By Tyler Wood, Operations Manager at Crime Tech Solutions.
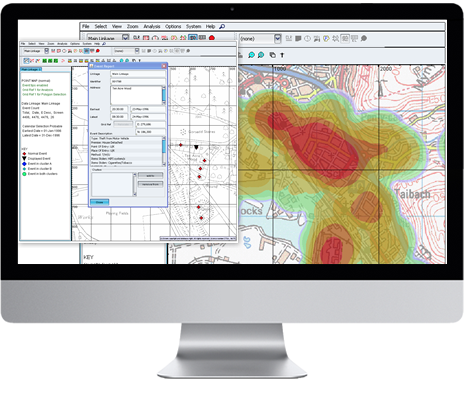
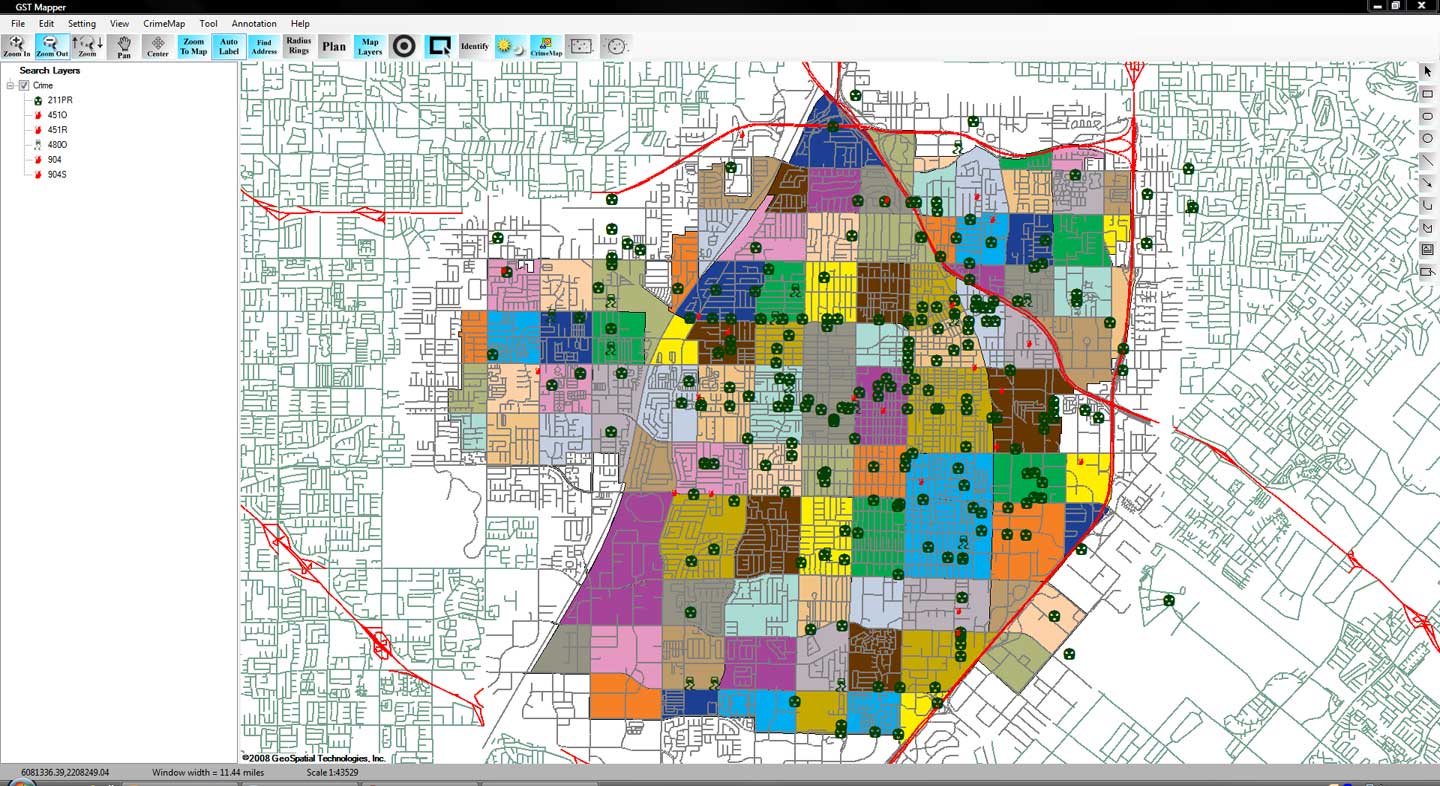
One of the many functions crime analysis performs is the identification of “hot spots”, or geographical areas that seem to be hubs for criminal activity. Identifying these hot spots through best practices in geospatial crime mapping allows law enforcement to focus their efforts in areas that need them most. The trouble that law enforcement and crime analysts have encountered is displacement – the fact that once a hot spot is “cleared”, crime seems to pop up again in a different location. The good news is that the displacement is never 100%, so policing hot spots is important – it’s just not a magic bullet.
To solve this problem, a team at Rutgers University’s School of Criminal Justice set out to develop new methodologies that would result in peaceful outcomes that are built to last instead of merely temporary.
The difference between the old approach and the new approach is stark. Where police and analysts used to focus solely on geographical concentration of crimes, Risk Terrain Modeling examines the factors that contribute to such dense concentrations to begin with. Rutgers team have identified several characteristics of any given geographical location which may attract or generate crime. Their technology takes these characteristics, which include socioeconomic data, physical layout, types of local businesses, etc… and uses them to calculate the likelihood crime occurring in the area. This allows law enforcement to be proactive in the prevention of crime in these areas.
The technique seems to be highly effective. After a trial run in New Haven, CT, police were able to identify sixteen “statistically significant risk factors that underlie violent crime occurrences.” A high percentage of violent crime in New Haven during the test period occurred in locations already identified by the concept of risk terrain modeling. Though the technology is still new, it is clearly showing impressive results already.
Shutting down hot spots is important policing, and risk terrain modeling technology allows analysts and law enforcement officers to be even more proactive in their prevention of crime.
The author, Tyler Wood, is head of operations at Austin, TX based Crime Tech Solutions – an innovator in crime analytics and law enforcement crime-fighting software. The clear price/performance leader for crime fighting software, the company’s offerings include sophisticated Case Closed™ investigative case management and major case management, GangBuster™ gang intelligence software, powerful link analysis software, evidence management, mobile applications for law enforcement, comprehensive crime analytics with mapping and predictive policing, and 28 CFR Part 23 compliant criminal intelligence database management systems.)
Tag Archives: mobile technology
Crime Tech Solutions Acquires Case Closed Software
June 1, 2016 (Austin, TX) Crime Tech Solutions, LLC, a leading provider of analytics and investigation software for law enforcement and commercial markets, today announced that it has acquired Cleveland, TN based Case Closed Software in a cash transaction. The terms of the deal were not released, but according to Crime Tech Solutions’ founder and president Douglas Wood, the acquisition brings together two dynamic and fast-growing software companies with an unparalleled complement of technologies.
“For Crime Tech Solutions, the opportunity to add Case Closed Software into the fold was too good to pass up” said Mr. Wood. “We think that the technology offered by Case Closed helps to further differentiate us in the market as the price performance leader for this type of investigative solution.”
Crime Tech Solutions, based in the city of Leander, TX, delivers advanced analytics and investigation software to commercial investigators and law enforcement agencies across the globe. Their solution suite includes criminal intelligence software, sophisticated crime analytics with geospatial mapping, and powerful link analysis and visualization software. The company says that the addition of Case Closed Software expands those offerings even further.
Case Closed Software develops and markets investigative case management software specifically designed for law enforcement agencies. The suite is built around four primary software products including best-in-class investigative case management software, property and evidence tracking, a gang database tool, and an integrated link analysis and data visualization tool. The company also plans to release the solution as Case Closed Cloud for cloud-based access.
“Case Closed couldn’t be happier than to be joining Crime Tech Solutions,” said Keith Weigand, the company’s founder. “The blending of our technologies creates a suite that will add tremendous value to our mutual customers, and will be hard for others to duplicate.”
According to both Mr. Weigand and Mr. Wood, the name Case Closed will continue on as the product brand, given its widespread popularity and loyal customer base. Crime Tech Solutions is expected to retain all Case Closed employees, with Mr. Weigand joining as the company’s chief technical officer.
Crime Tech Solutions says it expects continued growth via ongoing software sales and strategic acquisitions.
About Crime Tech Solutions
(NOTE: Crime Tech Solutions is an Austin, TX based provider of crime and fraud analytics software for commercial and law enforcement groups. Our offerings include sophisticated Case Closed™ investigative case management and major case management, GangBuster™ gang intelligence software, powerful link analysis software, evidence management, mobile applications for law enforcement, comprehensive crime analytics with mapping and predictive policing, and 28 CFR Part 23 compliant criminal intelligence database management systems.)
Biometrics and Authentication – A new world of possibilities
This article was written  by Sacha Breite, head of future payments at SIX Payment Services. It originally appeared here on July 20, 2015.
by Sacha Breite, head of future payments at SIX Payment Services. It originally appeared here on July 20, 2015.
The search for a common, international standard of payment authentication is in full flow.
Governments, retailers, banks and (not least) consumers are all eager to find a means of confirming someone’s identity beyond any doubt, secure from external hacking and technologically reliable.
The situation has become more urgent with the wildfire spread of mobile technology, opening up countless opportunities for remote transactions, but placing a growing burden on payment systems to prevent fraud and theft, both of assets and identities.
So, what are the best ways forward?
Here are some of the key technologies, with an analysis of their pros and cons:
Fingerprints and vein recognition
Already in common use at border controls and in many smartphones, fingerprint identification has become widely accepted. But concerns over its reliability and security has dissuaded banks from adopting it for payment authentication.
Some consumers fear that their fingerprint hashdata could be copied and used fraudulently, so they have switched back to pin ID. Younger consumers are more relaxed with the technology and ApplePay can be activated using fingerprint ID.
As technology develops and sensors are more widespread, some are concerned that their fingerprint ID could be captured simply by touching something, without realizing. The technology is likely to remain popular, but probably in combination with other forms of ID.
Facial recognition
Another border control technology which is likely to spread into the commercial world, this once again raises reliability concerns. What happens if one’s face alters its appearance? Can someone be impersonated by showing an image of their face?
A number of extra aspects can tighten security: infrared scanners can tell the difference between a live person and an image; a 3D scan of someone’s head provides further authentication; and iris recognition is becoming more sophisticated.
The new ‘Hello’ function on Windows 10 includes a means of unlocking one’s computer simply by looking at it. So the prospect of going to an ATM, looking at it and then getting cash out, may be possible in future (though some people will object to being filmed, on privacy grounds).
Customers taking ‘selfies’ and using these as authentication, either as a still image or a video, is another emerging form of authentication. Recently MasterCard announced plans to pilot this solution and replace passwords in 3-D Secure protected payments.
Heartbeats
Like our fingerprints and irises, everyone has a unique heartbeat. Using this for identification has the advantage that is it dynamic rather than static and therefore harder to replicate and proves that you are an actual human being.
The technology is part of many current and emerging devices, particularly for sports and fitness use, providing a ready means of integration with other systems, such as transactions or establishing ID.
Wearable technology, whether for health, fashion or communication, will give this type of authentication further impetus. So we can expect to see more of it in the years to come.
Beyond the technologies employed, there are further debates over whose responsibility it should be to develop any common standard. Governments are an obvious place to start, and indeed they have collaborated successfully to introduce border controls using biometric ID.
Yet transactions involving large amounts of money, especially ones using mobile devices, require greater security than this. People are physically present at border points and have to show their passports, so the biometrics are simply an additional security layer.
Most of the initiatives rolled out by governments using biometric ID authentication for health insurance (for example) have failed to work in the commercial sphere.
Card Schemes such as Visa and MasterCard would love to introduce such a system and have it commonly adopted internationally, since it would increase brand loyalty and probably win them new customers.
But so far, the lack of clarity over what kind of technology will be most widely accepted, by governments, consumers and by the legal world, has prevented any major financial service provider taking a leap of faith. Reliability, security and privacy issues remain unresolved.
In some ways, technology is leaping ahead of the best efforts of governments and banks, through applications like Google Street View and Google Image, where individuals can be identified through pictures taken of them without necessarily having their consent. And commercial services such as Amazon, PayPal and eBay have pioneered slimmed-down ID procedures, which may become more widely adopted.
An ever increasing amount of data is being stored on all of us, which will enable identification through many differing avenues. Irrespectively of the current position of biometrics and technology, it is vital for banking and payment infrastructure providers like SIX Payment Services, to provide high levels of security and reliability. In the near future we can expect further innovations to appear in this space, however it is still unclear which will form the basis of a single global standard, until the dust has settled from the current burst of activity.