Re-posted by Crime Tech Solutions – Your Source for Investigation Software
It’s “precrime” meets “thoughtcrime.” China is using its substantial surveillance apparatus as the basis for a “unified information environment” that will allow authorities to profile individual citizens based upon their online behaviors, financial transactions, where they go, and who they see. The authorities are watching for deviations from the norm that might indicate someone is involved in suspicious activity. And they’re doing it with a hand from technology pioneered in the US.
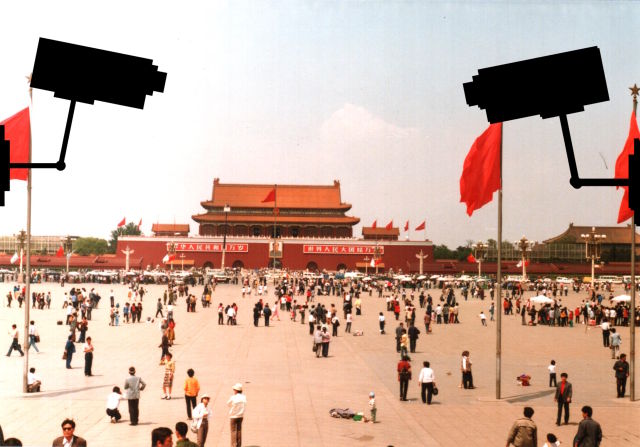 As Defense One’s Patrick Tucker reports, the Chinese government is leveraging “predictive policing” capabilities that have been used by US law enforcement, and it has funded research into machine learning and other artificial intelligence technologies to identify human faces in surveillance video. The Chinese government has also used this technology to create a “Situation-Aware Public Security Evaluation (SAPE) platform” that predicts “security events” based on surveillance data, which includes anything from actual terrorist attacks to large gatherings of people.
As Defense One’s Patrick Tucker reports, the Chinese government is leveraging “predictive policing” capabilities that have been used by US law enforcement, and it has funded research into machine learning and other artificial intelligence technologies to identify human faces in surveillance video. The Chinese government has also used this technology to create a “Situation-Aware Public Security Evaluation (SAPE) platform” that predicts “security events” based on surveillance data, which includes anything from actual terrorist attacks to large gatherings of people.
The Chinese government has plenty of data to feed into such systems. China invested heavily in building its surveillance capabilities in major cities over the past five years, with spending on “domestic security and stability” surpassing China’s defense budget—and turning the country into the biggest market for security technology. And in December, China’s government gained a new tool in surveillance: anti-terrorism laws giving the government even more surveillance powers and requiring any technology companies doing business in China to provide assistance in that surveillance.
The law states that companies “shall provide technical interfaces, decryption and other technical support and assistance to public security and state security agencies when they are following the law to avert and investigate terrorist activities”—in other words, the sort of “golden key” that FBI Director James Comey has lobbied for in the US. For obvious reasons, the Chinese government is particularly interested in the outcome of the current legal confrontation between the FBI and Apple over the iPhone used by Syed Farook.
Bloomberg reports that China is harnessing all that data in an effort to perform behavioral prediction at an individual level—tasking the state-owned defense contractor China Electronics Technology Group to develop software that can sift through the online activities, financial transactions, work data, and other behavioral data of citizens to predict which will perform “terrorist” acts. The system could watch for unexpected transfers of money, calls overseas by individuals with no relatives outside the country, and other trigger events that might indicate they were plotting an illegal action. China’s definition of “terrorism” is more expansive than that of many countries.
At a news conference in December, China Electronics Technology Group Chief Engineer Wu Manqing told reporters, “We don’t call it a big data platform, but a united information environment… It’s very crucial to examine the cause after an act of terror, but what is more important is to predict the upcoming activities.”
__
(NOTE: Crime Tech Solutions is an Austin, TX based provider of crime and fraud analytics software for commercial and law enforcement groups. We proudly support the Association of Certified Fraud Examiners (ACFE), International Association of Chiefs of Police (IACP), Association of Law Enforcement Intelligence Units (LEIU) and International Association of Crime Analysts (IACA). Our offerings include sophisticated link analysis software, comprehensive crime analytics with mapping and predictive policing, and criminal intelligence database management systems.)
Tag Archives: fraud technology
Link Analysis and Crime – An examination.
Posted by Tyler Wood, Operations Manager at Crime Tech Solutions
 The topic of fraud is widely discussed, and the focus of thousands upon thousands of articles. Television shows such as Crime, Inc and American Greed have become popular due, in part, to our fascination with the topic of fraud.
The topic of fraud is widely discussed, and the focus of thousands upon thousands of articles. Television shows such as Crime, Inc and American Greed have become popular due, in part, to our fascination with the topic of fraud.
The organizations that are affected by fraud are also fascinated… but for entirely different reasons. Some estimates suggest that the US economy loses 11 trillion dollars each year due to one form of fraud or another. It’s little wonder, therefore, that the companies most frequently defrauded have been heavily investing in anti-fraud technologies at an increasing rate over the past decade or more.
The biggest problem with fraud, of course, is that it is always evolving in a very Darwinian fashion. Like a living, breathing entity, fraud schemes change over time in order to survive. As the targets of fraud schemes put new policies, procedures and/or systems to deter the activities, the schemes modify and find new ways to survive.
So, since the nature of criminal activity is such that they constantly change, how do investigators find a fool proof methodology to ensure they are 100% safe from them? The answer, of course, is that they can’t. They never will; at least not until we live in a world such as the one depicted in the 2002 film Minority Report, starring Tom Cruise. In that movie, criminals are arrested prior to committing a crime based upon the predictions of psychics called ‘Precogs’. Corporations and individual targets of fraud can only wish.
Nope, there are no Precogs running around locking up would-be practitioners of fraud that would protect banks, insurance companies, Medicaid and Medicare programs, victims of Ponzi schemes, victims of identity theft, and countless others. Instead, organizations rely upon skilled knowledge workers using purpose-built crime and fraud analytics technology that can detect anomalies in patterns, suspicious transactions, hotspot mapping, networks of fraudsters, and other sophisticated data analytics tools.
Crime and fraud analytics
Any discussion of analytics and investigation software must touch upon the topic of ‘big data’. No longer just a buzz word, big data literally fuels the insights gathered by organizations in every area of business. Naturally, then, organizations who have been traditionally targeted by fraudsters have increasingly invested in crime technology such as investigation software and analytics in order to exploit the phenomenon.
 Of course, big data in and by itself does nothing. It just sits there. Nobody has ever yelled “Help! We’ve been defrauded! Call the big data!” Big data is only useful when it can be transformed into ‘smart data’. In other words, understanding the big picture of costly fraudulent activities is not akin to understanding the specifics of ‘who’ is defrauding you, and ‘how’ they are doing it.
Of course, big data in and by itself does nothing. It just sits there. Nobody has ever yelled “Help! We’ve been defrauded! Call the big data!” Big data is only useful when it can be transformed into ‘smart data’. In other words, understanding the big picture of costly fraudulent activities is not akin to understanding the specifics of ‘who’ is defrauding you, and ‘how’ they are doing it.
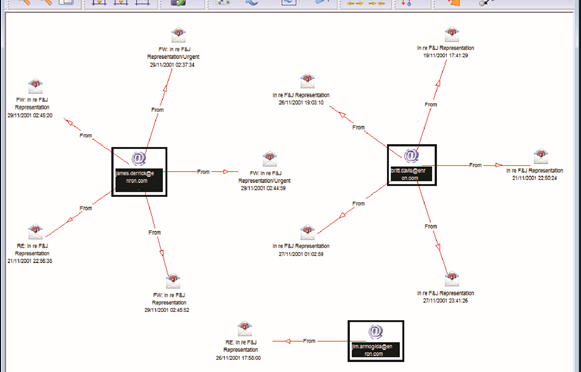
Those questions can best be answered through the powerful data mining and link analysis software tools offered by Austin, TX based Crime Tech Solutions in partnership with Sterling, VA based Visallo. Effective link analysis complements big data analytics platforms, helping to expose previously undetected fraud, and the entities (people or organizations) committing it.
Link Analysis – Transforming big data into smart data
By definition, link analysis is a data analysis technique that examines relationships among people, places, and things. As a visual tool, link analysis provides users a powerful method to quickly understand and ‘see’ what is happening. Because of this, it is widely used by financial institutions such as banks and insurance companies to uncover criminal networks, improve fraud investigations, detect insider fraud, and expose money laundering schemes. Similarly, government agencies use link analysis to investigate fraud, enhance screening processes, uncover terrorist networks and investigate criminal activities.
At Crime Tech Solutions, we liken the question of how to detect and deter fraud to ‘How do you eat an elephant?’ The answer, of course, is one bite at a time. If big data is the elephant, comprehensive link analysis software is part of the one ‘bite’ at a time. Or should we say ‘byte’.
(NOTE: Crime Tech Solutions is an Austin, TX based provider of investigation software and analytics for commercial and law enforcement groups. We proudly support the Association of Certified Fraud Examiners (ACFE), International Association of Chiefs of Police (IACP), Association of Law Enforcement Intelligence Units (LEIU) and International Association of Crime Analysts (IACA). Our offerings include sophisticated link analysis software, an industry-leading investigation case management solution, and criminal intelligence database management systems.)
Professor urges increased use of technology in fighting crime
 Posted by Crime Tech Solutions
Posted by Crime Tech Solutions
This article originally appeared HERE in Jamaica Observer. It’s an interesting read…
A University of the West Indies (UWI) professor is calling for the increased use of technology by developing countries, including Jamaica, to assist in the fight against crime.
Professor Evan Duggan, who is Dean of the Faculty of Social Sciences, said there have been “amazing advancements” in information and communications technologies (ICT), over the past six decades, which offer great potential for improving security strategies.
The academic, who was addressing a recent National Security Policy Seminar at UWI’s Regional Headquarters, located on the Mona campus, pointed to Kenya as a developing country that has employed the use of inexpensive technology in its crime fighting initiatives.
“Potential applications and innovations have been implemented through the use of powerful but not very expensive technologies that have allowed law enforcers to make enormous leaps in criminal intelligence, crime analysis, emergency response and policing,” he said.
He pointed to the use of a variety of mobile apps for crime prevention and reporting, web facilities, and citizen portals for the reporting of criminal activity.
Professor Duggan said that in order for Jamaica to realise the full benefit of technology in crime fighting, national security stakeholders need to engage local application developers.
“I would enjoin our stakeholders to engage the extremely creative Jamaican application developers, who now produce high quality apps for a variety of mobile and other platforms. I recommend interventions to assist in helping these groups to cohere into a unified force that is more than capable of supplying the applications we need,” he urged.
The UWI Professor pointed to the Mona Geoinformatic Institute as one entity that has been assisting in fighting crime, through analyses of crime data as well as three dimensional (3D) reconstruction of crime scenes; and mapping jurisdictional boundaries for police posts and divisions, as well as the movement of major gangs across the country.
In the meantime, Professor Duggan called for “purposeful activism” in the fight against crime and lawlessness which, he said, are “serious deterrents to economic development and national growth prospects” and could derail the national vision of developed country status by 2030.
“In the current global landscape where security challenges are proliferating across borders and have taken on multifaceted physiognomies, all hands on deck are vital,” he stressed.
“We need to …consolidate pockets of research excellence in this area …to provide the kinds of insight that will lead to more fruitful and productive collaborative engagements that are required to help us better understand the security challenges and threats from crime in order to better inform our national security architecture and direction,” he added.
Biometrics and Authentication – A new world of possibilities
This article was written  by Sacha Breite, head of future payments at SIX Payment Services. It originally appeared here on July 20, 2015.
by Sacha Breite, head of future payments at SIX Payment Services. It originally appeared here on July 20, 2015.
The search for a common, international standard of payment authentication is in full flow.
Governments, retailers, banks and (not least) consumers are all eager to find a means of confirming someone’s identity beyond any doubt, secure from external hacking and technologically reliable.
The situation has become more urgent with the wildfire spread of mobile technology, opening up countless opportunities for remote transactions, but placing a growing burden on payment systems to prevent fraud and theft, both of assets and identities.
So, what are the best ways forward?
Here are some of the key technologies, with an analysis of their pros and cons:
Fingerprints and vein recognition
Already in common use at border controls and in many smartphones, fingerprint identification has become widely accepted. But concerns over its reliability and security has dissuaded banks from adopting it for payment authentication.
Some consumers fear that their fingerprint hashdata could be copied and used fraudulently, so they have switched back to pin ID. Younger consumers are more relaxed with the technology and ApplePay can be activated using fingerprint ID.
As technology develops and sensors are more widespread, some are concerned that their fingerprint ID could be captured simply by touching something, without realizing. The technology is likely to remain popular, but probably in combination with other forms of ID.
Facial recognition
Another border control technology which is likely to spread into the commercial world, this once again raises reliability concerns. What happens if one’s face alters its appearance? Can someone be impersonated by showing an image of their face?
A number of extra aspects can tighten security: infrared scanners can tell the difference between a live person and an image; a 3D scan of someone’s head provides further authentication; and iris recognition is becoming more sophisticated.
The new ‘Hello’ function on Windows 10 includes a means of unlocking one’s computer simply by looking at it. So the prospect of going to an ATM, looking at it and then getting cash out, may be possible in future (though some people will object to being filmed, on privacy grounds).
Customers taking ‘selfies’ and using these as authentication, either as a still image or a video, is another emerging form of authentication. Recently MasterCard announced plans to pilot this solution and replace passwords in 3-D Secure protected payments.
Heartbeats
Like our fingerprints and irises, everyone has a unique heartbeat. Using this for identification has the advantage that is it dynamic rather than static and therefore harder to replicate and proves that you are an actual human being.
The technology is part of many current and emerging devices, particularly for sports and fitness use, providing a ready means of integration with other systems, such as transactions or establishing ID.
Wearable technology, whether for health, fashion or communication, will give this type of authentication further impetus. So we can expect to see more of it in the years to come.
Beyond the technologies employed, there are further debates over whose responsibility it should be to develop any common standard. Governments are an obvious place to start, and indeed they have collaborated successfully to introduce border controls using biometric ID.
Yet transactions involving large amounts of money, especially ones using mobile devices, require greater security than this. People are physically present at border points and have to show their passports, so the biometrics are simply an additional security layer.
Most of the initiatives rolled out by governments using biometric ID authentication for health insurance (for example) have failed to work in the commercial sphere.
Card Schemes such as Visa and MasterCard would love to introduce such a system and have it commonly adopted internationally, since it would increase brand loyalty and probably win them new customers.
But so far, the lack of clarity over what kind of technology will be most widely accepted, by governments, consumers and by the legal world, has prevented any major financial service provider taking a leap of faith. Reliability, security and privacy issues remain unresolved.
In some ways, technology is leaping ahead of the best efforts of governments and banks, through applications like Google Street View and Google Image, where individuals can be identified through pictures taken of them without necessarily having their consent. And commercial services such as Amazon, PayPal and eBay have pioneered slimmed-down ID procedures, which may become more widely adopted.
An ever increasing amount of data is being stored on all of us, which will enable identification through many differing avenues. Irrespectively of the current position of biometrics and technology, it is vital for banking and payment infrastructure providers like SIX Payment Services, to provide high levels of security and reliability. In the near future we can expect further innovations to appear in this space, however it is still unclear which will form the basis of a single global standard, until the dust has settled from the current burst of activity.
The Name Game Fraud
 Posted by Douglas Wood, Editor. Alright everybody, let’s play a game. The name game!
Posted by Douglas Wood, Editor. Alright everybody, let’s play a game. The name game!
“Shirley, Shirley bo Birley. Bonana fanna fo Firley. Fee fy mo Mirley. Shirley!” No, not THAT name game. (Admit it… you used to love singing the “Chuck” version, though.)
The name game I’m referring to is slightly more sinister, and relates to the criminal intent to deceive others for gain by slightly misrepresenting attributes in order to circumvent fraud detection techniques. Pretty much anywhere money, goods, or services are dispensed, folks play the name game.
Utilities, Insurance, Medicaid, retail, FEMA. You name it.
Several years ago, I helped a large online insurance provider determine the extent to which they were offering insurance policies to corporations and individuals with whom they specifically did not want to do business. Here’s what the insurer knew:
- They had standard application questions designed to both determine the insurance quote AND to ensure that they were not doing business with undesirables. These questions included things such as full name, address, telephone number, date of birth, etc… but also questions related to the insured property. “Do you live within a mile of a fire station?”, Does your home have smoke detectors?”, and “Is your house made of matchsticks?”
- On top of the questions, the insurer had a list of entities with whom the knew they did not want to do business for one reason or another. Perhaps Charlie Cheat had some previously questionable claims… he would have been on their list.
In order to circumvent the fraud prevention techniques, of course, the unscrupulous types figured out how to mislead the insurer just enough so that the policy was approved. Once approved, the car would immediately be stolen. The house would immediately burn down, etc.
The most common way by which the fraudsters misled the insurers was a combination of The Name Game and modifying answers until the screening system was fooled. Through a combination of investigative case management and link analysis software, I went back and looked at several months of historical data and found some amazing techniques used by the criminals. Specifically, I found one customer who made 19 separate online applications – each time changing just one attribute or answer slightly – until the policy was issued. Within a week of the policy issue, a claim was made. You can use your imagination to determine if it was a legitimate claim. 😀
This customer, Charlie Cheat (obviously not his real name), first used his real name, address, telephone number, and date of birth… and answered all of the screening questions honestly. Because he did not meet the criteria AND appeared on an internal watch list for having suspicious previous claims, his application was automatically denied. Then he had his wife, Cheri Cheat, complete the application in hopes that the system would see a different name and approve the policy. Thirdly, he modified his name to Charlie Cheat, Chuck E. Cheat, and so on. Still no go. His address went from 123 Fifth Street to 123-A 5th Street. You get the picture.
Then he began to modify answers to the screening questions. All of a sudden, he DID live within a mile of a fire station… and his house was NOT made of matchsticks… and was NOT located next door to a fireworks factory. After almost two dozen attempts, he was finally issued the policy under a slightly revised name, a tweak in his address, and some less-than-truthful answers on the screening page. By investing in powerful investigative case management software with link analysis and fuzzy matching this insurer was able to dramatically decrease the number of policies issued to known fraudsters or otherwise ineligible entities.
Every time a new policy is applied for, the system analyzes the data against previous responses and internal watch lists in real time. In other words, Charlie and Cheri just found it a lot more difficult to rip this insurer off. These same situations occur in other arenas, costing us millions annually in increased taxes and prices. So, what happened to the Cheats after singing the name game?
Let’s just say that after receiving a letter from the insurer, Charlie and Cheri started singing a different tune altogether.
Investigating the Investigations.
Posted by Douglas Wood, Editor.
A few years ago, I read a book called Fraud Analytics by Delena Spann. Ms. Spann is with the U.S. Secret Service, Electronic & Financial Crimes Task Force. The book is an overview of investigation analytics with specific information about some former technology leaders in this area.
The IBM i2 toolset is discussed, along with offerings from Raytheon, Centrifuge, and SAS, and FMS’ Link Analytics, and others. (My friend Chris Westphal, formerly of Raytheon Visual Analytics, by the way, published his book ‘Data Mining for Intelligence, Fraud & Criminal Detection’ a few years ago and is another one I strongly recommend.)
Both books offer advice and use cases on how technology can be applied in the fight against crime. A few months ago, I summarized the types of technology being put to use as tools to prevent, detect, and investigate fraud and other criminal activities. (It’s worth a quick read.) What I’m investigating today, however, is… well, investigations.
“IMA is the most critical connection between technology and investigators.”
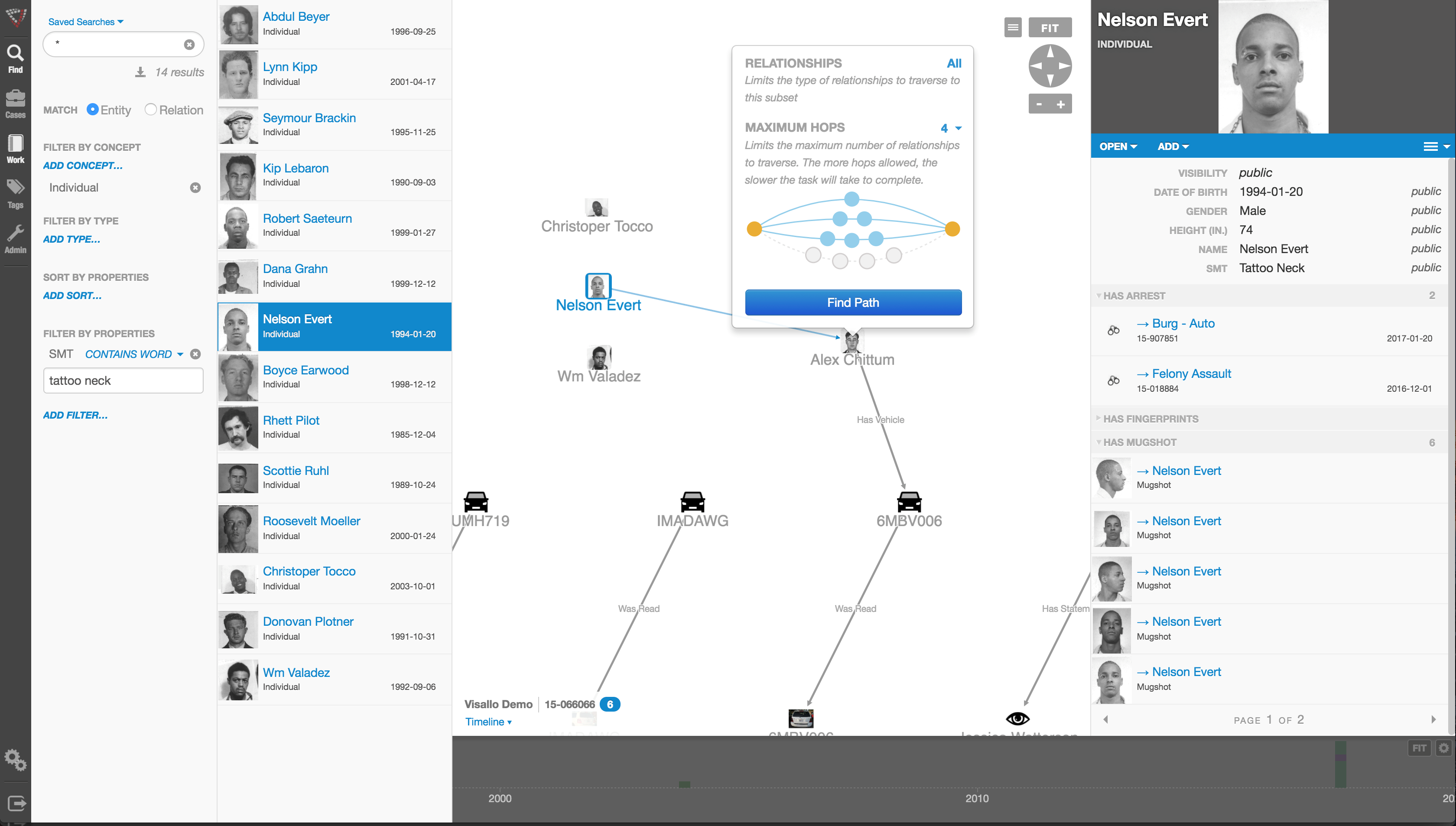
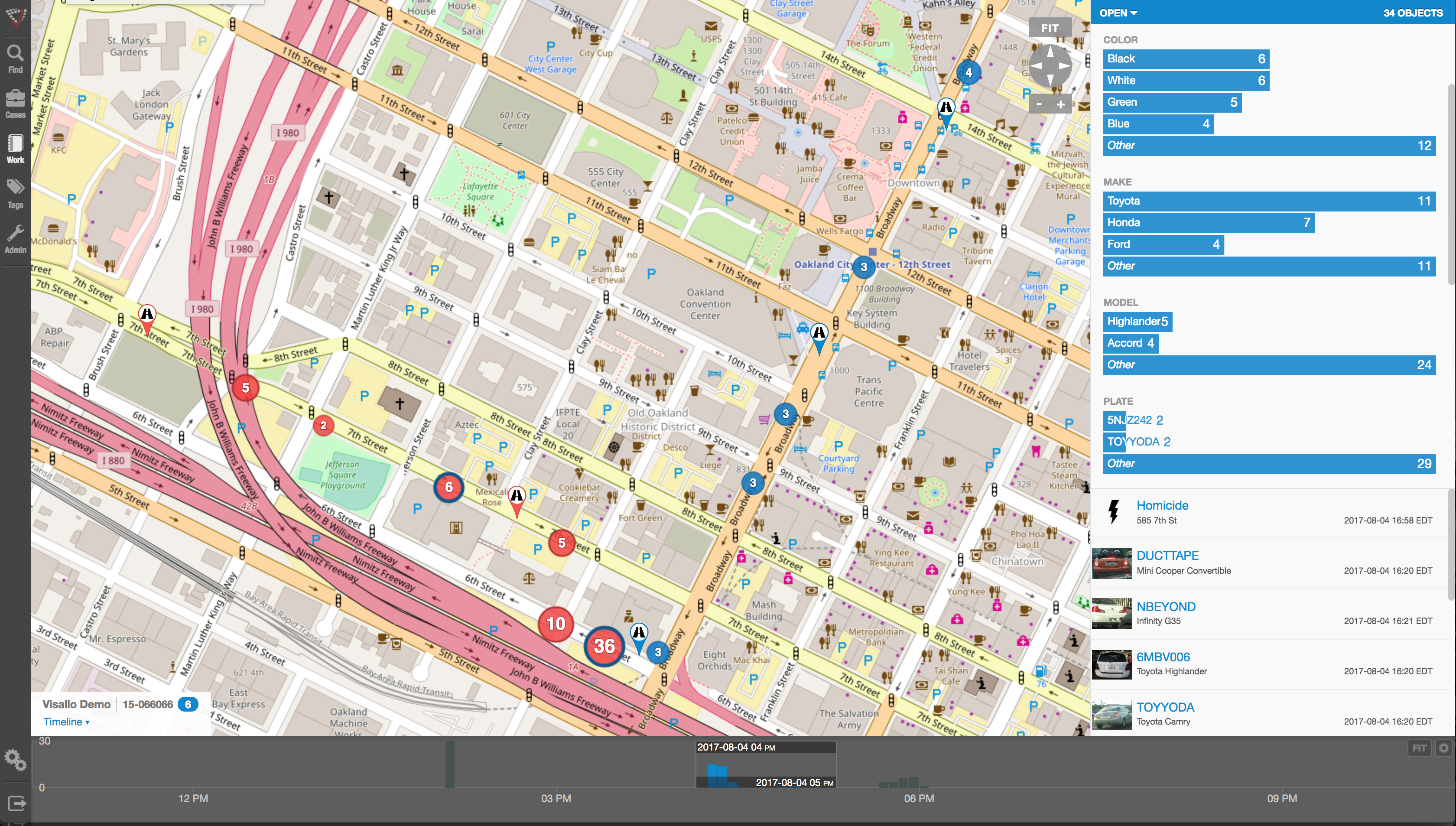
In my technology summary, I termed this area Investigation Management & Adjudication (IMA). IMA is the most critical connection between technology and humans within an enterprise fraud management ecosystem. Incorporating key elements of enterprise case management, collaboration, link visualization, information dissemination and knowledge discovery, this layer of functionality is designed to uncover insights which aid in investigating complex incidents. The result ought to be actionable visualization of critical entities, and documented results for potential litigation and regulatory compliance.
IBM i2 has long been considered a thought and market leader in this segment – deservedly or not. Palantir Technologies plays in this area as well. Perhaps no company is more in tune with this market, though, than Visallo with their leading investigation analytics platform. Each platform clearly adds value to investigation case management solutions by providing powerful, emerging functionalities that allow easy and intuitive consumption of data in any form. For investigators, the more data – and the easier that data is to consume – the better.
“Users want actionable intelligence, not endless queries.”
What makes for good IMA? A few things, actually. First among them is the technology’s ability to adapt to the way human beings think and act. Users want actionable intelligence, not endless queries. IMA tools, therefore, ought to interact with the investigator in a consultative way that a fellow investigator would. “Hey, have you thought about this, Mr. Investigator?” and “Maybe you should look at that.”
Second, IMA ought to have context. Technologies that simply point to two entities and say, ‘Hey these things look linked‘ are great but leave all of the thinking up to Mr. Investigator. The IMA tools that I like have contextual values associated to those links. ‘Hey, these things look linked AND here’s why that’s important’. Big difference.
Third, IMA should bring the investigations to closure. There are a lot of data mining tools out there that allow querying with case management. How, though, does the investigator get to the point where an investigation is solved and prosecutable? Once again, the most functional IMA products act the way humans do. They package up the results of the investigation in an easy-to-comprehend document that can be shared internally or with police. No loose ends.
“Every investigation ends with an investigator.”
Predictive analytics, big data, and real-time alert scoring are the current industry buzzwords. They should be. They’re important. At the end of the day, however, every investigation ends with an investigator. Putting the right tools in their hands is often the difference between success and failure in an entire enterprise investigation system.
That’s precisely what Crime Tech Solutions, LLC does. Please take a moment to look us over.
Part Two of this series is now available HERE.
Lottery Fraud – How lucky can you get?
Posted by Douglas Wood, Editor.
Two weeks ago, I wrote in this space about some interesting experiences I’d had working through Workers Compensation Premium Fraud at a government run program. This week, I received a fraud alert about a retailer being banned from ever selling lottery tickets, and it reminded me of a great exercise I underwent with a government run Lottery corporation several years ago.
Lottery retailer fraud is simple and widespread. NBC Dateline ran a two hour episode several years ago, outlining the problem and going undercover to catch some bad guys in action.
In a nutshell, there are many unscrupulous retailers who outright lie to patrons when asked to check their numbers. Joe the customer hands the ticket over to the clerk and asks her to see if it’s a winner. She scans the barcode and says “Sorry, Joe… you didn’t win“. Then, as Joe heads out the door, she picks the ticket up from the trash bin knowing full well that it’s a big winner. Here’s a real life example.
How bad is the problem? According to Dateline NBC, a Philadelphia retailer cashed eighteen lottery tickets in three months for a total of $45,000. In New Jersey, a retailer cashed 105 lottery tickets for more than $236,000. In Illinois, it found one store where four employees and five of their relatives cashed a total of 556 winning tickets, for more than $1,600,000. In California, lottery investigators were seeing the same thing. In fact, in 2007, the five most frequent winners in California were retailers. One store owner in Los Angeles allegedly cashed 121 tickets for more than $160,000.
As a result of shrinking public trust and outrage, many lottery corporations have taken to more tightly scrutinize ‘winning’ ticket claims from lottery retailers. What, though, if the lottery clerk has her husband cash the ticket? Or her next door neighbor? How can you scrutinize large winning ticket claims without grinding the process to a halt?
That’s precisely where my customer was when they called me.
As with any fraud prevention program, the availability of data was of utmost importance as we scoped out the technology solution. The lottery corporation obviously knew who their retailers were (XYZ Groceries, ABC Petroleum, etc) but how did that help point to a specific Suzie Employee within that retailer? After all, companies weren’t cashing in winning tickets. People were.
Well, we helped them realize that they had employee names as a result of the mandatory training they offered retailers for handling sales of lottery tickets. Each employee of a retailer was required to take a brief online course for certification purposes, and entered some of their personal data (name, date of birth) in order to begin the training.
That got us through step one – the employees. In order to get to the next level of culprit (the family or neighbors of employees), we incorporated publicly available data into the mix.
Through a defined process of business discovery and problem resolution, we designed a process where individuals redeeming winning tickets above a certain value would be compared to the data of retail employees. If it was determined that a winner closely resembled a retail employee, an alert was automatically generated for investigators.
If a winner was determined to be closely acquainted to a retail employee via relationship-detection technology and public data, an alert was again generated. The specifics of how relationships were determined and analyzed won’t be disclosed for obvious reasons, but one example would be a shared address or telephone number.
This particularly lottery corporation was fortunate that they had a mechanism by which to collect employee data. In meeting with dozens of other Lotteries in the years since, I’ve learned that not enough of them have a similar process in place. Unfortunately, without that initial data set, it’s more difficult to detect this type of fraud.
In the case of my client, however, they began immediately seeing benefits in the new process and several fraudulent retailers were exposed. It was some very interesting work, and a cool exercise in problem solving for complex fraud.
Posted by Douglas G. Wood. Check out my site at www.crimetechsolutions.com
SEC taking stock of analytics (and a cool use case for stock exchanges)
 Posted by Douglas Wood, Editor.
Posted by Douglas Wood, Editor.
I read with interest today an article about the SEC’s use of analytics in the ongoing fight against financial crimes. The link to that article is below. It reminded me of some work I once did with a major stock exchange around insider trading.
As a passionate anti-fraud technologist, I was thrilled with the challenge of helping the stock exchange better recognize cases of illegal insider trading. The results of the work we did was pretty cool.
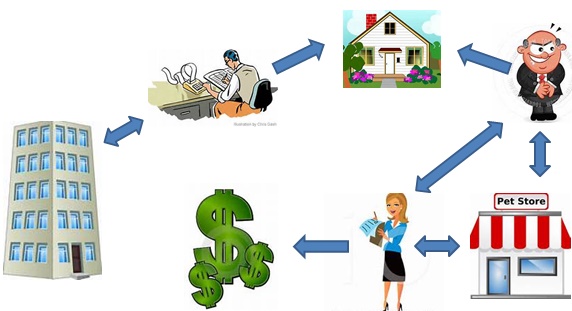
The stock exchange – as do all exchanges – had a great deal of data at their disposal. They knew, for example, the names of each and every ‘insider’ within every company listed on their exchange. Insiders include senior executives, board members, legal counsel, auditors, and so on. Basically, everyone who knew – or ought to have known – about an upcoming event that would likely cause a significant change in stock price.
They also knew, of course, the identity of investors who traded profitably prior to the public release of that information. The problem was exposing the hidden relationships that might exist between Insiders and investors.
Here is an actual example… Joe Blow was an associate partner at the independent accounting firm responsible for auditing the quarterly financial results of publicly traded Company A. By definition, Joe is an insider. He knows Company A’s financials. Jane Doe dumped her entire position in Company A mere days ahead of what turned out to be very poor results. The stock plummeted, and Jane was saved from significant losses. She was seemingly a complete outsider. So, did she somehow know Joe Blow (or any other insider)? Or was she just one lucky gal.
Using link analysis, crime mapping, and behavioral analytics, we set about the challenge of finding out. Here’s what the analytics exposed:
Joe Blow, the insider by way of being employed at Company A’s auditing firm, shared an address with… oh, let’s call him “Rich Quick”. Rich held no positions with Company A whatsoever. He did, however, own a pet food store with a lovely young lady. Can you guess her name? Yep.. Jane Doe. So, the analytics exposed that Company A had an insider relationship with Joe Blow. Joe lived with Rich Quick. Rich owned a business with Jane Doe. Coincidence? Not likely.
Without the ability to draw out hidden links between individuals and organizations, this case may never have been discovered. It’s like Six Degrees of Kevin Bacon, only with much higher stakes. All of the suspects were investigated and prosecuted.
(Note: All the names in this example are fictitious, but the case is not. If your name happens to be Jane Doe, Joe Blow, Rich Quick… or if you work for an organization called Company A, rest assured that I’m not talking about you.)
Here is the link to the SEC article. http://fcw.com/articles/2013/09/18/sec-taps-analytics-to-predict-risk.aspx?s=fcwdaily_190913 .
Financial Crimes and Technology
Posted by Douglas Wood, Editor.
In the midst of preparing for a presentation last week, I entered the term “financial crimes” into my internet search engine. I’ve probably done this same search a hundred times, but seemingly never took notice of the staggering number of results. Over two million of them!
Among those results are a stunning number of definitions, news reports, and general articles. But with so many links to seemingly unconnected terms such as check fraud, credit card fraud, medical fraud, insider trading, bank fraud, health care fraud, tax evasion, bribery, identity theft, counterfeiting, and money laundering – it must appear to the uninitiated that an understanding of ‘financial crimes’ requires an Einstein-like intelligence pedigree.
To those involved in the daily prevention / detection / and investigation of financial crimes, however, the term can be effectively boiled down to:
1) Intentional deception made for personal gain, and
2) The illegal process of concealing the source of those gains.
Everything else – all that other noise – simply falls underneath that definition, and only a cohesive combination of human intelligence and technology can take a bite out of those crimes.
Of course, most companies that are targets of these crimes invest heavily in different forms of technology for enterprise fraud management and anti-money laundering systems. There are dozens of vendors in this market with varying levels of functionality and service offerings.
The problem with too many of those offerings, however, is that they do not account for organizational truths such as functional (and data) silos, data quality issues, changing criminal tactics, human limitations, and big data.
A complete enterprise solution for financial crimes management must include automated processes for:
Customer Onboarding – Knowing the customer is the first step an organization can take to prevent financial crimes. A holistic view of an entity – customers, partners, employees – provides a very clear view of what is already known about the entity including their past interactions and relationships with other entities.
Flexible Rules-Based Alert Detection – A robust rules-based alert detection process must provide out-of-box functionality for the types of crimes outlined at the beginning of this article. At the same time, it should be flexible enough for an organization to modify or create rules as criminal activities evolve.
Predictive Analytics – Expected by analysts to become a 5.25B industry by 2018, predictive analytics ensures that big data is scrutinized and correlated with present and past historical trends. Predictive analytics utilizes a variety of statistics and modeling techniques and also uses machine information, data mining, and Business Intelligence (BI) tools to make predictions about the future behaviors including risk and fraud.
Social Network Analysis – Also known as Fraud Network Analysis, this emerging technology helps organizations detect and prevent fraud by going beyond rules and predictive analytics to analyze all related activities and relationships within a network. Knowing about shared telephone numbers, addresses or employment histories allows companies to effectively ‘cluster’ groups of suspected financial crime perpetrators. The key here, however, is context. Many technologies can build these networks and clusters for review, but precious few can provide the key “what does this mean” element that business users require.
Investigation Management and Adjudication – Incorporating key elements of enterprise case management, collaboration, link visualization, information dissemination and knowledge discovery, this layer of functionality is designed to uncover insights which aid in investigating complex incidents. The result ought to be actionable visualization of critical entities, and documented results for potential litigation and regulatory compliance.
Anti-Money Laundering (AML) and Regulatory Compliance – With record fines being assessed to financial institutions globally, AML compliance is very clearly a major requirement within a financial crimes management solution. The oversight requirements grow almost daily, but at a minimum include out of box functionality for suspicious activity monitoring, regulatory reporting, watch list filtering, customer due diligence, Currency Transaction Report (CTR) processing, and the Foreign Account Tax Compliance Act (FATCA) compliance.
Now, there are clearly many more dynamics than can be summarized here but hopefully the point is made. The only way that organizations can continue to drive fraud and money laundering out is via a happy marriage between skilled financial crimes professionals and the flexible/adaptable technology that empowers them.
Posted by Douglas G. Wood. Click on ABOUT for more information.