Posted by Tyler Wood Crime Tech Solutions, your source for investigation software.
The information provided on this page comes primarily from Boba, R. (2008: Pages 3 through 6) Crime Analysis with Crime Mapping. For a full discussion of the crime analysis discipline, refer to the book which can be obtained through www.sagepub.com.
Over the past 20 years, many scholars have developed definitions of crime analysis. Although definitions of crime analysis differ in specifics, they share several common components: all agree that crime analysis supports the mission of the police agency, utilizes systematic methods and information, and provides information to a range of audiences. Thus, the following definition of crime analysis is used as the foundation of this initiative:
Crime analysis is the systematic study of crime and disorder problems as well as other police–related issues—including sociodemographic, spatial, and temporal factors—to assist the police in criminal apprehension, crime and disorder reduction, crime prevention, and evaluation.
Clarification of each aspect of this definition helps to demonstrate the various elements of crime analysis. Generally, to study means to inquire into, investigate, examine closely, and/or scrutinize information. Crime analysis, then, is the focused and systematic examination of crime and disorder problems as well as other police-related issues. Crime analysis is not haphazard or anecdotal; rather, it involves the application of social science data collection procedures, analytical methods, and statistical techniques.
More specifically, crime analysis employs both qualitative and quantitative data and methods. Crime analysts use qualitative data and methods when they examine non-numerical data for the purpose of discovering underlying meanings and patterns of relationships. The qualitative methods specific to crime analysis include field research (such as observing characteristics of locations) and content analysis (such as examining police report narratives). Crime analysts use quantitative data and methods when they conduct statistical analysis of numerical or categorical data. Although much of the work in crime analysis is quantitative, crime analysts use simple statistical methods, such as frequencies, percentages, means, and rates. Typical crime analysis tools include link analysis and crime mapping software.
The central focus of crime analysis is the study of crime (e.g., rape, robbery, and burglary); disorder problems (e.g., noise complaints, burglar alarms, and suspicious activity); and information related to the nature of incidents, offenders, and victims or targets of crime (targets refer to inanimate objects, such as buildings or property). Crime analysts also study other police-related operational issues, such as staffing needs and areas of police service. Even though this discipline is called crime analysis, it actually includes much more than just the examination of crime incidents.
Although many different characteristics of crime and disorder are relevant in crime analysis, the three most important kinds of information that crime analysts use are sociodemographic, spatial, and temporal. Sociodemographic information consists of the personal characteristics of individuals and groups, such as sex, race, income, age, and education. On an individual level, crime analysts use sociodemographic information to search for and identify crime suspects. On a broader level, they use such information to determine the characteristics of groups and how they relate to crime. For example, analysts may use sociodemographic information to answer the question, “Is there a white, male suspect, 30 to 35 years of age, with brown hair and brown eyes, to link to a particular robbery?” or “Can demographic characteristics explain why the people in one group are victimized more often than people in another group in a particular area?”
The spatial nature of crime and other police-related issues is central to understanding the nature of a problem. In recent years, improvements in computer technology and the availability of electronic data have facilitated a larger role for spatial analysis in crime analysis. Visual displays of crime locations (maps) and their relationship to other events and geographic features are essential to understanding the nature of crime and disorder. Recent developments in criminological theory have encouraged crime analysts to focus on geographic patterns of crime, by examining situations in which victims and offenders come together in time and space.
Finally, the temporal nature of crime, disorder, and other police-related issues is a major component of crime analysis. Crime analysts conduct several levels of temporal analysis, including (a) examination of long-term patterns in crime trends over several years, the seasonal nature of crime, and patterns by month; (b) examination of mid-length patterns, such as patterns by day of week and time of day; and (c) examination of short-term patterns, such as patterns by day of the week, time of day, or time between incidents within a particular crime series.
The final part of the crime analysis definition—”to assist the police in criminal apprehension, crime and disorder reduction, crime prevention, and evaluation” generally summarizes the purpose and goals of crime analysis. The primary purpose of crime analysis is to support (i.e., “assist”) the operations of a police department. Without police, crime analysis would not exist as it is defined here.
The first goal of crime analysis is to assist in criminal apprehension, given that this is a fundamental goal of the police. For instance, a detective may be investigating a robbery incident in which the perpetrator used a particular modus operandi (i.e., method of the crime). A crime analyst might assist the detective by searching a database of previous robberies for similar cases.
Another fundamental police goal is to prevent crime through methods other than apprehension. Thus, the second goal of crime analysis is to help identify and analyze crime and disorder problems as well as to develop crime prevention responses for those problems. For example, members of a police department may wish to conduct a residential burglary prevention campaign and would like to target their resources in areas with the largest residential burglary problem. A crime analyst can assist by conducting an analysis of residential burglary to examine how, when, and where the burglaries occurred along with which items were stolen. The analyst can then use this information to develop crime prevention suggestions, (such as closing and locking garage doors) for specific areas.
Many of the problems that police deal with or are asked to solve are not criminal in nature; rather, they are related to quality of life and disorder. Some examples include false burglar alarms, loud noise complaints, traffic control, and neighbor disputes. The third goal of crime analysis stems from the police objective to reduce crime and disorder. Crime analysts can assist police with these efforts by researching and analyzing problems such as suspicious activity, noise complaints, code violations, and trespass warnings. This research can provide officers with information they can use to address these issues before they become more serious criminal problems.
The final goal of crime analysis is to help with the evaluation of police efforts by determining the level of success of programs and initiatives implemented to control and prevent crime and disorder and measuring how effectively police organizations are run. In recent years, local police agencies have become increasingly interested in determining the effectiveness of their crime control and prevention programs and initiatives. For example, an evaluation might be conducted to determine the effectiveness of a two-month burglary surveillance or of a crime prevention program that has sought to implement crime prevention through environmental design (CPTED) principles within several apartment communities. Crime analysts also assist police departments in evaluating internal organizational procedures, such as resource allocation (i.e., how officers are assigned to patrol areas), realignment of geographic boundaries, the forecasting of staffing needs, and the development of performance measures. Police agencies keep such procedures under constant scrutiny in order to ensure that the agencies are running effectively.
In summary, the primary objective of crime analysis is to assist the police in reducing and preventing crime and disorder. Present cutting edge policing strategies, such as hotspots policing, problem-oriented policing, disorder policing, intelligence-led policing, and CompStat management strategies, are centered on directing crime prevention and crime reduction responses based on crime analysis results. Although crime analysis is recognized today as important by both the policing and the academic communities, it is a young discipline and is still being developed. Consequently, it is necessary to provide new and experienced crime analysts with training and assistance that improves their skills and provides them examples of best practices from around the country and the world. http://crimetechsolutions.com
Tag Archives: fraud software
Uncovering Fraud means Uncovering Non-Obvious Relationships
Posted by Tyler Wood, Operations Manager at Crime Tech Solutions
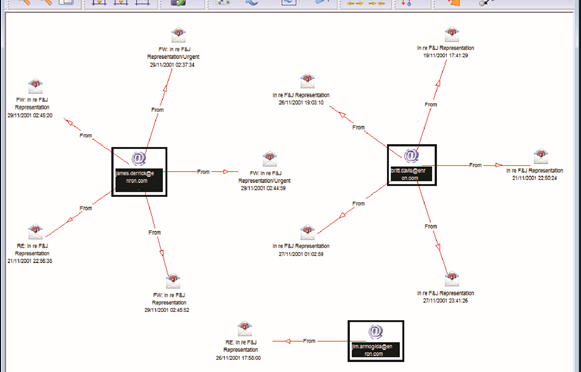
Although no fraud prevention measures are ever 100% foolproof, significant progress can be achieved by looking beyond the individual data points to the relationships between them. This is the science of link analysis.
Looking at data relationships isn’t straightforward and doesn’t necessarily mean gathering new or more data. The key to battling financial crimes it is to look at the existing data in a new way – namely, in a way that makes underlying connections and patterns using powerful but proven tools such as the Sentinel Visualizer software offered by Crime Tech Solutions.
Unlike most other ways of looking at data, link analysis charts are designed to exploit relationships in data. That means they can uncover patterns difficult to detect using traditional representations such as tables.
Now, we all know that there are various types of fraud – first-party, insurance, and e-commerce fraud, for instance. What they all have in common is the layers of dishonesty to hide the crime. In each of these types of fraud, link analysis from Crime Tech Solutions offers a significant opportunity to augment existing methods of fraud detection, making evasion substantially more difficult.
Let’s take a look at first-party fraud. This type of fraud involves criminals who apply for loans or credit cards but who have no intention of ever paying the money back. It’s a serious problem for banks, who lose tens of billions of dollars every year to this form of fraud. It’s hard to detect and the fraudsters are good at impersonating good customers until the moment they do their ‘Bust-Out,’ i.e. cleaning out all their accounts and disappearing.
Another factor is the nature of the relationships between the participants in the fraud ring. While these characteristics make these schemes very damaging, it also renders them especially vulnerable to link analysis methods of fraud detection.
That’s because a first-party fraud ring involves a group of people sharing a subset of legitimate contact information and bogus information, and then combining them to create a number of synthetic identities. With these fake identities, fraudsters open new accounts for new forms of loans.
The fraudsters’ accounts are used in a normal manner with regular purchases and timely payments so that the banks gain confidence and slowly increase credit over time. Then, one day… Poof! The credit cards are maxed out and everyone has disappeared. The fraudsters are long gone and ready to hit the next bank down the road.
Gartner Group believes in a layered model for fraud prevention that starts with simple discrete methods but progresses to more elaborate types of analysis. The final layer, Layer 5, is called “Entity Link Analysis” and is designed to leverage connections in data in order to detect organized fraud.
In other words, Gartner believes that running appropriate entity link analysis queries can help organizations identify probable fraud rings during or even before the fraud occurs.
IBM Crime Analytics: Missing the mark? CTS Hits the bullseye!
 Posted by Crime Tech Solutions – Your source for analytics in the fight against crime and fraud.
Posted by Crime Tech Solutions – Your source for analytics in the fight against crime and fraud.
September 7, 2015. IBM announced this week a major update to its IBM i2 Safer Planet intelligence portfolio that includes a major overhaul of the widely used Analyst’s Notebook product. The product, which has become increasingly abandoned by its user base over the past five years, is now being positioned as ‘slicker‘ than previous versions.
IBM suggests that the new version scales from one to 1,000 users and can ingest petabytes of information to visualize. (A single petabyte roughly translates to 20,000,000 four-drawer filing cabinets completely filled with text).
That’s a lot of data. Seems to me that analysts are already inundated with data… now they need more?
This all begs the question: “Where is IBM headed with this product?”
The evidence seems to point to the fact that IBM wants this suite of products to compete head-to-head with money-raising machine and media darling Palantir Technologies. If I’m IBM, that makes sense. Palantir has been eating Big Blue’s lunch for a few years now, particularly at the lucrative US Federal market level. Worse yet, for IBM i2, is the recent news of a new competitor with even more powerful technology.
If I’m a crime or fraud analyst, however, I have to view this as IBM moving further and further away from my reality.
The reality? Nobody has ever yelled “Help! I’ve been robbed. Call the petabytes of ‘slick’ data!” No, this tiring ‘big data’ discussion is not really part of the day to day work for the vast majority of analysts. Smart people using appropriate data with intuitive and flexible crime technology solutions… that’s the reality for most of us.
So, as IBM moves their market-leading tool higher and higher into the stratosphere, where does the industry turn for more practical desktop solutions with realistic pricing? For more and more customers around the world, the answer is a crime and fraud link analytics tool from Crime Tech Solutions.
No, it won’t ingest 20,000,000 four-drawer filing cabinets of data, and it’s more ‘efficient‘ than ‘slick‘. Still, the product has been around for decades as a strong competitor to Analysts Notebook, and is well-supported by a network of strategic partners around the world. Importantly, it is the only American made and supported alternative. Period. It’s also, seemingly, the last man standing in the market for efficient and cost-effective tools that can be used by real people doing their real jobs.
The Name Game Fraud
 Posted by Douglas Wood, Editor. Alright everybody, let’s play a game. The name game!
Posted by Douglas Wood, Editor. Alright everybody, let’s play a game. The name game!
“Shirley, Shirley bo Birley. Bonana fanna fo Firley. Fee fy mo Mirley. Shirley!” No, not THAT name game. (Admit it… you used to love singing the “Chuck” version, though.)
The name game I’m referring to is slightly more sinister, and relates to the criminal intent to deceive others for gain by slightly misrepresenting attributes in order to circumvent fraud detection techniques. Pretty much anywhere money, goods, or services are dispensed, folks play the name game.
Utilities, Insurance, Medicaid, retail, FEMA. You name it.
Several years ago, I helped a large online insurance provider determine the extent to which they were offering insurance policies to corporations and individuals with whom they specifically did not want to do business. Here’s what the insurer knew:
- They had standard application questions designed to both determine the insurance quote AND to ensure that they were not doing business with undesirables. These questions included things such as full name, address, telephone number, date of birth, etc… but also questions related to the insured property. “Do you live within a mile of a fire station?”, Does your home have smoke detectors?”, and “Is your house made of matchsticks?”
- On top of the questions, the insurer had a list of entities with whom the knew they did not want to do business for one reason or another. Perhaps Charlie Cheat had some previously questionable claims… he would have been on their list.
In order to circumvent the fraud prevention techniques, of course, the unscrupulous types figured out how to mislead the insurer just enough so that the policy was approved. Once approved, the car would immediately be stolen. The house would immediately burn down, etc.
The most common way by which the fraudsters misled the insurers was a combination of The Name Game and modifying answers until the screening system was fooled. Through a combination of investigative case management and link analysis software, I went back and looked at several months of historical data and found some amazing techniques used by the criminals. Specifically, I found one customer who made 19 separate online applications – each time changing just one attribute or answer slightly – until the policy was issued. Within a week of the policy issue, a claim was made. You can use your imagination to determine if it was a legitimate claim. 😀
This customer, Charlie Cheat (obviously not his real name), first used his real name, address, telephone number, and date of birth… and answered all of the screening questions honestly. Because he did not meet the criteria AND appeared on an internal watch list for having suspicious previous claims, his application was automatically denied. Then he had his wife, Cheri Cheat, complete the application in hopes that the system would see a different name and approve the policy. Thirdly, he modified his name to Charlie Cheat, Chuck E. Cheat, and so on. Still no go. His address went from 123 Fifth Street to 123-A 5th Street. You get the picture.
Then he began to modify answers to the screening questions. All of a sudden, he DID live within a mile of a fire station… and his house was NOT made of matchsticks… and was NOT located next door to a fireworks factory. After almost two dozen attempts, he was finally issued the policy under a slightly revised name, a tweak in his address, and some less-than-truthful answers on the screening page. By investing in powerful investigative case management software with link analysis and fuzzy matching this insurer was able to dramatically decrease the number of policies issued to known fraudsters or otherwise ineligible entities.
Every time a new policy is applied for, the system analyzes the data against previous responses and internal watch lists in real time. In other words, Charlie and Cheri just found it a lot more difficult to rip this insurer off. These same situations occur in other arenas, costing us millions annually in increased taxes and prices. So, what happened to the Cheats after singing the name game?
Let’s just say that after receiving a letter from the insurer, Charlie and Cheri started singing a different tune altogether.
Using Link Analysis to untangle fraud webs
Posted by Douglas Wood, Editor.
NOTE: This article originally appeared HERE by Jane Antonio. I think it’s a great read…
Link analysis has become an important technique for discovering hidden relationships involved in healthcare fraud. An excellent online source, FierceHealthPayer:AntiFraud, recently spoke to Vincent Boyd Bryant about the value of this tool for payer special investigations units.
A former biometric scientist for the U.S. Department of Defense, Bryant has 30 years of experience in law enforcement and intelligence analysis. He’s an internationally-experienced investigations and forensics expert who’s worked for a leading health insurer on government business fraud and abuse cases.
How does interactive link analysis help insurers prevent healthcare fraud? Can you share an example of how the tool works?
One thing criminals do best is hide pots of money in different places. As a small criminal operation becomes successful, it will often expand its revenue streams through associated businesses. Link analysis is about trying to figure out where all those different baskets of revenue may be. Insurers are drowning in a sea of theft. Here’s where link analysis becomes beneficial. Once insurers discover a small basket of money lost to a criminal enterprise, then serious research needs to go into finding out who owns the company, who they’re associated with, what kinds of business they’re doing and if there are claims associated with it.
You may find a clinic, for example, connected to and working near a pharmacy, a medical equipment supplier, a home healthcare services provider and a construction company. Diving into those companies and what they do, you find that they’re serving older patients for whom multiple claims from many providers exist. The construction company may be building wheelchair ramps on homes. And you may find that the providers are claiming payment for dead people. Overall, using this tool requires significant curiosity and a willingness to look beyond the obvious.
Any investigation consists of aggregating facts, generating impressions and creating a theory about what happened. Then you work to confirm or disconfirm your theory. It’s important to have tools that let you take large masses of facts and visualize them in ways that cue you to look closer.
Let’s say you investigate a large medical practice and interview “Doctor Jones.” The day after the interview, you learn through link analysis that he transferred $11 million from his primary bank account to the Cayman Islands. And in looking at Dr. Jones’ phone records, you see he called six people, each of whom was the head of another individual practice on whose board Dr. Jones sits. Now the investigation expands, since the timing of those phone calls was contemporaneous to the money taking flight.
Why are tight clusters of similar entities possible indicators of fraud, waste or abuse?
Bryant: When you find a business engaged in dishonest practices and see its different relationships with providers working out of the same building, this gives rise to reasonable suspicion. The case merits a closer look. Examining claims and talking to members served by those companies will give you an indication of how legitimate the operation is.
What are the advantages of link analysis to payer special investigation units, and how are SIUs using its results?
Bryant: Link analysis can define relationships through data insurers haven’t always had, data that traditionally belonged to law enforcement.
Link analysis results in a visual reference that can take many forms: It can look like a family tree, an organizational chart or a time line. This reference helps investigators assess large masses of data for clustering and helps them arrive at a conclusion more rapidly.
Using link analysis, an investigator can dump in large amounts of data–such as patient lists from multiple practices–and see who’s serving the same patient. This can identify those who doctor shop for pain medication, for example. Link analysis can chart where this person was and when, showing the total amount of medication prescribed and giving you an idea of how the person is operating.
What types of data does link analysis integrate?
Bryant: Any type of data that can be sorted and tied together can be loaded into the tool. Examples include telephone records, addresses, vehicle information, corporate records that list individuals serving on boards and banking and financial information. Larger supporting documents can be loaded and linked to the charts, making cases easier to present to a jury.
Linked analysis can pull in data from state government agencies, county tax records or police records from state departments of correction and make those available in one bucket. In most cases, this is more efficient than the hours of labor needed to dig up these types of public records through site visits.
Is there anything else payers should know about link analysis that wasn’t covered in the above questions?
Bryant: The critical thing is remembering that you don’t know what you don’t know. If a provider or member is stealing from the plan in what looks like dribs and drabs, insurers may never discover the true extent of the losses. But if–as a part of any fraud allegation that arises–you look at what and who is associated with the subject of the complaint, what started as a $100,000 questionable claims allegation can expose millions of dollars in inappropriate billings spread across different entities.
Part 2: Investigating the Investigations – X Marks the Spot
Posted by Douglas Wood, Editor. http://www.linkedin.com/in/dougwood
Part One of this series is HERE.
Most of the financial crimes investigators I know live in a world where they dream of moving things from their Inbox to their Outbox. Oh, like everyone else, they also dream about winning the lottery, flying without wings, and being naked in public. But in terms of the important roles they perform within both public and private sectors, there is simply Investigating (Inbox) and Adjudication (Outbox). Getting there requires a unique blend of their own capabilities, the availability of data, and the technology that allows them to operate. In the diagram below, ‘X‘ marks the spot where crimes are moved from the Inbox to the Outbox. Without any of those three components, an investigation becomes exponentially more difficult to conclude.
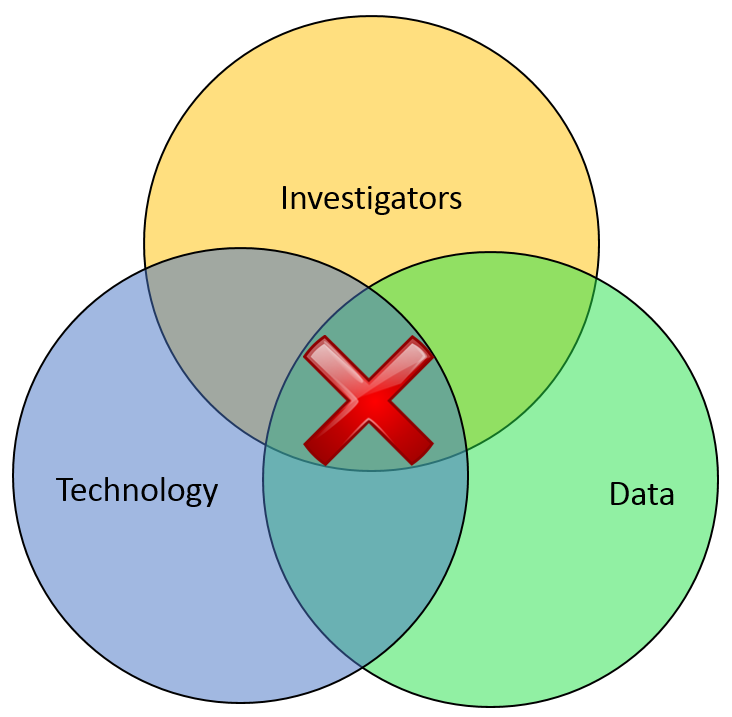
In part one of this article two weeks ago, I wrote about the Investigation Management & Adjudication (IMA) side of financial crimes investigations. I coined that term to call out what is arguably the most integral component of any enterprise fraud management (EFM) ecosystem. The original EFM overview is here.
“The job is almost unrecognizable to those who once used rotary phones in smoke filled offices…
Twenty years ago, IMA was based primarily upon human eyes. Yes, there were technology tools available such as Wordperfect charts and Lotus 1-2-3 spreadsheets, but ultimately it was the investigator who was tasked with finding interesting connections across an array of data elements including handwritten briefs, telephone bills, lists of suspect information, and discussions with other investigators. The job got done, though. Things moved from the Inbox to the Outbox, arrests were made and prosecutions were successful. Kudos, therefore, to all of the investigators who worked in this environment.
Fast forward to today, and the investigator’s world is dramatically different. The job is the same, of course, but the tools and mass availability of data has made the job almost unrecognizable to those who once used rotary phones in smoke filled offices. Organizations began building enterprise data warehouses designed to provide a single version of the truth. Identity Resolution technology was implemented to help investigators recognize similarities between entities in that data warehouse. And today, powerful new IMA tools are allowing easy ingestion of that data, improved methods for securely sharing across jurisdictions, automated link discovery, non-obvious relationship detection, and interactive visualization tools, and -importantly – packaged e-briefs which can be understood and used by law enforcement, prosecutors, or adjudication experts.
“Without any of these components, everything risks falling to the outhouse…
With all these new technologies, surely the job of the Investigator is becoming easier? Not so fast.
IMA tools – and other EFM tools – do nothing by themselves. The data – big data – does nothing by itself. It just sits there. The best investigators – without tools or data – are rendered impotent. Only the combination of skilled, trained investigators using the best IMA tools to analyze the most useful data available results in moving things from the Inbox to the Outbox. Without any of these components… everything eventually risks falling to the Outhouse.
Kudos again, Mr. and Mrs. Investigator. You’ll always be at the heart of every investigation. Here’s hoping you solve for X every day.
Lottery Fraud – How lucky can you get?
Posted by Douglas Wood, Editor.
Two weeks ago, I wrote in this space about some interesting experiences I’d had working through Workers Compensation Premium Fraud at a government run program. This week, I received a fraud alert about a retailer being banned from ever selling lottery tickets, and it reminded me of a great exercise I underwent with a government run Lottery corporation several years ago.
Lottery retailer fraud is simple and widespread. NBC Dateline ran a two hour episode several years ago, outlining the problem and going undercover to catch some bad guys in action.
In a nutshell, there are many unscrupulous retailers who outright lie to patrons when asked to check their numbers. Joe the customer hands the ticket over to the clerk and asks her to see if it’s a winner. She scans the barcode and says “Sorry, Joe… you didn’t win“. Then, as Joe heads out the door, she picks the ticket up from the trash bin knowing full well that it’s a big winner. Here’s a real life example.
How bad is the problem? According to Dateline NBC, a Philadelphia retailer cashed eighteen lottery tickets in three months for a total of $45,000. In New Jersey, a retailer cashed 105 lottery tickets for more than $236,000. In Illinois, it found one store where four employees and five of their relatives cashed a total of 556 winning tickets, for more than $1,600,000. In California, lottery investigators were seeing the same thing. In fact, in 2007, the five most frequent winners in California were retailers. One store owner in Los Angeles allegedly cashed 121 tickets for more than $160,000.
As a result of shrinking public trust and outrage, many lottery corporations have taken to more tightly scrutinize ‘winning’ ticket claims from lottery retailers. What, though, if the lottery clerk has her husband cash the ticket? Or her next door neighbor? How can you scrutinize large winning ticket claims without grinding the process to a halt?
That’s precisely where my customer was when they called me.
As with any fraud prevention program, the availability of data was of utmost importance as we scoped out the technology solution. The lottery corporation obviously knew who their retailers were (XYZ Groceries, ABC Petroleum, etc) but how did that help point to a specific Suzie Employee within that retailer? After all, companies weren’t cashing in winning tickets. People were.
Well, we helped them realize that they had employee names as a result of the mandatory training they offered retailers for handling sales of lottery tickets. Each employee of a retailer was required to take a brief online course for certification purposes, and entered some of their personal data (name, date of birth) in order to begin the training.
That got us through step one – the employees. In order to get to the next level of culprit (the family or neighbors of employees), we incorporated publicly available data into the mix.
Through a defined process of business discovery and problem resolution, we designed a process where individuals redeeming winning tickets above a certain value would be compared to the data of retail employees. If it was determined that a winner closely resembled a retail employee, an alert was automatically generated for investigators.
If a winner was determined to be closely acquainted to a retail employee via relationship-detection technology and public data, an alert was again generated. The specifics of how relationships were determined and analyzed won’t be disclosed for obvious reasons, but one example would be a shared address or telephone number.
This particularly lottery corporation was fortunate that they had a mechanism by which to collect employee data. In meeting with dozens of other Lotteries in the years since, I’ve learned that not enough of them have a similar process in place. Unfortunately, without that initial data set, it’s more difficult to detect this type of fraud.
In the case of my client, however, they began immediately seeing benefits in the new process and several fraudulent retailers were exposed. It was some very interesting work, and a cool exercise in problem solving for complex fraud.
Posted by Douglas G. Wood. Check out my site at www.crimetechsolutions.com