Posted by Douglas Wood, Editor.
NOTE: This article originally appeared HERE by Jane Antonio. I think it’s a great read…
Link analysis has become an important technique for discovering hidden relationships involved in healthcare fraud. An excellent online source, FierceHealthPayer:AntiFraud, recently spoke to Vincent Boyd Bryant about the value of this tool for payer special investigations units.
A former biometric scientist for the U.S. Department of Defense, Bryant has 30 years of experience in law enforcement and intelligence analysis. He’s an internationally-experienced investigations and forensics expert who’s worked for a leading health insurer on government business fraud and abuse cases.
How does interactive link analysis help insurers prevent healthcare fraud? Can you share an example of how the tool works?
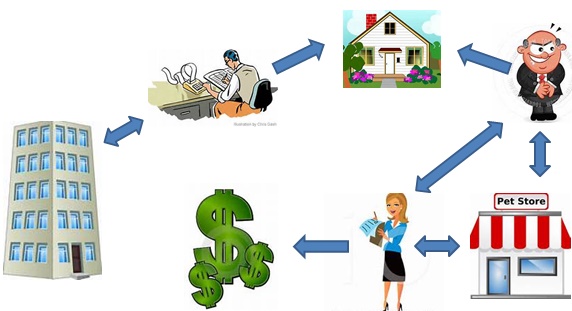
Boyd Bryant: Link analysis is most often used to piece together different kinds of data from multiple sources–to identify key players, connections between those players and patterns of behavior frequently missed. It can simplify an understanding of the level of involvement of individuals and criminal organizational hierarchies and can greatly simplify visualizing and communicating the operations of complex criminal enterprises.
One thing criminals do best is hide pots of money in different places. As a small criminal operation becomes successful, it will often expand its revenue streams through associated businesses. Link analysis is about trying to figure out where all those different baskets of revenue may be. Insurers are drowning in a sea of theft. Here’s where link analysis becomes beneficial. Once insurers discover a small basket of money lost to a criminal enterprise, then serious research needs to go into finding out who owns the company, who they’re associated with, what kinds of business they’re doing and if there are claims associated with it.
You may find a clinic, for example, connected to and working near a pharmacy, a medical equipment supplier, a home healthcare services provider and a construction company. Diving into those companies and what they do, you find that they’re serving older patients for whom multiple claims from many providers exist. The construction company may be building wheelchair ramps on homes. And you may find that the providers are claiming payment for dead people. Overall, using this tool requires significant curiosity and a willingness to look beyond the obvious.
Any investigation consists of aggregating facts, generating impressions and creating a theory about what happened. Then you work to confirm or disconfirm your theory. It’s important to have tools that let you take large masses of facts and visualize them in ways that cue you to look closer.
Let’s say you investigate a large medical practice and interview “Doctor Jones.” The day after the interview, you learn through link analysis that he transferred $11 million from his primary bank account to the Cayman Islands. And in looking at Dr. Jones’ phone records, you see he called six people, each of whom was the head of another individual practice on whose board Dr. Jones sits. Now the investigation expands, since the timing of those phone calls was contemporaneous to the money taking flight.
Why are tight clusters of similar entities possible indicators of fraud, waste or abuse?
Bryant: When you find a business engaged in dishonest practices and see its different relationships with providers working out of the same building, this gives rise to reasonable suspicion. The case merits a closer look. Examining claims and talking to members served by those companies will give you an indication of how legitimate the operation is.
What are the advantages of link analysis to payer special investigation units, and how are SIUs using its results?
Bryant: Link analysis can define relationships through data insurers haven’t always had, data that traditionally belonged to law enforcement.
Link analysis results in a visual reference that can take many forms: It can look like a family tree, an organizational chart or a time line. This reference helps investigators assess large masses of data for clustering and helps them arrive at a conclusion more rapidly.
Using link analysis, an investigator can dump in large amounts of data–such as patient lists from multiple practices–and see who’s serving the same patient. This can identify those who doctor shop for pain medication, for example. Link analysis can chart where this person was and when, showing the total amount of medication prescribed and giving you an idea of how the person is operating.
What types of data does link analysis integrate?
Bryant: Any type of data that can be sorted and tied together can be loaded into the tool. Examples include telephone records, addresses, vehicle information, corporate records that list individuals serving on boards and banking and financial information. Larger supporting documents can be loaded and linked to the charts, making cases easier to present to a jury.
Linked analysis can pull in data from state government agencies, county tax records or police records from state departments of correction and make those available in one bucket. In most cases, this is more efficient than the hours of labor needed to dig up these types of public records through site visits.
Is there anything else payers should know about link analysis that wasn’t covered in the above questions?
Bryant: The critical thing is remembering that you don’t know what you don’t know. If a provider or member is stealing from the plan in what looks like dribs and drabs, insurers may never discover the true extent of the losses. But if–as a part of any fraud allegation that arises–you look at what and who is associated with the subject of the complaint, what started as a $100,000 questionable claims allegation can expose millions of dollars in inappropriate billings spread across different entities.


 Unless you’ve been hiding under a big red nose and novelty wig, you probably know that there has been a rash of ‘creepy clown’ sightings in communities across the country. These creepy clowns – and the related threats they seem to pose – seem to range from crazy hoaxes to credible events. So what in the name of big, floppy shoes is going on here?
Unless you’ve been hiding under a big red nose and novelty wig, you probably know that there has been a rash of ‘creepy clown’ sightings in communities across the country. These creepy clowns – and the related threats they seem to pose – seem to range from crazy hoaxes to credible events. So what in the name of big, floppy shoes is going on here?
 Perhaps the biggest concern is that these creepy clowns take it too far, a la the snowball effect. We should be concerned that someone could be legitimately hurt as the trend grows. It’s even more possible that someone will take one of these creepy clowns as a legitimate threat and take matters into their own hands. We hope neither of those things happen, but we’d sure love to see a lot less of this clowning around.
Perhaps the biggest concern is that these creepy clowns take it too far, a la the snowball effect. We should be concerned that someone could be legitimately hurt as the trend grows. It’s even more possible that someone will take one of these creepy clowns as a legitimate threat and take matters into their own hands. We hope neither of those things happen, but we’d sure love to see a lot less of this clowning around.