Posted by Douglas Wood, Editor. http://www.linkedin.com/in/dougwood
Part One of this series is HERE.
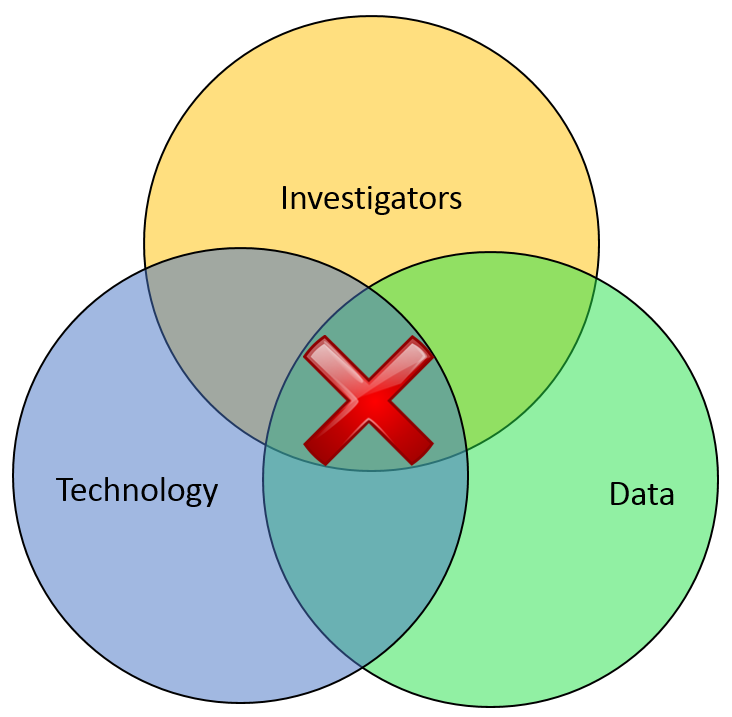
Most of the financial crimes investigators I know live in a world where they dream of moving things from their Inbox to their Outbox. Oh, like everyone else, they also dream about winning the lottery, flying without wings, and being naked in public. But in terms of the important roles they perform within both public and private sectors, there is simply Investigating (Inbox) and Adjudication (Outbox). Getting there requires a unique blend of their own capabilities, the availability of data, and the technology that allows them to operate. In the diagram below, ‘X‘ marks the spot where crimes are moved from the Inbox to the Outbox. Without any of those three components, an investigation becomes exponentially more difficult to conclude.
In part one of this article two weeks ago, I wrote about the Investigation Management & Adjudication (IMA) side of financial crimes investigations. I coined that term to call out what is arguably the most integral component of any enterprise fraud management (EFM) ecosystem. The original EFM overview is here.
“The job is almost unrecognizable to those who once used rotary phones in smoke filled offices…
Twenty years ago, IMA was based primarily upon human eyes. Yes, there were technology tools available such as Wordperfect charts and Lotus 1-2-3 spreadsheets, but ultimately it was the investigator who was tasked with finding interesting connections across an array of data elements including handwritten briefs, telephone bills, lists of suspect information, and discussions with other investigators. The job got done, though. Things moved from the Inbox to the Outbox, arrests were made and prosecutions were successful. Kudos, therefore, to all of the investigators who worked in this environment.
Fast forward to today, and the investigator’s world is dramatically different. The job is the same, of course, but the tools and mass availability of data has made the job almost unrecognizable to those who once used rotary phones in smoke filled offices. Organizations began building enterprise data warehouses designed to provide a single version of the truth. Identity Resolution technology was implemented to help investigators recognize similarities between entities in that data warehouse. And today, powerful new IMA tools are allowing easy ingestion of that data, improved methods for securely sharing across jurisdictions, automated link discovery, non-obvious relationship detection, and interactive visualization tools, and -importantly – packaged e-briefs which can be understood and used by law enforcement, prosecutors, or adjudication experts.
“Without any of these components, everything risks falling to the outhouse…
With all these new technologies, surely the job of the Investigator is becoming easier? Not so fast.
IMA tools – and other EFM tools – do nothing by themselves. The data – big data – does nothing by itself. It just sits there. The best investigators – without tools or data – are rendered impotent. Only the combination of skilled, trained investigators using the best IMA tools to analyze the most useful data available results in moving things from the Inbox to the Outbox. Without any of these components… everything eventually risks falling to the Outhouse.
Kudos again, Mr. and Mrs. Investigator. You’ll always be at the heart of every investigation. Here’s hoping you solve for X every day.