Posted by Douglas Wood.
Posted by Douglas Wood.
Journalist Raj Shekhar had an interesting article in the Times of India this week.
It’s like PreCrime, only four decades early. The “predictive policing” system seen in the Tom Cruise blockbuster Minority Report is now taking shape in Delhi. But instead of the three slime-immersed psychic “Precogs” that system relied on, Delhi Police’s crime prediction will be based on cold, hard data.
Once Enterprise Information Integration Solution or ‘EI2S’—a system that puts petabytes of information from more than a dozen crime databases at police staff’s fingertips—is ready, Delhi Police will be able to implement its ‘Crime Forecast’ plan to predict when and where criminals will strike.
The technology is not as fanciful as it seems at first and is already being tried out in many important cities, including New York, Los Angeles, London and Berlin. Officers associated with the plan say the software will analyze police data for patterns, compare it with other data from jails, courts and other crime-fighting agencies, and alert police to the likely threats. Data will be available not only on the suspects but also their likely victims.
A global tender has been floated for the project and Delhi Police is in talks with various firms for the technology.
According to the article, the system can help pre-empt many situations. For example, a violent clash between two gangs. It can identify individuals who are likely to join gangs or take to crime in an area based on the analyses of their behaviour and network. It can also curb domestic violence by identifying a pattern and predicting the next attack, the article said.
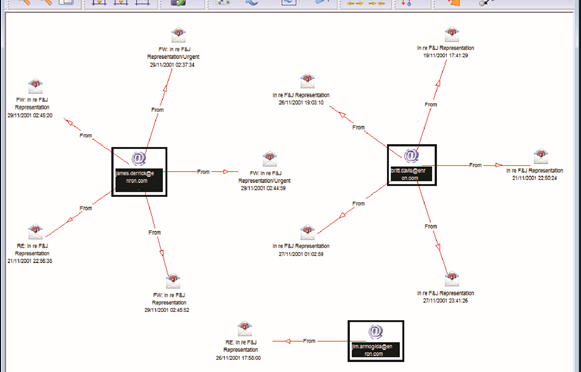
It all boils down to spotting patterns in mountains of data using tremendous computing power. A police document about the plan states that investigators should be able to perform crime series identification, crime trend identification, hot spot analysis and general analysis of criminal profiles. Link analysis will help spot common indicators of a crime by establishing associations and non obvious relationships between entities.
Using neighbourhood analysis, police will be able to understand crime events and the circumstances behind them in a small area as all the crime activity in a neighbourhood will be available for analysis. Criminal cases will be classified into multiple categories to understand what types of crime an area is prone to and the measures needed to curb them. Classification will be done through profiles of victims, suspects, localities and the modus operandi.
Another technique, called proximity analysis, will provide information about criminals, victims, witnesses and other people who are or were within a certain distance of the crime scene. By analyzing demographic and social trends, investigators will be able to understand the changes that have taken place in an area and their impact on criminality.
Network analysis will also be a part of this project to identify the important characteristics and functions of individuals within and outside a network, the network’s strengths and weaknesses and its financial and communication data.
While the system could help fight crime and rid Delhi of its ‘crime capital’ tag, it is bound to raise concerns over privacy and abuse as no predictive system can be foolproof.
Tag Archives: investigation software
Medicaid Fraud – The NAMPI Conference Wrap
Posted by Douglas Wood, Editor.
The National Association for Medicaid Program Integrity (NAMPI) wrapped up its 31st annual conference yesterday (August 12) in New Orleans with the theme “Jazzing up Program Integrity in the Big Easy.” I’m glad that the conference itself was full of cool presentations and networking events, because the temperature outside was Hot Hot Hot! (Note to self: One ‘Hurricane’ at Pat O’Briens on Bourbon Street is enough.)
50 years after President Lyndon Johnson signed into law legislation creating two new national health insurance programs – Medicare and Medicaid – the latter is the largest source of medical and health-related services in the US, providing healthcare to over 68 million Americans with a low income. As the number of enrollees continues to grow, so then does the challenge of maintaining program integrity and fighting the inevitable fraud that hurts us all.
As someone who markets technology solutions in the fight against fraud and crime, I found much of the conference to be right up my alley. As with any conference, much of the agenda was sponsored by vendors of data solutions and technology. Kudos to LexisNexis for sponsoring keynote speaker Elizabeth Smart, former kidnapping victim and advocate for children’s safety. Her story was a powerful way to begin the conference and the packed room was riveted by her story and courage.
NAMPI president John McCormick’s Monday morning remarks were short and sweet and set the tone for what turned out to be an excellent couple of days. In particular, I thought the breakout session on program integrity by the US Government Accountability Office was excellent, as well as a session discussing the facts and myths about Return on Investment. The panel included Illinois Inspector General Brad Hart, Ohio’s Lalita Jambhale, and Oklahoma’s Cindy Roberts. A session called Advanced Analytics was also well-attended and, in my opinion, one of the better forums.
There were several excellent vendor-specific sessions as well, most notably a session entitled “The Next Generation of Medicaid Program Integrity: Where Identity Data, Linking Technology, and Clearing Houses Intersect”, and a look at Missouri’s Medicaid Audit and Compliance programs sponsored by Truven Analytics.
A walk around the Exhibitor floor showed most of the usual suspects – HMS, Truven, SAS, IBM, and others. Each vendor had some uniqueness and most had interesting fraud detection and visual analytics. Still missing from the end-to-end solution equation, however, is an investigative case management system that is purpose designed for Medicaid fraud investigations. Most vendors talked a good talk… few could walk the walk in that area. And what about a biometrics play? Identity assurance is a key element to medical care, why not in program integrity? When will someone fill those voids?
Of note, 21CT was in attendance and had, from what I could see, one of the better overall demonstrations. Their Torch offering continues to impress. Also interesting, Appriss‘ continued push into the industry with their ever-growing database of incarceration records. All vendors performed well, and a full list of those sponsors and exhibitors can be found on the NAMPI Conference website.
Congratulations to NAMPI on an excellent conference, and here’s hoping that the ideas shared continue to put a dent in the billions lost to fraud each year.
Swoop 'n Squat, Army strong, and major case management: This week's Crime Technology headlines:
Posted by Douglas Wood, Editor.
Swoop and Squat…
http://www.propertycasualty360.com/2015/03/09/swoop-squat-beware-of-these-insurance-fraudsters
Army strong analytics…
http://www.military.com/daily-news/2015/03/27/army-improves-systems-testing-to-deliver-more-capability-to-figh.html
Investigative Case Management…
http://www.mvariety.com/cnmi/cnmi-news/local/75212-commonwealth-bureau-of-investigation-has-a-new-building
WorksafeBC introduces new Major Case Management (MCM) protocols…
http://www.workerscompensation.com/compnewsnetwork/workers-comp-blogwire/20898-worksafe-bc-posts-update-on-safety-review-plan.html
The Name Game Fraud
 Posted by Douglas Wood, Editor. Alright everybody, let’s play a game. The name game!
Posted by Douglas Wood, Editor. Alright everybody, let’s play a game. The name game!
“Shirley, Shirley bo Birley. Bonana fanna fo Firley. Fee fy mo Mirley. Shirley!” No, not THAT name game. (Admit it… you used to love singing the “Chuck” version, though.)
The name game I’m referring to is slightly more sinister, and relates to the criminal intent to deceive others for gain by slightly misrepresenting attributes in order to circumvent fraud detection techniques. Pretty much anywhere money, goods, or services are dispensed, folks play the name game.
Utilities, Insurance, Medicaid, retail, FEMA. You name it.
Several years ago, I helped a large online insurance provider determine the extent to which they were offering insurance policies to corporations and individuals with whom they specifically did not want to do business. Here’s what the insurer knew:
- They had standard application questions designed to both determine the insurance quote AND to ensure that they were not doing business with undesirables. These questions included things such as full name, address, telephone number, date of birth, etc… but also questions related to the insured property. “Do you live within a mile of a fire station?”, Does your home have smoke detectors?”, and “Is your house made of matchsticks?”
- On top of the questions, the insurer had a list of entities with whom the knew they did not want to do business for one reason or another. Perhaps Charlie Cheat had some previously questionable claims… he would have been on their list.
In order to circumvent the fraud prevention techniques, of course, the unscrupulous types figured out how to mislead the insurer just enough so that the policy was approved. Once approved, the car would immediately be stolen. The house would immediately burn down, etc.
The most common way by which the fraudsters misled the insurers was a combination of The Name Game and modifying answers until the screening system was fooled. Through a combination of investigative case management and link analysis software, I went back and looked at several months of historical data and found some amazing techniques used by the criminals. Specifically, I found one customer who made 19 separate online applications – each time changing just one attribute or answer slightly – until the policy was issued. Within a week of the policy issue, a claim was made. You can use your imagination to determine if it was a legitimate claim. 😀
This customer, Charlie Cheat (obviously not his real name), first used his real name, address, telephone number, and date of birth… and answered all of the screening questions honestly. Because he did not meet the criteria AND appeared on an internal watch list for having suspicious previous claims, his application was automatically denied. Then he had his wife, Cheri Cheat, complete the application in hopes that the system would see a different name and approve the policy. Thirdly, he modified his name to Charlie Cheat, Chuck E. Cheat, and so on. Still no go. His address went from 123 Fifth Street to 123-A 5th Street. You get the picture.
Then he began to modify answers to the screening questions. All of a sudden, he DID live within a mile of a fire station… and his house was NOT made of matchsticks… and was NOT located next door to a fireworks factory. After almost two dozen attempts, he was finally issued the policy under a slightly revised name, a tweak in his address, and some less-than-truthful answers on the screening page. By investing in powerful investigative case management software with link analysis and fuzzy matching this insurer was able to dramatically decrease the number of policies issued to known fraudsters or otherwise ineligible entities.
Every time a new policy is applied for, the system analyzes the data against previous responses and internal watch lists in real time. In other words, Charlie and Cheri just found it a lot more difficult to rip this insurer off. These same situations occur in other arenas, costing us millions annually in increased taxes and prices. So, what happened to the Cheats after singing the name game?
Let’s just say that after receiving a letter from the insurer, Charlie and Cheri started singing a different tune altogether.
Asking data questions
Posted by Douglas Wood, Editor. http://www.linkedin.com/in/dougwood.
A brief read and good perspective from my friend Chris Westphal of Raytheon. The article is by Anna Forrester of ExecutiveGov.com.
Federal managers should invest in technology that would help them extract insights from data and base their investment decision on the specific problems and information they want to learn and solve, Federal Times reported Friday.
Rutrell Yasin writes that the above managers should follow three steps as they seek to compress the high volume of data their agencies encounter in daily tasks and to derive value from them.
According to Shawn Kingsberry, chief information officer for the Recovery Accountability and Transparency Board, federal managers should first determine the questions they need to ask of data then create a profile for the customer or target audience.
Next, they should locate the data and their sources then correspond with those sources to determine quality of data, the report said. “Managers need to know if the data is in a federal system of records that gives the agency terms of use or is it public data,” writes Yasin.
Finally, they should consider the potential impact of the data, the insights and resulting technology investments on the agency.
Yasin reports that the Recovery Accountability and Transparency Board uses data analytics tools from Microsoft, SAP and SAS and link analysis tools from Palantir Technologies.
According to Chris Westphal, director of analytics technology at Raytheon, organizations should invest in a platform that gathers data from separate sources into a single data repository with analytics tools.
Yasin adds that agencies should also appoint a chief data officer and data scientists or architects to assist the CIO and CISO on these areas.
Perhaps a nice change at NICE Actimize?
Posted by Douglas Wood, Editor. http://www.linkedin.com/in/dougwood
Though not publicly released, news out of NICE Actimize is that long-time CEO Amir Orad is leaving the company effective May 1. Indicative of the ‘what a small world this is’ nature of the financial crimes technology marketplace, former Pegasystems co-founder and head of Americas for BAE Systems Detica, Joe Friscia, will be taking over the helm at that time.
Mr. Orad led NICE Actimize’s product and strategy functions prior to his five year tenure as CEO. During his tenure, he scaled the business size over six-fold. He is also a founding board member at BillGuard the venture backed personal finance analytics and security mobile app company.
Prior to Actimize, Orad was co-founder and CMO of Cyota a cyber security and payment fraud cloud company protecting over 100 million online users, acquired by RSA Security for $145M. Following the acquisition, he was VP Marketing at RSA.
I’ve known both Amir and Joe for several years, and have a tremendous amount of respect for both gentlemen. While it’s sad to see Amir leave the organization, I know that his rather large shoes will be more than adequately filled by Mr. Friscia.
Joe’s background is well-suited to this new position, and all of us here at FightFinancialCrimes wish him well. Joe joined Detica when BAE Systems acquired Norkom Technologies in early 2011, where he served as General Manager and Executive Vice President of the Americas. Joe led the rapid growth of Norkom in the Americas, with direct responsibility for sales, revenue and profit as well as managing multi-discipline teams based in North America. Prior to Norkom, Joe helped start Pegasystems Inc in 1984, a successful Business Process Management software company that went public in 1996.
Best of luck to Amir in his new ventures, and to Joe as he guides Actimize into it’s next phase.
Part Two: Major Investigation Analytics – Big Data and Smart Data
Posted by Douglas Wood, Editor.
As regular readers of this blog know, I spend a great deal of time writing about the use of technology in the fight against crime – financial and otherwise. In Part One of this series, I overviewed the concept of Major Investigation Analytics and Investigative Case Management.
I also overviewed the major providers of this software technology – Palantir Technologies, Case Closed Software, and Visallo. The latter two recently became strategic partners, in fact.
The major case for major case management (pun intended) was driven home at a recent crime and investigation conference in New York. Full Disclosure: I attended the conference for educational purposes as part of my role at Crime Tech Weekly. Throughout the three day conference, speaker after speaker talked about making sense of data. I think if I’d have heard the term ‘big data’ one more time I’d have gone insane. Nevertheless, that was the topic du jour as you can imagine, and the 3 V’s of big data – volume, variety, and velocity – remain a front and center topic for the vendor community serving the investigation market.
According to one report, 96% of everything we do in life – personal or at work – generates data. That statement probably best sums up how big ‘big data’ is. Unfortunately, there was very little discussion about how big data can help investigate major crimes. There was a lot of talk about analytics, for sure, but there was a noticeable lack of ‘meat on the bone’ when it came to major investigation analytics.
Nobody has ever yelled out “Help, I’ve been attacked. Someone call the big data!”. That’s because big data doesn’t, in and by itself, do anything. Once you can move ‘big data’ into ‘smart data’, however, you have an opportunity to investigate and adjudicate crime. To me, smart data (in the context of investigations) is a subset of an investigator’s ability to:
- Quickly triage a threat (or case) using only those bits of data that are most immediately relevant
- Understand the larger scope of the crime through experience and crime analytics, and
- Manage that case through intelligence-led analytics and investigative case management, data sharing, link exploration, text analytics, and so on.
Connecting the dots, as they say. From an investigation perspective, however, connecting dots can be daunting. In the children’s game, there is a defined starting point and a set of rules. We simply need to follow the instructions and the puzzle is solved. Not so in the world of the investigator. The ‘dots’ are not as easy to find. It can be like looking for a needle in a haystack, but the needle is actually broken into pieces and spread across ten haystacks.
Big data brings those haystacks together, but only smart data finds the needles… and therein lies the true value of major investigation analytics.
Major Investigation Analytics – No longer M.I.A. (Part One)
Posted by Douglas Wood, Editor. http://www.linkedin.com/in/dougwood
Long before the terrorist strikes of 9/11 created a massive demand for risk and investigation technologies, there was the case of Paul Bernardo.
Paul Kenneth Bernardo was suspected of more than a dozen brutal sexual assaults in Scarborough, Canada, within the jurisdiction of the Ontario Provincial Police. As his attacks grew in frequency they also grew in brutality, to the point of several murders. Then just as police were closing in the attacks suddenly stopped. That is when the Ontario police knew they had a problem. Because their suspect was not in jail, they knew he had either died or fled to a location outside their jurisdiction to commit his crimes.
The events following Bernardo’s disappearance in Toronto and his eventual capture in St. Catharines, would ultimately lead to an intense 1995 investigation into police practices throughout the Province of Ontario, Canada. The investigation, headed by the late Justice Archie Campbell, showed glaring weaknesses in investigation management and information sharing between police districts.
Campbell studied the court and police documents for four months and then produced a scathing report that documented systemic jurisdictional turf wars among the police forces in Toronto and the surrounding regions investigating a string of nearly 20 brutal rapes in the Scarborough area of Toronto and the murders of two teenaged girls in the St. Catharines area. He concluded that the investigation “was a mess from beginning to end.”
Campbell went on to conclude that there was an “astounding and dangerous lack of co-operation between police forces” and a litany of errors, miscalculations and disputes. Among the Justice’s findings was a key recommendation that an investigative case management system was needed to:
- Record, organize, manage, analyze and follow up all investigative data
- Ensure all relevant information sources are applied to the investigation
- Recognize at an early stage any linked or associated incidents
- “Trigger” alerts to users of commonalities between incidents
- Embody an investigative methodology incorporating standardized procedures
Hundreds of vendors aligned to provide this newly mandated technology, and eventually a vendor was tasked with making it real with the Ontario Major Case Management (MCM) program. With that, a major leap in the evolution of investigation analytics had begun. Today, the market leaders include IBM i2, Case Closed Software, Palantir Technologies, and Visallo.
Recently, the Ottawa Citizen newspaper published an indepth article on the Ontario MCM system. I recommend reading it.
Investigation analytics and major case management
The components of major investigation analytics include: Threat Triage, Crime & Fraud Analytics, and Intelligence-Lead Investigative Case Management. Ontario’s MCM is an innovative approach to solving crimes and dealing with complex incidents using these components. All of Ontario’s police services use this major investigation analytics tool to investigate serious crimes – homicides, sexual assaults and abductions. It combines specialized police training and investigation techniques with specialized software systems. The software manages the vast amounts of information involved in investigations of serious crimes.
Major investigation analytics helps solve major cases by:
- Providing an efficient way to keep track of, sort and analyze huge amounts of information about a crime: notes, witness statements, door-to-door leads, names, locations, vehicles and phone numbers are examples of the types of information police collect
- Streamlining investigations
- Making it possible for police to see connections between cases so they can reduce the risk that serial offenders will avoid being caught
- Preventing crime and reducing the number of potential victims by catching offenders sooner.
See Part Two of this series here.
Part 2: Investigating the Investigations – X Marks the Spot
Posted by Douglas Wood, Editor. http://www.linkedin.com/in/dougwood
Part One of this series is HERE.
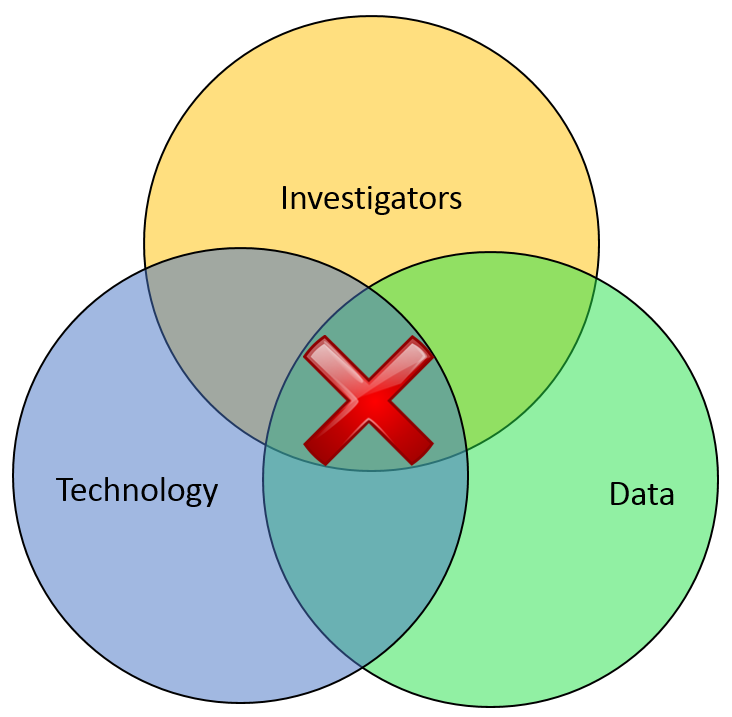
Most of the financial crimes investigators I know live in a world where they dream of moving things from their Inbox to their Outbox. Oh, like everyone else, they also dream about winning the lottery, flying without wings, and being naked in public. But in terms of the important roles they perform within both public and private sectors, there is simply Investigating (Inbox) and Adjudication (Outbox). Getting there requires a unique blend of their own capabilities, the availability of data, and the technology that allows them to operate. In the diagram below, ‘X‘ marks the spot where crimes are moved from the Inbox to the Outbox. Without any of those three components, an investigation becomes exponentially more difficult to conclude.
In part one of this article two weeks ago, I wrote about the Investigation Management & Adjudication (IMA) side of financial crimes investigations. I coined that term to call out what is arguably the most integral component of any enterprise fraud management (EFM) ecosystem. The original EFM overview is here.
“The job is almost unrecognizable to those who once used rotary phones in smoke filled offices…
Twenty years ago, IMA was based primarily upon human eyes. Yes, there were technology tools available such as Wordperfect charts and Lotus 1-2-3 spreadsheets, but ultimately it was the investigator who was tasked with finding interesting connections across an array of data elements including handwritten briefs, telephone bills, lists of suspect information, and discussions with other investigators. The job got done, though. Things moved from the Inbox to the Outbox, arrests were made and prosecutions were successful. Kudos, therefore, to all of the investigators who worked in this environment.
Fast forward to today, and the investigator’s world is dramatically different. The job is the same, of course, but the tools and mass availability of data has made the job almost unrecognizable to those who once used rotary phones in smoke filled offices. Organizations began building enterprise data warehouses designed to provide a single version of the truth. Identity Resolution technology was implemented to help investigators recognize similarities between entities in that data warehouse. And today, powerful new IMA tools are allowing easy ingestion of that data, improved methods for securely sharing across jurisdictions, automated link discovery, non-obvious relationship detection, and interactive visualization tools, and -importantly – packaged e-briefs which can be understood and used by law enforcement, prosecutors, or adjudication experts.
“Without any of these components, everything risks falling to the outhouse…
With all these new technologies, surely the job of the Investigator is becoming easier? Not so fast.
IMA tools – and other EFM tools – do nothing by themselves. The data – big data – does nothing by itself. It just sits there. The best investigators – without tools or data – are rendered impotent. Only the combination of skilled, trained investigators using the best IMA tools to analyze the most useful data available results in moving things from the Inbox to the Outbox. Without any of these components… everything eventually risks falling to the Outhouse.
Kudos again, Mr. and Mrs. Investigator. You’ll always be at the heart of every investigation. Here’s hoping you solve for X every day.
Bananas, Politicians and Navy Blue: Selected Financial Crimes Snapshot 01/02/2013
Posted by Douglas Wood, Editor. http://www.linkedin.com/in/dougwood
Be sure to check out “Investigating the Investigations” Part One and Two! In the meantime, here are this week’s weird headlines:
I can’t believe he tried to slip this one past investigators. Maybe he’ll win on a peel…
http://www.wjla.com/articles/2013/12/maurice-owens-to-appear-in-court-on-metro-banana-peel-fraud-charges-97541.html
A dishonest politician? Now I’ve heard everything!
http://www.wishtv.com/news/indiana/nw-indiana-politician-to-admit-6-wire-fraud-counts
He couldn’t just wait for Black Friday like everyone else?
http://www.hillsdale.net/article/20131202/NEWS/131209942
Navy blue about this one…
http://www.pbs.org/newshour/bb/military/july-dec13/navy_11-27.html