Posted by Tyler Wood, Operations Manager at Case Closed Software and Crime Tech Solutions
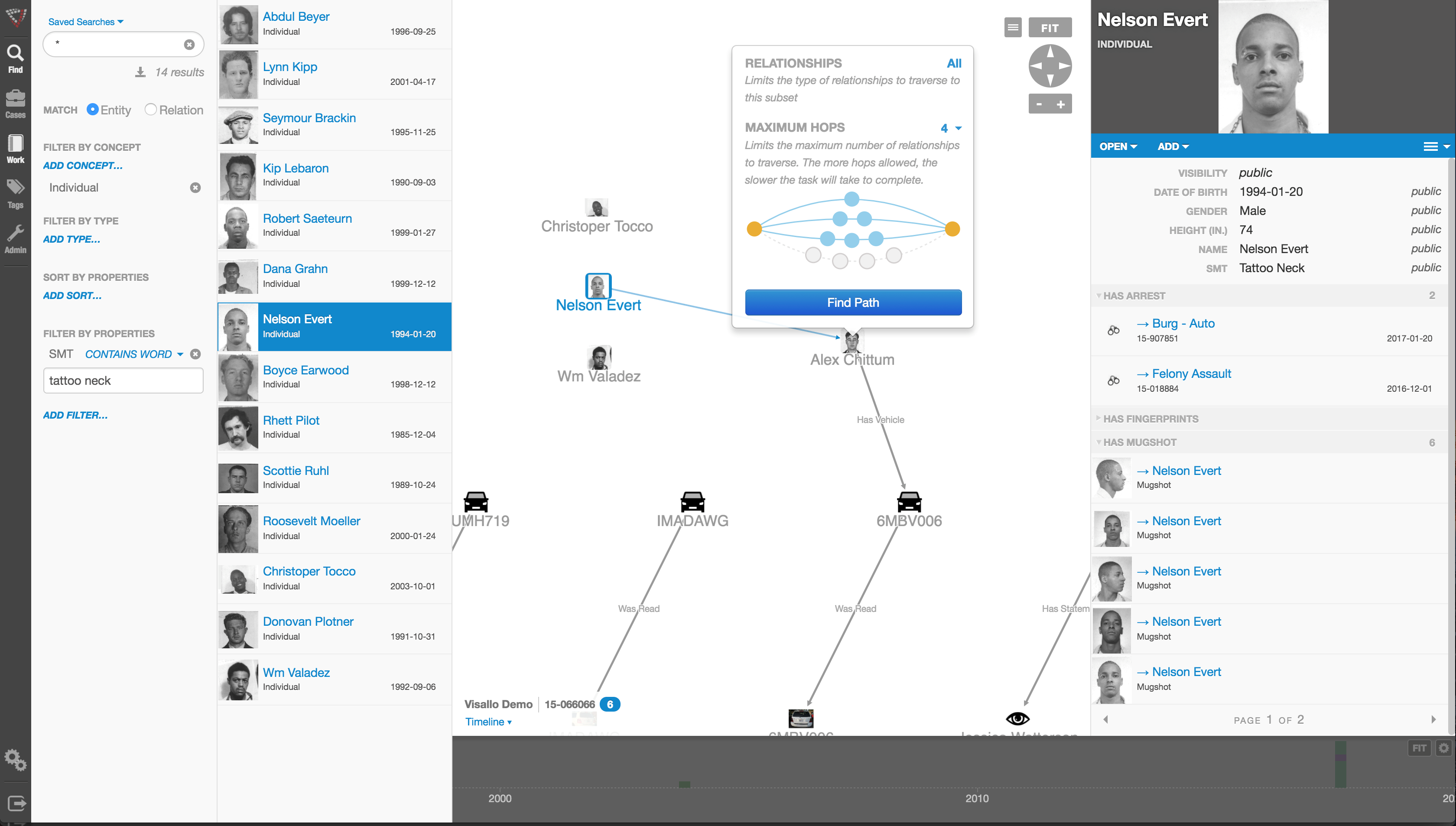
Investigative link analysis and visualization software is a powerful tool for both law enforcement agencies and the private sector investigators alike. It allows investigators to visualize the hidden, non-obvious connections that would likely otherwise go undetected. After all, we know that the human brain is much more easily able to make connections when information is presented via images rather than text.
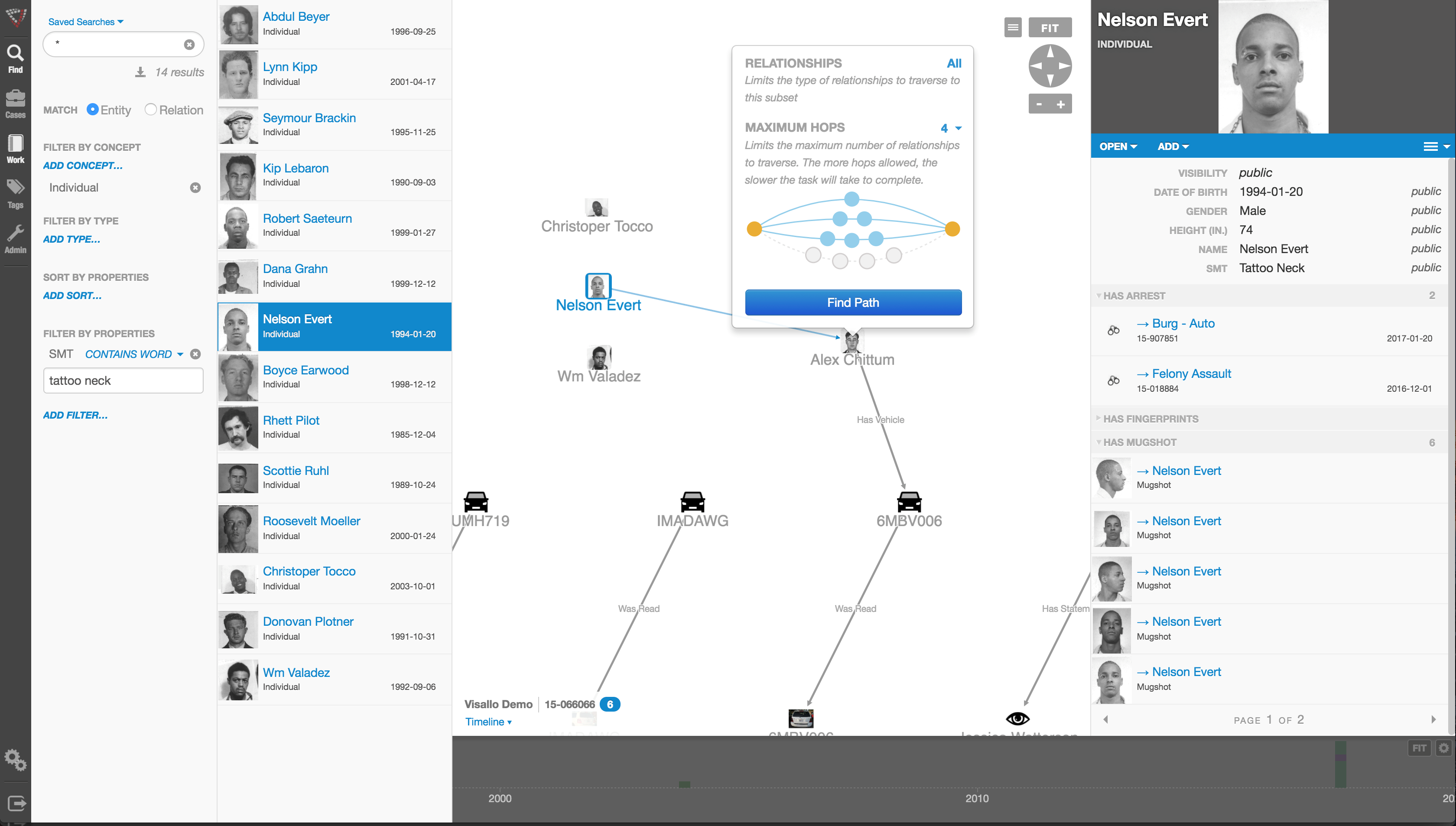
The software does, however, need a human to tell it what to look for, and where to look for it. Information is visualized in link analysis software by importing or querying a set of data, and then organizing that data according to parameters set by an investigator. The investigator is responsible for telling the software how to organize the data, and where to gather it from.
A smart investigator will utilize multiple sources when visualizing software. The majority of the time, not all the information needed for an investigation will come from the same source.
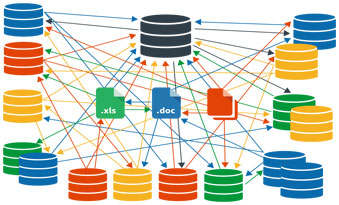
Law Enforcement investigators may need to pull RMS data, cell phone records, case management records, and even third party data, etc, to fully understand the big picture in a scenario. By using link analysis to cross-reference these data clusters against each other, the investigator is able to see even more connections, and find even more relevant data that may be crucial in solving a case.
It is important for investigators to exhaust all their resources so they can paint the clearest picture possible. This marriage of intuition and technology ensures that no connections stay hidden from investigation.
The key, as in all of life, is considering the source.
Contact us for more information about how powerful investigation big data link analysis can help your agency today.
[contact-form][contact-field label=”Name” type=”name” required=”1″ /][contact-field label=”Email” type=”email” required=”1″ /][contact-field label=”Website” type=”url” /][contact-field label=”Comment” type=”textarea” required=”1″ /][/contact-form]
Tag Archives: link visualization
SoCal City Selects Crime Tech Solutions for Link Analysis.
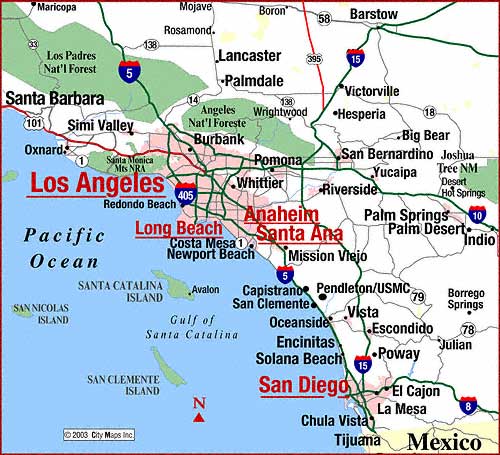 Crime Tech Solutions, LLC – a fast growing, vibrant software company based in Leander, TX today announced that a large, coastal city in California has selected them to provide sophisticated link and social network analysis software.
Crime Tech Solutions, LLC – a fast growing, vibrant software company based in Leander, TX today announced that a large, coastal city in California has selected them to provide sophisticated link and social network analysis software.
Crime Tech Solutions was awarded the contract based upon its price/performance leadership in the world of big data analytics for law enforcement and other investigative agencies.
Link analysis software is used by investigators to visualize hidden connections between people, places, and things within large and disparate data sets.
“Our link analysis software gives investigators an edge in the way they analyze data”, said Crime Tech Solutions’ CEO, Doug Wood. “By finding and displaying those hard to find connections and anomalies that reside in different data stores, our software helps investigative agencies more clearly see how networks of entities exist.”
Crime Tech Solutions said that the software implementation is already underway, and that the software will make life a little more miserable for criminals in the Southern California city.
The company also develops investigative case management and criminal intelligence software for law enforcement agencies of all sizes.
Using crime analysis solutions to take a ‘Byte’ out of crime
 Posted by Crime Tech Solutions
Posted by Crime Tech Solutions
Law enforcement agencies everywhere are tasked with reducing and investigating crime with fewer and fewer resources at their disposal. “To protect and serve” is the highest responsibilities one can sign up for, particularly in light of recent well-publicized criticisms of police by activists in every city.
That responsibility weighs even heavier in a world with no shortage of criminals and terrorists. There’s never enough money in the budget to adequately deal with all of the issues that face an individual agency on a daily basis. Never enough feet on the street, as they say.
New Tools for Age-Old Problems
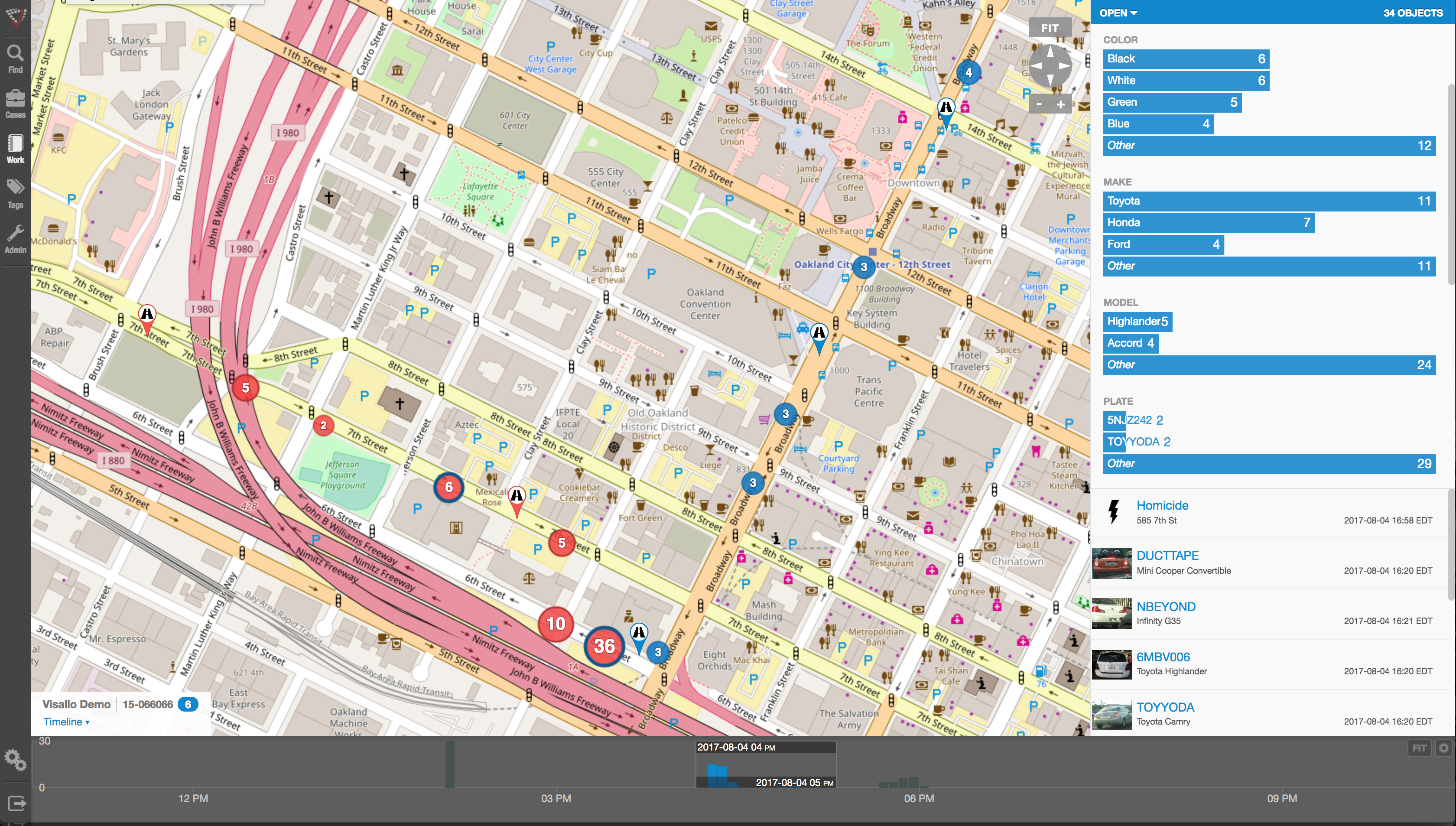
Perhaps that’s why agencies everywhere are moving to fight crime with an evolving 21st century weapon – law enforcement software including investigative case management, link and social network analysis, and, importantly, crime analytics with geospatial and temporal mapping.
Crime analytics and investigation software have proven themselves to be valuable tools in thwarting criminal activity by helping to better define resource allocation, target investigations more accurately, and enhancing public safety,
According to some reports, law enforcement budgets have been reduced by over 80% since the early 2000s. Still, agencies are asked to do more and more, with less and less.
Analytics in Policing
Analytics in law enforcement play a key role in helping law enforcement agencies better forecast what types of crimes are most likely to occur in a certain area within a certain window of time. While no predictive analytics solution offers the clarity of a crystal ball, they can be effective in affecting crime reduction and public safety.
Predictive analysis, in essence, is taking data from disparate sources, analyzing them and then using the results to anticipate, prevent and respond more effectively to future crime. Those disparate data sources typically include historical crime data from records management systems, calls for service/dispatch information, tip lines, confidential informant information, and specialized criminal intelligence data.
The Five W’s of Predictive Analytics
Within this disparate data lie the 5 W’s of information that can be used by crime analysis software to build predictions. Those key pieces include:
- Arrest records – who committed crimes
- Geospatial data – where crimes have occurred
- Temporal data – when crimes have occurred
- Statistical data – what crimes have occurred
- Investigation data – why (and how) the crimes occurred
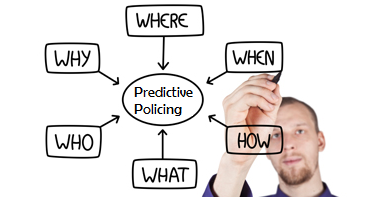
Using the 5 W’s, agencies are able to gain insight and make predictions about likely future criminal behavior. For example, if a certain type of crime (what) tends to occur in ‘this’ area (where) at ‘this’ time (when), and by ‘this’ type of individual (who) for ‘this’ reason (why)… it would be wise to deploy resources in that area at that time in order to prevent the incidents from ever occurring. This, of course, is a dramatic over-simplification of the types of analytics that make up predictive policing, but illustrates the general concept well.
Although criminals will always try to be one step ahead of the law, agencies deploying predictive analytics are able to maximize the effectiveness of its staff and other resources, increasing public safety, and keeping bad guys off the street.
More about Crime Tech Solutions
Crime Tech Solutions is an Austin, TX based provider of crime and fraud analytics software for commercial and law enforcement groups. Our offerings include sophisticated Case Closed™ investigative case management and major case management, GangBuster™ gang intelligence software, powerful link analysis software, evidence management, mobile applications for law enforcement, comprehensive crime analytics with mapping and temporal reporting, and 28 CFR Part 23 compliant criminal intelligence database management systems.
Crime Tech Solutions’ continued growth fuels management team expansion
September 13, 2016 – (Leander, TX) Crime Tech Solutions, a fast-growing provider of low cost crime fighting software and analytics today announced the appointment of Kevin Konczal as Vice President of Sales. The company created the position in response to rapid growth in market share for crime analysis and investigative case management software.
 Mr. Konczal is a seasoned start-up and marketing expert with over 30 years of diversified business management, marketing and start-up experience in information technology and consumer goods. Additionally, Konczal has over two decades of Public Safety service as a police officer, Deputy Sheriff and Special Agent.
Mr. Konczal is a seasoned start-up and marketing expert with over 30 years of diversified business management, marketing and start-up experience in information technology and consumer goods. Additionally, Konczal has over two decades of Public Safety service as a police officer, Deputy Sheriff and Special Agent.
Most recently, he held the position as a Regional Sales Manager for TriTech Software Systems, a leading provider of public safety software.
“Kevin is a seasoned executive with a combination of public service and information technology expertise”, said Crime Tech Solutions’ chief technology officer Keith Weigand. “The management team is looking forward to adding his leadership within the sales organization.”
In addition to his executive career, Konczal serves on several advisory boards, commissions and boards of directors. He attended Oakland College studying Criminal Justice and completed the Dallas Police Academy. Notably, he was awarded the Police Commendation Award for saving the lives of fellow officers in a deadly force c onfrontation.
onfrontation.
“The exciting thing about Crime Tech Solutions”, added Konczal “is their clear position as a fast-growing company dedicated to low price and high performance software for law enforcement.”
“I’m looking forward to working with a company that delivers true value to customers with comprehensive investigative case management software, sophisticated link analysis tools, criminal intelligence management software, and crime mapping technology that includes what I think are the industry’s best analytics and reporting capabilities”, he added.
Earlier this year, Crime Tech Solutions acquired Tennessee based Case Closed Software (www.caseclosedsoftware.com).
About Crime Tech Solutions
Crime Tech Solutions (www.crimetechsolutions.com) is a fast-growing U.S. based provider of low cost / high performance investigation software and crime analytics. The company proudly supports the International Association of Crime Analysts (www.iaca.net), International Association of Chiefs of Police (www.iacp.org), the National Sheriff’s Association (www.sheriffs.org), and the association of Law Enforcement Intelligence Units (www.leiu.org).
The company’s products include Case Closed investigative case management software, link and social network analytics, 28 CFR Part 23 compliant criminal intelligence management software, enterprise search for law enforcement, and crime analytics with mapping, reporting, and predictive policing.
The importance of 'gang intelligence' in law enforcement
Posted by Crime Tech Solutions
 Great article on how gang intelligence can assist law enforcement battle the problem of gangs and criminal activities. Read it HERE.
Great article on how gang intelligence can assist law enforcement battle the problem of gangs and criminal activities. Read it HERE.
Crime Tech Solutions Acquires Case Closed Software
June 1, 2016 (Austin, TX) Crime Tech Solutions, LLC, a leading provider of analytics and investigation software for law enforcement and commercial markets, today announced that it has acquired Cleveland, TN based Case Closed Software in a cash transaction. The terms of the deal were not released, but according to Crime Tech Solutions’ founder and president Douglas Wood, the acquisition brings together two dynamic and fast-growing software companies with an unparalleled complement of technologies.
“For Crime Tech Solutions, the opportunity to add Case Closed Software into the fold was too good to pass up” said Mr. Wood. “We think that the technology offered by Case Closed helps to further differentiate us in the market as the price performance leader for this type of investigative solution.”
Crime Tech Solutions, based in the city of Leander, TX, delivers advanced analytics and investigation software to commercial investigators and law enforcement agencies across the globe. Their solution suite includes criminal intelligence software, sophisticated crime analytics with geospatial mapping, and powerful link analysis and visualization software. The company says that the addition of Case Closed Software expands those offerings even further.
Case Closed Software develops and markets investigative case management software specifically designed for law enforcement agencies. The suite is built around four primary software products including best-in-class investigative case management software, property and evidence tracking, a gang database tool, and an integrated link analysis and data visualization tool. The company also plans to release the solution as Case Closed Cloud for cloud-based access.
“Case Closed couldn’t be happier than to be joining Crime Tech Solutions,” said Keith Weigand, the company’s founder. “The blending of our technologies creates a suite that will add tremendous value to our mutual customers, and will be hard for others to duplicate.”
According to both Mr. Weigand and Mr. Wood, the name Case Closed will continue on as the product brand, given its widespread popularity and loyal customer base. Crime Tech Solutions is expected to retain all Case Closed employees, with Mr. Weigand joining as the company’s chief technical officer.
Crime Tech Solutions says it expects continued growth via ongoing software sales and strategic acquisitions.
About Crime Tech Solutions
(NOTE: Crime Tech Solutions is an Austin, TX based provider of crime and fraud analytics software for commercial and law enforcement groups. Our offerings include sophisticated Case Closed™ investigative case management and major case management, GangBuster™ gang intelligence software, powerful link analysis software, evidence management, mobile applications for law enforcement, comprehensive crime analytics with mapping and predictive policing, and 28 CFR Part 23 compliant criminal intelligence database management systems.)
Is the Most Dangerous Company in America?
Posted by Tyler Wood, Operations Manager at Crime Tech Solutions
 This is a very interesting read about the current big data analytics darling, Palantir Technologies. The article from GS Early appears on the Personal Liberty website HERE.
This is a very interesting read about the current big data analytics darling, Palantir Technologies. The article from GS Early appears on the Personal Liberty website HERE.
The original article follows…
“I was reading my newsfeeds and I came across a very interesting story about this highly secretive company that is apparently buying up as much Palo Alto, California real estate as it can get its hands on.
But that isn’t even the most interesting thing about them. What piques my interest is how this start-up that just added another $450 million to its funding — it now has about $20 billion in funding — got its money.
The company is called Palantir Technologies. If the name sounds familiar, it’s because it comes from JRR Tolkein’s trilogy of fantasy novels. In The Fellowship of the Ring, Saruman the wizard uses the Palantir of Orthanc, an indestructible sphere of dark crystal, to see into the future and communicate across the world.
That sounds geeky and innocuous enough, no?
But Palantir the company’s biggest clients are the FBI, SEC and the CIA. It is a Big Data company that also has corporate clients, but much of the work — from what anyone can tell — comes from hush-hush projects for the U.S. intelligence community.
This crystal ball of a company sounds less like a quaint fantasy than a key element of the “thought police” in Philip K. Dick’s dark science fiction tale “The Minority Report.”
In “The Minority Report,” the police used computers to predict when and where a crime would occur and apprehend the perpetrator before he actually committed the crime.
The crazy thing is, we’re now living in a world where Big Data makes that possible.
First, let me explain what Big Data is. Basically, now that our lives are completely recorded in various media — traffic cameras, debit card transactions, loyalty cards, phone calls, television shows watched, internet, social media, SMS texts, etc. — computers are powerful enough now to sort through all this data from all these sources and come up with predictive patterns for individuals and groups.
This is a very hot area for retail stores. But it also has enormous implications in a variety of industries; and many of them are helpful.
It is certainly a tool that law enforcement and our intelligence services would find valuable to root out potential terrorists or groups that are planning some terrorist act. It is also useful to find people who are attempting to elude authorities. And being able to get ahead of the some of the more devious players on Wall Street and their illegal trading schemes would be nice.
But you can see where this could be turned on Americans, just as easily as the NSA turned its endeavors on to less than righteous paths.
Palantir is raising eyebrows in the epicenter of digital startups because most companies, once they reach a certain size, move out of Palo Alto and build a campus in some surrounding town.
Not Palantir. It now owns about 10-15 percent of all the available space in Palo Alto, more than 250,000 square feet. It is the fourth most valuable venture backed company in the world.
The irony in the article was, the concern wasn’t about its biggest client or what it’s doing for the CIA, it was the fact that it’s eating up all the available commercial space in Palo Alto and not leaving room for new startups.
My concern is a bit deeper. The CIA could have quietly gone to one of the major Big Data firms like Accenture or IBM and worked with them on whatever it is they needed. But instead they essentially built their own company, where there are much fewer people to throw up roadblocks to the work being done. I have no problem with government using Big Data to protect us; my concern is when intelligence and enforcement agencies have unfettered use of it.
But, there’s no turning back the clock. We are in the Big Data, cybersecurity age and plenty of these companies already exist. Usually their goal is help their clients sell more lavender soap in February or figure out what kind of salad greens a 37-year-old mother of two prefers to buy at 7 p.m. on a Wednesday evening.
On a fundamental level, it’s best to keep your digital footprint light. Make sure you have secure passwords that aren’t just 1234 or your pet’s name. Most browsers have an “incognito” mode that won’t track your browser history. But truth be told, if someone really wants your history, they can get it.
If you’re more serious about hiding your footprints, look into encrypted services like Tor (www.torproject.com) that will protect against traffic analysis (browser history, instant messaging, etc.). It’s free and very good.
Transactions in bitcoins is a way to keep your footprint light in the marketplace.
And if you’re looking to make money on the trend, there are any number of companies that are at the forefront of cybersecurity (Palo Alto Networks, FireEye, Synamtec) and Big Data (Accenture, IBM, Teradata, Oracle).
–GS Early“
(NOTE: Crime Tech Solutions is an Austin, TX based provider of crime and fraud analytics software for commercial and law enforcement groups. We proudly support the Association of Certified Fraud Examiners (ACFE), International Association of Chiefs of Police (IACP), Association of Law Enforcement Intelligence Units (LEIU) and International Association of Crime Analysts (IACA). Our offerings include sophisticated link analysis software, comprehensive crime mapping and predictive policing, and criminal intelligence database management systems.)
Link Analysis and Crime – An examination.
Posted by Tyler Wood, Operations Manager at Crime Tech Solutions
 The topic of fraud is widely discussed, and the focus of thousands upon thousands of articles. Television shows such as Crime, Inc and American Greed have become popular due, in part, to our fascination with the topic of fraud.
The topic of fraud is widely discussed, and the focus of thousands upon thousands of articles. Television shows such as Crime, Inc and American Greed have become popular due, in part, to our fascination with the topic of fraud.
The organizations that are affected by fraud are also fascinated… but for entirely different reasons. Some estimates suggest that the US economy loses 11 trillion dollars each year due to one form of fraud or another. It’s little wonder, therefore, that the companies most frequently defrauded have been heavily investing in anti-fraud technologies at an increasing rate over the past decade or more.
The biggest problem with fraud, of course, is that it is always evolving in a very Darwinian fashion. Like a living, breathing entity, fraud schemes change over time in order to survive. As the targets of fraud schemes put new policies, procedures and/or systems to deter the activities, the schemes modify and find new ways to survive.
So, since the nature of criminal activity is such that they constantly change, how do investigators find a fool proof methodology to ensure they are 100% safe from them? The answer, of course, is that they can’t. They never will; at least not until we live in a world such as the one depicted in the 2002 film Minority Report, starring Tom Cruise. In that movie, criminals are arrested prior to committing a crime based upon the predictions of psychics called ‘Precogs’. Corporations and individual targets of fraud can only wish.
Nope, there are no Precogs running around locking up would-be practitioners of fraud that would protect banks, insurance companies, Medicaid and Medicare programs, victims of Ponzi schemes, victims of identity theft, and countless others. Instead, organizations rely upon skilled knowledge workers using purpose-built crime and fraud analytics technology that can detect anomalies in patterns, suspicious transactions, hotspot mapping, networks of fraudsters, and other sophisticated data analytics tools.
Crime and fraud analytics
Any discussion of analytics and investigation software must touch upon the topic of ‘big data’. No longer just a buzz word, big data literally fuels the insights gathered by organizations in every area of business. Naturally, then, organizations who have been traditionally targeted by fraudsters have increasingly invested in crime technology such as investigation software and analytics in order to exploit the phenomenon.
 Of course, big data in and by itself does nothing. It just sits there. Nobody has ever yelled “Help! We’ve been defrauded! Call the big data!” Big data is only useful when it can be transformed into ‘smart data’. In other words, understanding the big picture of costly fraudulent activities is not akin to understanding the specifics of ‘who’ is defrauding you, and ‘how’ they are doing it.
Of course, big data in and by itself does nothing. It just sits there. Nobody has ever yelled “Help! We’ve been defrauded! Call the big data!” Big data is only useful when it can be transformed into ‘smart data’. In other words, understanding the big picture of costly fraudulent activities is not akin to understanding the specifics of ‘who’ is defrauding you, and ‘how’ they are doing it.
Those questions can best be answered through the powerful data mining and link analysis software tools offered by Austin, TX based Crime Tech Solutions in partnership with Sterling, VA based Visallo. Effective link analysis complements big data analytics platforms, helping to expose previously undetected fraud, and the entities (people or organizations) committing it.
Link Analysis – Transforming big data into smart data
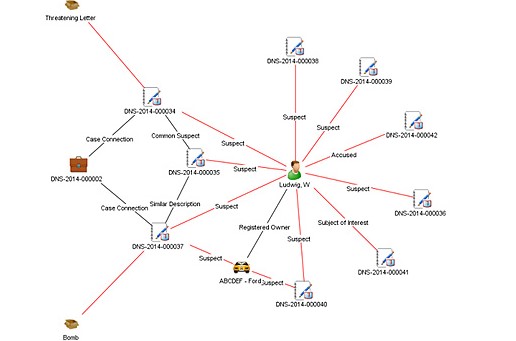
By definition, link analysis is a data analysis technique that examines relationships among people, places, and things. As a visual tool, link analysis provides users a powerful method to quickly understand and ‘see’ what is happening. Because of this, it is widely used by financial institutions such as banks and insurance companies to uncover criminal networks, improve fraud investigations, detect insider fraud, and expose money laundering schemes. Similarly, government agencies use link analysis to investigate fraud, enhance screening processes, uncover terrorist networks and investigate criminal activities.
At Crime Tech Solutions, we liken the question of how to detect and deter fraud to ‘How do you eat an elephant?’ The answer, of course, is one bite at a time. If big data is the elephant, comprehensive link analysis software is part of the one ‘bite’ at a time. Or should we say ‘byte’.
(NOTE: Crime Tech Solutions is an Austin, TX based provider of investigation software and analytics for commercial and law enforcement groups. We proudly support the Association of Certified Fraud Examiners (ACFE), International Association of Chiefs of Police (IACP), Association of Law Enforcement Intelligence Units (LEIU) and International Association of Crime Analysts (IACA). Our offerings include sophisticated link analysis software, an industry-leading investigation case management solution, and criminal intelligence database management systems.)
Insurance Fraud and Terrorist Financing – A bloody mix.
Published by Tyler Wood, Operations Manager at Crime Tech Solutions
December 7, 2015 – Nice post on LinkedIn today written by Aaron Denbo, Lead Trainer at Frauducate Counter-Fraud Academy…

The game has changed. Insurance Fraud isn’t the “quiet fraud” committed by otherwise “normal” people fudging a bit on their past driving experience, prior injuries, work status, or income. It is an $80 BILLION dollar a year problem and it funds and fuels organized crime rings, drug cartels, and terrorism. In a recent article by Christopher Tidball at PropertyCasualty360, “We’re seeing organized trans-national crime rings that are using insurance fraud as a vehicle to fund illegal activities.”
$80 BILLION is a lot of money. That’s a lot of well-funded death and destruction that can be bought and that’s just from the Insurance Fraud front.
That $80 BILLION also includes terrorism, which is more poignant than ever in the wake of both the Paris and the San Bernardino, California terrorist attacks. Combating insurance fraud – and fraud in general — has never been more important.
Now those of us who are counter-fraud professionals and have completed training in identifying, detecting, and investigating fraud and work fraud cases know that what we do is important. Your friends and family probably have a general understanding of what you do but have you connected your work to combating organized crime or terrorism? Have you thought of your work as part of a bigger piece that just might combat the next wave of terrorism? Have you thought of your fraud fighting in terms of making it so that some bad people with bad intentions might just not be able to make that extra explosive device because you disrupted their funding?
After San Bernardino, after Paris, after …. [insert next terror attack here]maybe we should think of ourselves not just as fraud fighters but also as disrupters and agitators to terror groups and organized crime rings. It is a change in awareness and mentality that I’m advocating here, an expansive sense of purpose. Terrorism Finance is more than just working Anti-Money Laundering cases now or leaving that to a problem that the banking sector has to face. It means our insurance fraud investigations are more than just money for our companies or agencies. It means we’re playing for keeps now.
__
Crime Tech Solutions delivers powerful link and social network analysis software to insurance companies to find hidden and suspicious connections between people, places, and things.
What is Link / Social Network Analysis?
Posted by Crime Tech Solutions
Some linkage data, such as telephone call detail records, may be simple but voluminous, with uniform node and link types and a great deal of regularity. Other data, such as law enforcement data, may be extremely rich and varied, though sparse, with elements possessing many attributes and confidence values that may change over time.
Various techniques are appropriate for distinct problems. For example, heuristic, localized methods might be appropriate for matching known patterns to a network of financial transactions in a criminal investigation. Efficient global search strategies, on the other hand, might be best for finding centrality or severability in a telephone network.
Link analysis can be broken down into two components—link generation, and utilization of the resulting linkage graph.
Link Generation
Link generation is the process of computing the links, link attributes and node attributes. There are several different ways to define links. The different approaches yield very different linkage graphs. A key aspect in defining a link analysis is deciding which representation to use.
Explicit Links
A link may be created between the nodes corresponding to each pair of entities in a transaction. For example, with a call detail record, a link is created between the originating telephone number and the destination telephone number. This is referred to as an explicit link.
Aggregate Links
A single link may be created from multiple transactions. For example, a single link could represent all telephone calls between two parties, and a link attribute might be the number of calls represented. Thus, several explicit links may be collapsed into a single aggregate link.
Inferred Relationships
Links may also be created between pairs of nodes based on inferred strengths of relationships between them. These are sometimes referred to as soft links, association links, or co-occurrence links. Classes of algorithms for these computations include association rules, Bayesian belief networks and context vectors. For example, a link may be created between any pair of nodes whose context vectors lie within a certain radius of one another. Typically, one attribute of such a link is the strength of the relationship it represents. Time is a key feature that offers an opportunity to uncover linkages that might be missed by more typical data analysis approaches. For example, suppose a temporal analysis of wire transfer records indicates that a transfer from account A to person X at one bank is temporally proximate to a transfer from account B to person Y at another bank. This yields an inferred link between accounts A and B. If other aspects of the accounts or transactions are also suspicious, they may be flagged for additional scrutiny for possible money laundering activity.
A specific instance of inferred relationships is identifying two nodes that may actually correspond to the same physical entity, such as a person or an account. Link analysis includes mechanisms for collapsing these to a single node. Typically, the analyst creates rules or selects parameters specifying in which instances to merge nodes in this fashion.
Utilization
Once a linkage graph, including the link and node attributes, has been defined, it can be browsed, searched or used to create variables as inputs to a decision system.
Visualization
In visualizing linking graphs, each node is represented as an icon, and each link is represented as a line or an arrow between two nodes. The node and link attributes may be displayed next to the items or accessed via mouse actions. Different icon types represent different entity types. Similarly, link attributes determine the link representation (line strength, line color, arrowhead, etc.).
Standard graphs include spoke and wheel, peacock, group, hierarchy and mesh. An analytic component of the visualization is the automatic positioning of the nodes on the screen, i.e., the projection of the graph onto a plane. Different algorithms position the nodes based on the strength of the links between nodes or to agglomerate the nodes into groups of the same kind. Once displayed, the user typically has the ability to move nodes, modify node and link attributes, zoom in, collapse, highlight, hide or delete portions of the graph.
Variable Creation
Link analysis can append new fields to existing records or create entirely new data sets for subsequent modeling stages in a decision system. For example, a new variable for a customer might be the total number of email addresses and credit card numbers linked to that customer.
Search
Link analysis query mechanisms include retrieving nodes and links matching specified criteria, such as node and link attributes, as well as search by example to find more nodes that are similar to the specified example node.
A more complex task is similarity search, also called clustering. Here, the objective is to find groups of similar nodes. These may actually be multiple instances of the same physical entity, such as a single individual using multiple accounts in a similar fashion.
Network Analysis
Network analysis is the search for parts of the linkage graph that play particular roles. It is used to build more robust communication networks and to combat organized crime. This exploration revolves around questions such as:
- Which nodes are key or central to the network?
- Which links can be severed or strengthened to most effectively impede or enhance the operation of the network?
- Can the existence of undetected links or nodes be inferred from the known data?
- Are there similarities in the structure of subparts of the network that can indicate an underlying relationship (e.g., modus operandi)?
- What are the relevant sub-networks within a much larger network?
- What data model and level of aggregation best reveal certain types of links and sub-networks?
- What types of structured groups of entities occur in the data set?
Applications
Link analysis tools such as those provided by Crime Tech Solutions are increasingly used in law enforcement investigations, detecting terrorist threats, fraud detection, detecting money laundering, telecommunications network analysis, classifying web pages, analyzing transportation routes, pharmaceuticals research, epidemiology, detecting nuclear proliferation and a host of other specialized applications. For example, in the case of money laundering, the entities might include people, bank accounts and businesses, and the transactions might include wire transfers, checks and cash deposits. Exploring relationships among these different objects helps expose networks of activity, both legal and illegal.