June 1, 2016 (Austin, TX) Crime Tech Solutions, LLC, a leading provider of analytics and investigation software for law enforcement and commercial markets, today announced that it has acquired Cleveland, TN based Case Closed Software in a cash transaction. The terms of the deal were not released, but according to Crime Tech Solutions’ founder and president Douglas Wood, the acquisition brings together two dynamic and fast-growing software companies with an unparalleled complement of technologies.
“For Crime Tech Solutions, the opportunity to add Case Closed Software into the fold was too good to pass up” said Mr. Wood. “We think that the technology offered by Case Closed helps to further differentiate us in the market as the price performance leader for this type of investigative solution.”
Crime Tech Solutions, based in the city of Leander, TX, delivers advanced analytics and investigation software to commercial investigators and law enforcement agencies across the globe. Their solution suite includes criminal intelligence software, sophisticated crime analytics with geospatial mapping, and powerful link analysis and visualization software. The company says that the addition of Case Closed Software expands those offerings even further.
Case Closed Software develops and markets investigative case management software specifically designed for law enforcement agencies. The suite is built around four primary software products including best-in-class investigative case management software, property and evidence tracking, a gang database tool, and an integrated link analysis and data visualization tool. The company also plans to release the solution as Case Closed Cloud for cloud-based access.
“Case Closed couldn’t be happier than to be joining Crime Tech Solutions,” said Keith Weigand, the company’s founder. “The blending of our technologies creates a suite that will add tremendous value to our mutual customers, and will be hard for others to duplicate.”
According to both Mr. Weigand and Mr. Wood, the name Case Closed will continue on as the product brand, given its widespread popularity and loyal customer base. Crime Tech Solutions is expected to retain all Case Closed employees, with Mr. Weigand joining as the company’s chief technical officer.
Crime Tech Solutions says it expects continued growth via ongoing software sales and strategic acquisitions.
About Crime Tech Solutions
(NOTE: Crime Tech Solutions is an Austin, TX based provider of crime and fraud analytics software for commercial and law enforcement groups. Our offerings include sophisticated Case Closed™ investigative case management and major case management, GangBuster™ gang intelligence software, powerful link analysis software, evidence management, mobile applications for law enforcement, comprehensive crime analytics with mapping and predictive policing, and 28 CFR Part 23 compliant criminal intelligence database management systems.)
Tag Archives: insurance fraud
Insurance Fraud and Terrorist Financing – A bloody mix.
Published by Tyler Wood, Operations Manager at Crime Tech Solutions
December 7, 2015 – Nice post on LinkedIn today written by Aaron Denbo, Lead Trainer at Frauducate Counter-Fraud Academy…

The game has changed. Insurance Fraud isn’t the “quiet fraud” committed by otherwise “normal” people fudging a bit on their past driving experience, prior injuries, work status, or income. It is an $80 BILLION dollar a year problem and it funds and fuels organized crime rings, drug cartels, and terrorism. In a recent article by Christopher Tidball at PropertyCasualty360, “We’re seeing organized trans-national crime rings that are using insurance fraud as a vehicle to fund illegal activities.”
$80 BILLION is a lot of money. That’s a lot of well-funded death and destruction that can be bought and that’s just from the Insurance Fraud front.
That $80 BILLION also includes terrorism, which is more poignant than ever in the wake of both the Paris and the San Bernardino, California terrorist attacks. Combating insurance fraud – and fraud in general — has never been more important.
Now those of us who are counter-fraud professionals and have completed training in identifying, detecting, and investigating fraud and work fraud cases know that what we do is important. Your friends and family probably have a general understanding of what you do but have you connected your work to combating organized crime or terrorism? Have you thought of your work as part of a bigger piece that just might combat the next wave of terrorism? Have you thought of your fraud fighting in terms of making it so that some bad people with bad intentions might just not be able to make that extra explosive device because you disrupted their funding?
After San Bernardino, after Paris, after …. [insert next terror attack here]maybe we should think of ourselves not just as fraud fighters but also as disrupters and agitators to terror groups and organized crime rings. It is a change in awareness and mentality that I’m advocating here, an expansive sense of purpose. Terrorism Finance is more than just working Anti-Money Laundering cases now or leaving that to a problem that the banking sector has to face. It means our insurance fraud investigations are more than just money for our companies or agencies. It means we’re playing for keeps now.
__
Crime Tech Solutions delivers powerful link and social network analysis software to insurance companies to find hidden and suspicious connections between people, places, and things.
The Name Game Fraud
 Posted by Douglas Wood, Editor. Alright everybody, let’s play a game. The name game!
Posted by Douglas Wood, Editor. Alright everybody, let’s play a game. The name game!
“Shirley, Shirley bo Birley. Bonana fanna fo Firley. Fee fy mo Mirley. Shirley!” No, not THAT name game. (Admit it… you used to love singing the “Chuck” version, though.)
The name game I’m referring to is slightly more sinister, and relates to the criminal intent to deceive others for gain by slightly misrepresenting attributes in order to circumvent fraud detection techniques. Pretty much anywhere money, goods, or services are dispensed, folks play the name game.
Utilities, Insurance, Medicaid, retail, FEMA. You name it.
Several years ago, I helped a large online insurance provider determine the extent to which they were offering insurance policies to corporations and individuals with whom they specifically did not want to do business. Here’s what the insurer knew:
- They had standard application questions designed to both determine the insurance quote AND to ensure that they were not doing business with undesirables. These questions included things such as full name, address, telephone number, date of birth, etc… but also questions related to the insured property. “Do you live within a mile of a fire station?”, Does your home have smoke detectors?”, and “Is your house made of matchsticks?”
- On top of the questions, the insurer had a list of entities with whom the knew they did not want to do business for one reason or another. Perhaps Charlie Cheat had some previously questionable claims… he would have been on their list.
In order to circumvent the fraud prevention techniques, of course, the unscrupulous types figured out how to mislead the insurer just enough so that the policy was approved. Once approved, the car would immediately be stolen. The house would immediately burn down, etc.
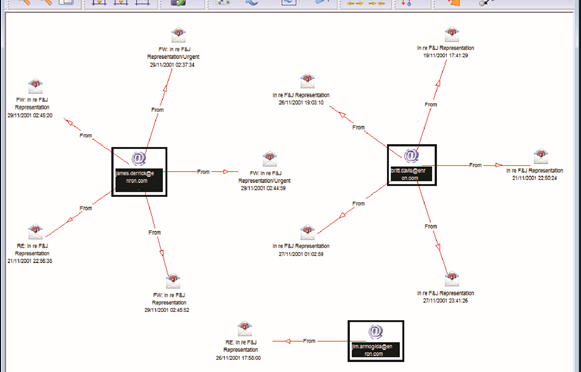
The most common way by which the fraudsters misled the insurers was a combination of The Name Game and modifying answers until the screening system was fooled. Through a combination of investigative case management and link analysis software, I went back and looked at several months of historical data and found some amazing techniques used by the criminals. Specifically, I found one customer who made 19 separate online applications – each time changing just one attribute or answer slightly – until the policy was issued. Within a week of the policy issue, a claim was made. You can use your imagination to determine if it was a legitimate claim. 😀
This customer, Charlie Cheat (obviously not his real name), first used his real name, address, telephone number, and date of birth… and answered all of the screening questions honestly. Because he did not meet the criteria AND appeared on an internal watch list for having suspicious previous claims, his application was automatically denied. Then he had his wife, Cheri Cheat, complete the application in hopes that the system would see a different name and approve the policy. Thirdly, he modified his name to Charlie Cheat, Chuck E. Cheat, and so on. Still no go. His address went from 123 Fifth Street to 123-A 5th Street. You get the picture.
Then he began to modify answers to the screening questions. All of a sudden, he DID live within a mile of a fire station… and his house was NOT made of matchsticks… and was NOT located next door to a fireworks factory. After almost two dozen attempts, he was finally issued the policy under a slightly revised name, a tweak in his address, and some less-than-truthful answers on the screening page. By investing in powerful investigative case management software with link analysis and fuzzy matching this insurer was able to dramatically decrease the number of policies issued to known fraudsters or otherwise ineligible entities.
Every time a new policy is applied for, the system analyzes the data against previous responses and internal watch lists in real time. In other words, Charlie and Cheri just found it a lot more difficult to rip this insurer off. These same situations occur in other arenas, costing us millions annually in increased taxes and prices. So, what happened to the Cheats after singing the name game?
Let’s just say that after receiving a letter from the insurer, Charlie and Cheri started singing a different tune altogether.
Using Link Analysis to untangle fraud webs
Posted by Douglas Wood, Editor.
NOTE: This article originally appeared HERE by Jane Antonio. I think it’s a great read…
Link analysis has become an important technique for discovering hidden relationships involved in healthcare fraud. An excellent online source, FierceHealthPayer:AntiFraud, recently spoke to Vincent Boyd Bryant about the value of this tool for payer special investigations units.
A former biometric scientist for the U.S. Department of Defense, Bryant has 30 years of experience in law enforcement and intelligence analysis. He’s an internationally-experienced investigations and forensics expert who’s worked for a leading health insurer on government business fraud and abuse cases.
How does interactive link analysis help insurers prevent healthcare fraud? Can you share an example of how the tool works?
One thing criminals do best is hide pots of money in different places. As a small criminal operation becomes successful, it will often expand its revenue streams through associated businesses. Link analysis is about trying to figure out where all those different baskets of revenue may be. Insurers are drowning in a sea of theft. Here’s where link analysis becomes beneficial. Once insurers discover a small basket of money lost to a criminal enterprise, then serious research needs to go into finding out who owns the company, who they’re associated with, what kinds of business they’re doing and if there are claims associated with it.
You may find a clinic, for example, connected to and working near a pharmacy, a medical equipment supplier, a home healthcare services provider and a construction company. Diving into those companies and what they do, you find that they’re serving older patients for whom multiple claims from many providers exist. The construction company may be building wheelchair ramps on homes. And you may find that the providers are claiming payment for dead people. Overall, using this tool requires significant curiosity and a willingness to look beyond the obvious.
Any investigation consists of aggregating facts, generating impressions and creating a theory about what happened. Then you work to confirm or disconfirm your theory. It’s important to have tools that let you take large masses of facts and visualize them in ways that cue you to look closer.
Let’s say you investigate a large medical practice and interview “Doctor Jones.” The day after the interview, you learn through link analysis that he transferred $11 million from his primary bank account to the Cayman Islands. And in looking at Dr. Jones’ phone records, you see he called six people, each of whom was the head of another individual practice on whose board Dr. Jones sits. Now the investigation expands, since the timing of those phone calls was contemporaneous to the money taking flight.
Why are tight clusters of similar entities possible indicators of fraud, waste or abuse?
Bryant: When you find a business engaged in dishonest practices and see its different relationships with providers working out of the same building, this gives rise to reasonable suspicion. The case merits a closer look. Examining claims and talking to members served by those companies will give you an indication of how legitimate the operation is.
What are the advantages of link analysis to payer special investigation units, and how are SIUs using its results?
Bryant: Link analysis can define relationships through data insurers haven’t always had, data that traditionally belonged to law enforcement.
Link analysis results in a visual reference that can take many forms: It can look like a family tree, an organizational chart or a time line. This reference helps investigators assess large masses of data for clustering and helps them arrive at a conclusion more rapidly.
Using link analysis, an investigator can dump in large amounts of data–such as patient lists from multiple practices–and see who’s serving the same patient. This can identify those who doctor shop for pain medication, for example. Link analysis can chart where this person was and when, showing the total amount of medication prescribed and giving you an idea of how the person is operating.
What types of data does link analysis integrate?
Bryant: Any type of data that can be sorted and tied together can be loaded into the tool. Examples include telephone records, addresses, vehicle information, corporate records that list individuals serving on boards and banking and financial information. Larger supporting documents can be loaded and linked to the charts, making cases easier to present to a jury.
Linked analysis can pull in data from state government agencies, county tax records or police records from state departments of correction and make those available in one bucket. In most cases, this is more efficient than the hours of labor needed to dig up these types of public records through site visits.
Is there anything else payers should know about link analysis that wasn’t covered in the above questions?
Bryant: The critical thing is remembering that you don’t know what you don’t know. If a provider or member is stealing from the plan in what looks like dribs and drabs, insurers may never discover the true extent of the losses. But if–as a part of any fraud allegation that arises–you look at what and who is associated with the subject of the complaint, what started as a $100,000 questionable claims allegation can expose millions of dollars in inappropriate billings spread across different entities.
Premium Fraud – Piano Tuners and Window Washers?
Posted by Douglas Wood, Editor.
I came across a news article earlier this week regarding a business owner convicted of fraudulently avoiding worker’s compensation premiums. The link to that news article is below.
It brought to mind some fascinating work I was involved with a few years ago to help a state run Worker’s Compensation Bureau more effectively detect this kind of fraud. Their biggest concern was recovering monies owed by companies who illegally misrepresent themselves for the purpose of reducing or avoiding the payment of premiums. Here’s how these scams work…
Intentional Misclassification: A crooked business claims that employees work safer jobs than they really do. Perhaps a high-rise window washer is falsely classified as a piano tuner. Much lower premiums, obviously.
Employee Misrepresentation: A business says it has fewer employees or a lower payroll than it actually does.
Coverage Avoidance/Experience Modification: A business simply doesn’t buy the required insurance, hoping state officials won’t notice. If the state learns of the avoidance, the company will simply close, then re-emerge as a ‘new’ company’ in order to avoid the payments.
So the state bureau I worked with needed to understand when, for example, a ‘piano tuner’ was requesting a permit for high rise window washing. Red flag, right? Or when an five separate claims were filed by employees of a company who stated they had only 3 employees. Another red flag.
Oh, and what about a new company registrant whose owners, address, telephone number, and line of business are all suspiciously similar to those of a recently closed business who owed thousands of dollars in back premiums. BIG red flag.
The state itself had all of the data it needed to detect this fraud. The problem, as is often the case, is that the data sat in different jurisdictions. Working with our client, we helped those other jurisdictions – Business Registrations, Building Permits, Tax Departments, etc. – understand the value of sharing that data. That’s the key to this success story – data sharing. Without it, problems are much more difficult to solve.
Ultimately, we delivered a system that included business rules, anomaly detection, and social network analysis. It provided the bureau with the ability to flag those anomalies using their existing data infrastructure and fraud alert output from those other state agencies.
With the tools in place to trigger those red flags, the agency immediately began recovering lost premiums, prosecuting offenders, and ultimately adding much needed revenue to the state coffers.
Fraudsters who choose to commit financial crimes are always coming up with new scams. Those of us committed to delivering true technology innovations through data sharing are starting to put a real dent in their chosen profession, though.
Maybe they can tune pianos instead. Do they need a building permit for that?
http://www.workerscompensation.com/compnewsnetwork/mobile/news/17511-investigation-leads-to-conviction-of-ca-business-owner-for-insurance-fraud.htmlgus
Posted by Douglas G. Wood. Click on ABOUT for more information and follow Financial Crimes Weekly on Twitter @FightFinCrime