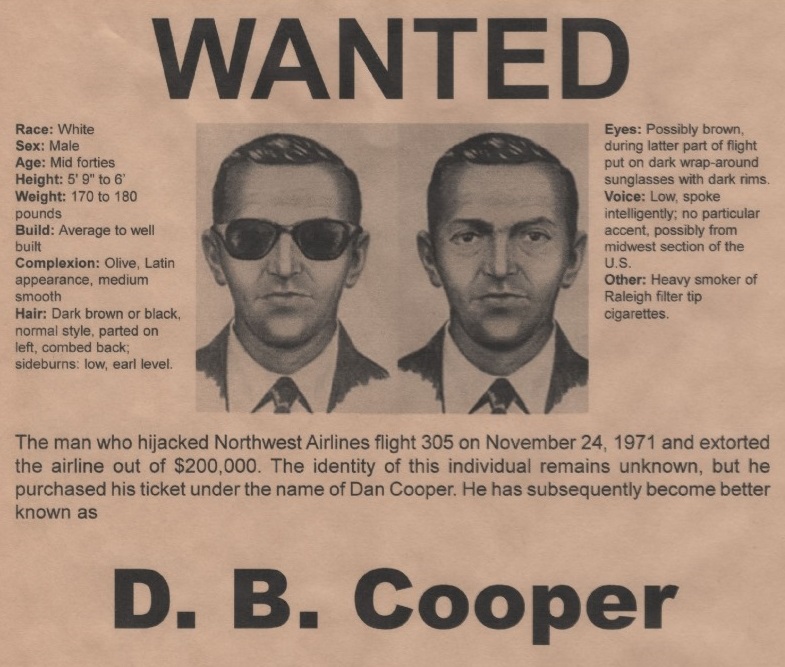
In early 2011, following a host of other investigations — both private and government-led — Tom Colbert picked up the trail of the man now known as D.B. Cooper. As an investigative reporter and producer living in Southern California, Colbert was tipped off by a source in the illicit drug trade who had credible — albeit circumstantial — evidence that D.B. Cooper was alive and living in California. Over the next few years, Colbert invested incredible amounts of time and personal resources toward tackling a 45-year-old mystery that so many other investigators before him had failed to solve.
A New Approach to Finding D.B. Cooper
Colbert assembled a large group of leading private investigators, detectives, attorneys, profilers and other subject matter experts into a group he called the “Cold Case Team.” He also knew he needed the expertise of intelligence professionals to help him organize and analyze all the evidence related to this case. While intelligence analysts almost always focus on using their skills for predictive analysis predictive analysis (i.e., what’s going to happen), Colbert knew having people proficient in intelligence collection and analysis would provide unique insight into a case that was decades old.
In December 2011, Colbert elicited my help while I was involved in an Army intelligence training contract. We had been associates and friends for a few years and he knew about my involvement in the Able Danger program. As a student, practitioner, developer and instructor of intelligence methodology, I was interested in his investigation because it was another chance for me to adapt intelligence analytical methods to a cold (very cold) case. I immediately agreed to support his efforts; he sent me a copy of a dossier on the man he suspected was D.B. Cooper.
It contained photos, maps, interview summaries and many other pieces of evidence connecting this man to the D.B. Cooper incident. Much of the initial information was secondhand and circumstantial, so Colbert was using it to provide further investigative leads for the Cold Case Team members.
Here is where I make my quick disclaimer: Collecting information on U.S. persons for intelligence purposes is prohibited by several federal regulations with very few specific exceptions. Even though I would be supporting a private investigation, I was working as a defense contractor at the time and therefore felt it was important to follow the spirit of these restrictions by creating products based only upon what the Cold Case Team provided. Neither myself nor my colleague independently searched for or collected any additional information for any part of this investigation.
That being said, it was an exceptional opportunity to use analytical intelligence techniques to assist in this investigation.
Using Link Analysis Techniques in the Investigation
In his meetings with various law enforcement officials, Colbert had grown frustrated that no one was taking the time to look through the dossier and consider the evidence. I gave it to one of my senior instructors, David D’Alessio, and asked him to make a link chart of associations using one of the best link analysis software programs available to us. A link chart is a graphic representation of the people, events, and significant items of interest (such as a bank account or address) associated with a particular subject. The key to these charts are the associations or “links” between each of the people, events and items in it.
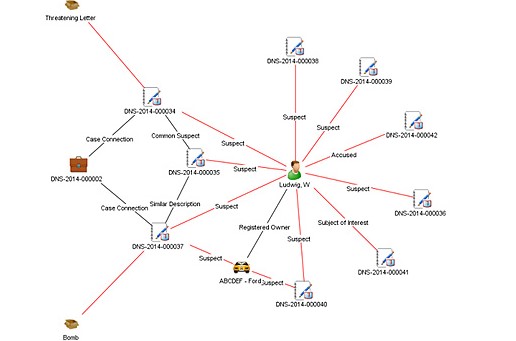
Creating this chart was a painstaking process because D’Alessio had to go through each paragraph line by line, identify the relative linkages between entities and enter them into the software program. The initial link chart started with the main suspect and then drew graphic linkages to all his known associates their connections to third parties, and a host of other associations to events, locations, aliases and specific pieces of physical evidence. Working with D’Alessio and Colbert over several iterations of this chart, we ended up with a 3×2 foot poster that, to the untrained eye, looked a lot like charts shown in court or on television shows like Law and Order. There were hundreds of links to the main suspect, the many aliases he used over the years to include military records and associations that placed him in the vicinity of the Portland, Oregon area during the time of the hijacking.
The benefit of link analysis charts is that they do more than just show connections between entities. A link chart tells a comprehensive visual story and conveys a dynamic and detailed summary of information from the document supporting it. This technique proved immensely successful, as the visual representation helped capture attention and interest from outside parties.
How Intelligence Analysis Aided in the Investigation
Besides taking text-based information and turning it into a graphic visualization for presentation purposes, a link chart also helped the investigation in other ways. First, Colbert and his team were able to see gaps in the information where investigators needed to dig deeper. He could also see which links were strong and which were weak or tenuous. The team could then plan their investigations more effectively by identifying which gaps needed to be filled and prioritize how to best use their limited resources.
This chart also had a psychological value to the Cold Case Team. In 2013, one of the team’s private investigators presented it directly to the suspect and asked him to come forward. The hope was that once the suspect knew there was a vast amount of information on the identity of D.B. Cooper (not to mention it featured his picture right at the center). Revealing this chart helped Colbert enter into negotiations with the suspect’s lawyer and he came very close to a deal that would potentially involve an admission. Unfortunately, Colbert and the Cold Case Team were turned down at the last minute due to what we believe was his fear of being connected to other illicit activities.
Why Law Enforcement Must Partner More Often with Intelligence Agencies
 Ultimately, this case demonstrates that intelligence analysis can play a crucial part in law enforcement investigations, both as a predictive asset as well as an investigative one. The D.B. Cooper investigation is decades old, but there are many other cases that are not. Other law enforcement agencies can use the techniques tested in this case to assist with other unsolved crimes, missing persons and patterns of criminal activity. It’s important for law enforcement authorities to remember that analysts in the intelligence field bring with them a toolkit that provides both unique and specialized analytical methods that can offer new perspectives. Bringing intelligence analysts into the fold of law enforcement can enhance a crime-solving team.
Ultimately, this case demonstrates that intelligence analysis can play a crucial part in law enforcement investigations, both as a predictive asset as well as an investigative one. The D.B. Cooper investigation is decades old, but there are many other cases that are not. Other law enforcement agencies can use the techniques tested in this case to assist with other unsolved crimes, missing persons and patterns of criminal activity. It’s important for law enforcement authorities to remember that analysts in the intelligence field bring with them a toolkit that provides both unique and specialized analytical methods that can offer new perspectives. Bringing intelligence analysts into the fold of law enforcement can enhance a crime-solving team.
The federal government has awesome capabilities in intelligence collection and investigation but they are not alone. There is an equally awesome, yet untapped capability, in the commercial sector and among academia to support investigations like this and other more current cases. There are uncounted numbers of undergraduate and graduate students in criminal justice, data analysis and intelligence studies courses who would be eager to support a future case. In addition, there are also many retired law enforcement and intelligence professionals who would be eager to lend their experience and subject matter expertise to similar cases and problem sets, if only to satisfy the investigative bug still within them.
While the FBI officially closed its investigation in the D.B. Cooper case earlier this year, it has not been closed in the eyes of the Cold Case Team. This team continues to move forward with its own investigation, relying on intelligence analysis methods to support them and continue to evaluate every bit of evidence in new ways.
Overland Park senior crime analyst Jamie May joins Crime Tech Solutions
September 16, 2016 – (Leander, TX) Crime Tech Solutions, a fast-growing provider of low cost / high performance crime fighting software and analytics is delighted to announce the addition of Jamie May as senior analyst and strategic advisor to the company.
 Ms. May has spent over 17 years as a crime and intelligence analyst for Overland Park Police Department in Kansas, and is a recognized expert in crime analysis, mapping, and criminal intelligence. She has sat on critical crime analysis committees including the International Association of Crime Analysts’ Ethics Committee (IACA) and is a past Vice President / Secretary at Mid American Regional Crime Analyst Network (MARCAN).
Ms. May has spent over 17 years as a crime and intelligence analyst for Overland Park Police Department in Kansas, and is a recognized expert in crime analysis, mapping, and criminal intelligence. She has sat on critical crime analysis committees including the International Association of Crime Analysts’ Ethics Committee (IACA) and is a past Vice President / Secretary at Mid American Regional Crime Analyst Network (MARCAN).
“Jamie brings an incredible amount of user experience and innovation to the company”, said Kevin Konczal, Crime Tech Solutions’ VP of Sales. “She’s been active in this community for years, and co-authored the ground-breaking guide, GIS in Law Enforcement: Implementation Issues and Case Studies.”
“To me, Crime Tech Solutions represents a truly innovative company that understands how to develop and market very good technology at prices that most agencies can actually afford”, said Ms. May. “I’m looking forward to being part of the continued growth here.”
In her role with the company, Ms. May will interact with customers and prospects to help align the company’s solution strategy with market and user requirements.
 Crime Tech Solutions, who earlier this year acquired TN based Case Closed Software, delivers unique value to customers with comprehensive investigative case management software, sophisticated link analysis tools, criminal intelligence management software, and crime mapping technology that includes some of the industry’s best analytics and reporting capabilities.
Crime Tech Solutions, who earlier this year acquired TN based Case Closed Software, delivers unique value to customers with comprehensive investigative case management software, sophisticated link analysis tools, criminal intelligence management software, and crime mapping technology that includes some of the industry’s best analytics and reporting capabilities.
Why is Oregon conducting Intelligence work?
The headline on OPB.org is rather silly, actually….
Why Is The State Of Oregon Conducting Intelligence Work?
Well, you know, because Intelligence work is kind of important. The question isn’t ‘why’… the question is ‘how’. Read on…
 The article is an excellent read, and outlines precisely why compliance with Federal regulation 28 CFR Part 23 is important. The regulation outlines standards for operating federally grant-funded multijurisdictional criminal intelligence systems. It specifically provides guidance in five primary areas: submission and entry of criminal intelligence information, security, inquiry, dissemination, and review-and-purge process.
The article is an excellent read, and outlines precisely why compliance with Federal regulation 28 CFR Part 23 is important. The regulation outlines standards for operating federally grant-funded multijurisdictional criminal intelligence systems. It specifically provides guidance in five primary areas: submission and entry of criminal intelligence information, security, inquiry, dissemination, and review-and-purge process.
See a robust 28 CFR Part 23 compliant criminal intelligence system from Crime Tech Solutions HERE.
What follows is a cut-and-paste of the article as it appears originally.
“The Oregon Department of Justice recently commissioned a review into why state investigators were scrutinizing Oregonians who used the hashtag #BlackLivesMatter on social media, including tweets by the head of the agency’s own Civil Rights Division. The resulting report suggests that two employees potentially broke state laws with their searches, but ultimately acted on their own volition.The state investigators who conducted the searches are part of an intelligence unit at the DOJ’s Terrorism Information Threat Assessment Network Fusion Center, part of a criminal intelligence unit at the DOJ. The Fusion Center is designed to prevent criminal activity and monitor public safety and specifically, terrorism threats in Oregon. The center collects data and shares information up and down the chain between federal, state and local law enforcement agencies.The Black Lives Matter investigation has raised questions about the role of the Oregon Fusion Center and the cultural competency of its employees. OPB decided to take a closer look at this criminal intelligence unit:Who Works At The Fusion Center, And What Exactly Do They Do?The state-run center has been part of the DOJ’s Criminal Justice Division since 2007 and consists of eight employees, mostly research analysts. Some of those employees also work on other criminal cases. But Fusion Center work is often focused on producing terrorism threat assessments. Analysts research potential threats in advance of major events, such as the governor’s inauguration. Those assessments are used by law enforcement for event preparation and security. In an interview with OPB’s John Sepulvado, Oregon Attorney General Ellen Rosenblum said the center is essential to public safety.
“The Pendleton Round-Up, I know they’ve used the Fusion Center to do threat assessments to ensure safety of those who come to Pendleton for the event,” Rosenblum said. She also cited Oregon’s frequent hosting of international track meets: “I know we have participated there to ensure the safety of the participants and the community.”The Fusion Center also distributes safety and informational bulletins to other law enforcement agencies. Department of Justice spokeswoman Kristina Edmunson pointed to a 2014 example in which a center’s bulletin helped identify a rape suspect. The Port of Portland Police Department requested the Fusion Center distribute information about a rape at a hotel near Portland International Airport. The suspect’s description was distributed statewide and to the National Fusion Center Network, which DOJ officials said led to the identification and eventual arrest of the suspect.
Why Is The State Engaged In This Level Of Security And Intelligence Work?
Oregon’s Fusion Center is one of more than 70 such criminal intelligence centers across the country. President George W. Bush approved the establishment of fusion centers in 2006 with the goal of having local law enforcement and U.S. Department of Homeland Security authorities collaborate and share information. The Salem office is the only one of its kind in Oregon. The Department of Homeland Security describes fusion centers as “information sharing hubs that provide comprehensive and appropriate access, analysis, and dissemination that no other single partner can offer.” “The TITAN Fusion Center is highly regarded throughout Oregon, and highly relied upon by entities throughout the state that have events, for example, where they want to make ensure the safety of the participants,” Rosenblum said. A core concept of these centers is that employees may have local knowledge or context that federal authorities lack. So, hypothetically, if the Department of Homeland Security learned of a terrorism threat in, say, Eugene, federal investigators could forward that threat to Oregon’s Fusion Center. Research analysts could investigate that threat in partnership with Eugene-area law enforcement officials, and provide local context. “The whole point of a fusion center is to fuse information,” said Portland attorney Sean Riddell, who was chief of the DOJ’s Criminal Justice Division from 2009-2011 and oversaw Oregon’s Fusion Center.
“Say for instance, a law enforcement agency in Medford calls, says ‘We’re looking at this house and this person for trafficking of narcotics, and we don’t want to trip over another agency,” Riddell said. “They’d ask, ‘Is somebody else looking at him?’” The Fusion Center could then examine the files of other law enforcement agencies, such as the U.S. Drug Enforcement Agency. If the DEA did in fact have an open file on that individual, the center could facilitate the sharing of information about the two investigations between agencies.
How Is The Fusion Center Funded?
Five Fusion Center positions are funded by the state legislature in the amount of $1.3 million for the 2015-2017 biennia. The other three staffers are paid via grants or federal money, according to the DOJ.
What Kinds Of Information Can Oregon’s Fusion Center Collect And Analyze?
The Fusion Center has access to an array of criminal and law enforcement records including criminal histories, suspicious activity reports and case records from federal, local and state agencies. They can research individuals, locations or organizations based on “reasonable suspicions.” The center may follow-up on tips and reports that come from individuals as well as other law enforcement agencies.
Fusion Centers have been criticized by the American Civil Liberties Union and other organizations for excessive secrecy standards that may limit public oversight, data collection that could threaten individual privacy, and ambiguous lines of authority.
The Oregon center is not allowed to seek out information about an individual on the basis of religious, political, racial or social views, per state law. They’re also not supposed to investigate people based on their participation in a particular non-criminal organization or event.
So it’s possible that Fusion Center investigators violated state law by conducting social media searches for #BlackLivesMatter on Twitter.
Rosenblum wouldn’t speak to whether the DOJ investigators involved broke the law. She said the DOJ plans to require diversity and bias training among staff in the future.
Carolyn Walker, an employment attorney with Portland law firm Stoel Rives prepared the DOJ report looking into the incident. She determined that intelligence unit staff need cultural competency training to help separate potential threats from everyday social media traffic.
The report shows that a DOJ employee was concerned that Erious Johnson Jr., who heads the Oregon Department of Justice’s Civil Rights Division, “constituted a potential threat to police,” citing several of Johnson’s tweets. One tweet the employee referenced included the lyrics “Consider yourself warned,” and a logo from the 1980s rap group Public Enemy. The investigators apparently didn’t understand the cultural reference.
“The Intelligence Unit as a whole would benefit from clear and consistent leadership and direction,” Walker wrote in her report, “specifically with respect to electronic monitoring of social media.””
__
Crime Tech Solutions is a low price / high performance innovator in crime analytics and law enforcement crime-fighting software. The clear price/performance leader for crime fighting software, the company’s offerings include sophisticated Case Closed™ investigative case management and major case management, GangBuster™ gang intelligence software, powerful link analysis software, evidence management, mobile applications for law enforcement, comprehensive crime analytics with mapping and predictive policing, and 28 CFR Part 23 compliant criminal intelligence database management systems.