You needn’t be a criminal investigator for particularly long before beginning to feel overwhelmed. Even the most seasoned detectives can be torn between competing priorities such as internal briefings, public scrutiny, phone calls, emails, and the general business that police officers experience every day.
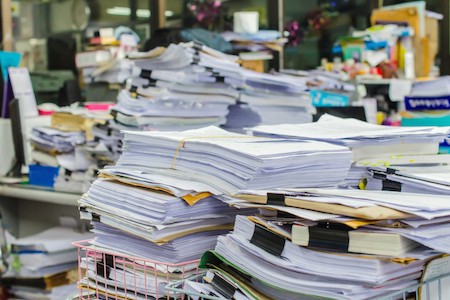
Causing even more grief – and consuming additional time and resources – are the routine tasks of managing investigation case files, documents, interviews, supplemental reports, as well as preparing for DA meetings, court dates, and so on. The manual effort of attempting to locate specific pieces of evidence or paper documents, and then trying to determine how they fit together and disseminating the conclusions is massive.
Managing a criminal investigation becomes more and more difficult each day, given the sheer amount of information generated. Evidence and clues must be garnered from things such as call detail records, body cam video, crime scene photos, arrest records, calls for service data, search warrant results, physical evidence management, and so on… and they all combine to make management of individual cases nearly impossible without the appropriate resources
In an era where senior law enforcement officials are being asked to do ‘more’ with ‘less’, however, those resources can rarely come by way of additional staff. Instead, there are technology solutions, thankfully, that ease the pain that lies in the process of managing criminal investigations.
Investigation Case Management Software (ICMS) such as Case Closed Software provides investigation units with a solution that reduces the paper chase, keeps everything in order, and helps investigators close more cases, more quickly. Case Closed is also available via the cloud with Case Closed Cloud.
From a resource utilization perspective, effective ICMS automates the time-consuming tasks of:
- Storing and retrieving documents such as witness statements, complaints, and supplemental reports
- Locating and managing important audio and video files
- Tracking physical evidence
- Effectively communicating with counterparts
- Keeping up with assigned tasks
- Managing incoming tips and leads
- Developing and understanding connections across incidents and cases
- And much, much more.
From a productivity perspective, the benefits are also wide and varied:
- ICMS saves everything in real time. Detectives never have to worry about losing important documents.
- Allows case data to be entered anywhere – in the office, in the field, or at home.
- Makes everything searchable. People. Places. Things… everything is cross-indexed and easily ‘findable’.
- Provides real-time alerts to notify agents when and if information matches something already in the system.
- Generates standard reports with a few keystrokes based on information in the system.
- Easy preparation for internal status update meetings.
- Allows investigators to share case files internally – or externally to the DA.
- Etcetera, etcetera, etcetera!
Many agencies are still operating investigations on paper files or antiquated, unfriendly systems because they believe the cost of implementing ICMS is prohibitive. Nothing could be further from the truth. The cost of effective software is now well within reach of the vast majority of law enforcement agencies. More importantly, the benefits far outweigh these costs.
Spend less. Solve more cases. Case Closed Software. Download a free brochure.
 Investigation Case Management refers to the gathering and examination of all the evidence, leads, suspects etc… in a criminal investigation. Traditionally, this has been done with pens and paper and file cabinets, but in the 21st century we now have powerful software to aid investigators in their fight against crime.
Investigation Case Management refers to the gathering and examination of all the evidence, leads, suspects etc… in a criminal investigation. Traditionally, this has been done with pens and paper and file cabinets, but in the 21st century we now have powerful software to aid investigators in their fight against crime.
 According to Jeff Kunkle, President of Visallo, the partnership enhances his company’s suite of easy-to-use, web-based data visualization tools for investigative link analysis, data discovery, crime analytics and geospatial analysis with Crime Tech Solutions’ powerful and flexible
According to Jeff Kunkle, President of Visallo, the partnership enhances his company’s suite of easy-to-use, web-based data visualization tools for investigative link analysis, data discovery, crime analytics and geospatial analysis with Crime Tech Solutions’ powerful and flexible 

 Posted by Tyler Wood, Director of Operations at Case Closed Software.
Posted by Tyler Wood, Director of Operations at Case Closed Software.

 ‘Correctly’ is the operative term, of course. The ability to turn these large data stores into actionable investigation intelligence requires more than a simple data warehouse or data mining tool, and for the most part police departments recognize this need. They understand that their data holds the key to understanding the hidden connections between people, places, and things – the lynchpin of any successful investigation.
‘Correctly’ is the operative term, of course. The ability to turn these large data stores into actionable investigation intelligence requires more than a simple data warehouse or data mining tool, and for the most part police departments recognize this need. They understand that their data holds the key to understanding the hidden connections between people, places, and things – the lynchpin of any successful investigation. Big Data Investigation Analytics – such as those provided by Virginia based
Big Data Investigation Analytics – such as those provided by Virginia based  When paired with the robust investigative case management and criminal intelligence systems available from
When paired with the robust investigative case management and criminal intelligence systems available from 
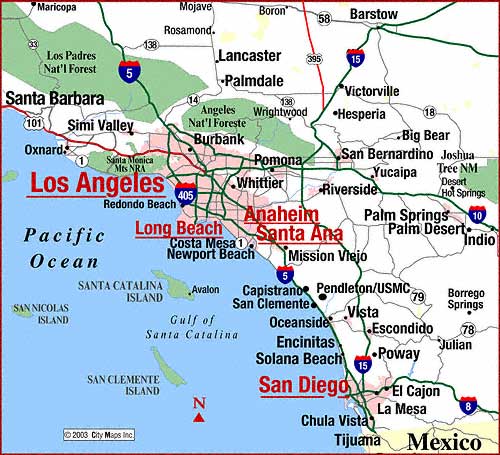 Crime Tech Solutions, LLC – a fast growing, vibrant software company based in Leander, TX today announced that a large, coastal city in California has selected them to provide sophisticated
Crime Tech Solutions, LLC – a fast growing, vibrant software company based in Leander, TX today announced that a large, coastal city in California has selected them to provide sophisticated 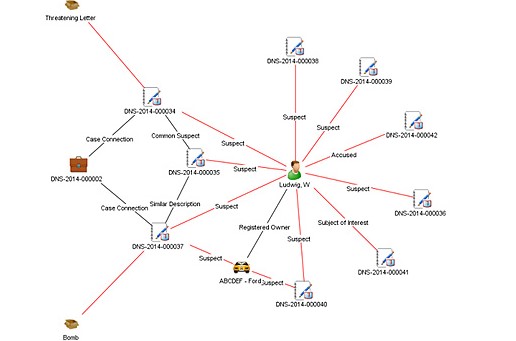
 Government decisions and policies are heavily influenced by the insights provided by the criminal intelligence analyst, and police investigations use the intelligence in support of their missions. To that end, the main functions of criminal intelligence analysts include:
Government decisions and policies are heavily influenced by the insights provided by the criminal intelligence analyst, and police investigations use the intelligence in support of their missions. To that end, the main functions of criminal intelligence analysts include:  B. Strategic Criminal Intelligence
B. Strategic Criminal Intelligence D. Abuse and Misuse of Criminal Intelligence
D. Abuse and Misuse of Criminal Intelligence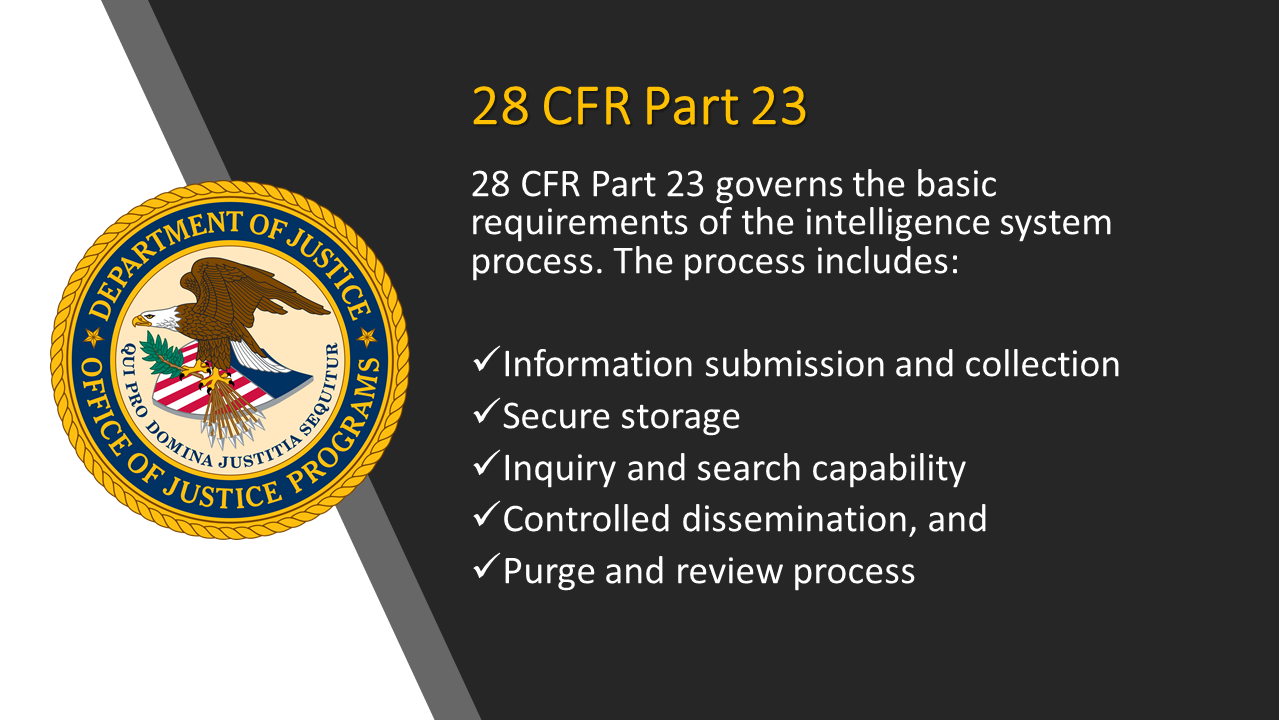 Specifically,
Specifically, 